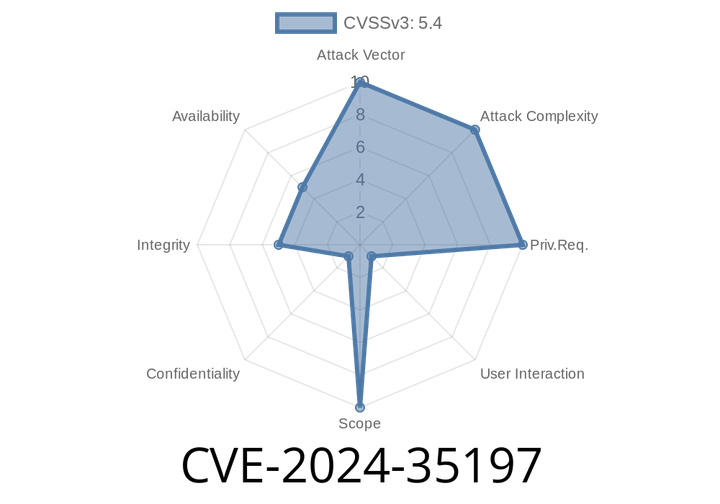
CVE-2024-35197 - How Cloning Git Repositories on Windows with gitoxide May Be Dangerous
In May 2024, a security flaw was found in gitoxide, which is a blazing-fast, pure Rust implementation of Git. This vulnerability, tracked as CVE-2024-35197, mainly
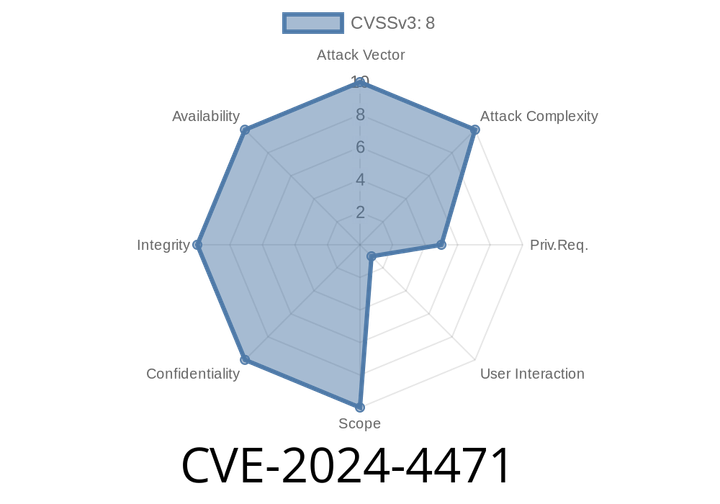
CVE-2024-4471 - PHP Object Injection Vulnerability in “The 140+ Widgets | Best Addons For Elementor – FREE” WordPress Plugin
In June 2024, a serious security issue (CVE-2024-4471) was uncovered in the popular WordPress plugin The 140+ Widgets | Best Addons For Elementor – FREE. This plugin,
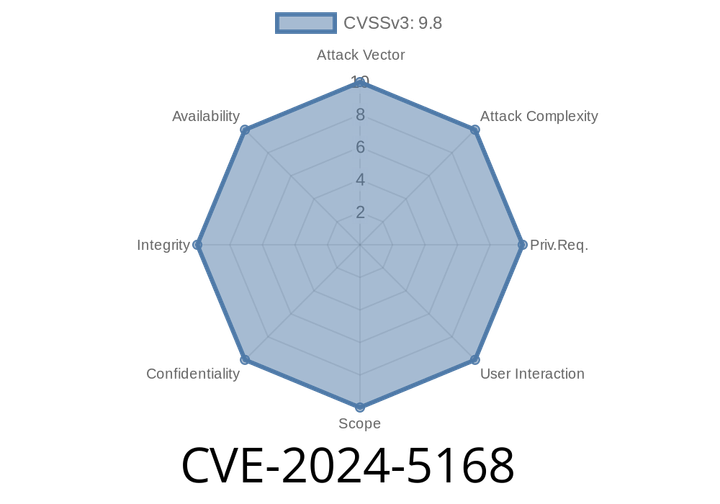
CVE-2024-5168 - How Hackers Bypass Authentication on Prodys Quantum Audio Codec (Exclusive, Simple Explanation & Code)
A new critical security vulnerability — CVE-2024-5168 — has been discovered affecting Prodys’ Quantum Audio Codec, specifically all firmware versions up to and including 2.3.4t.
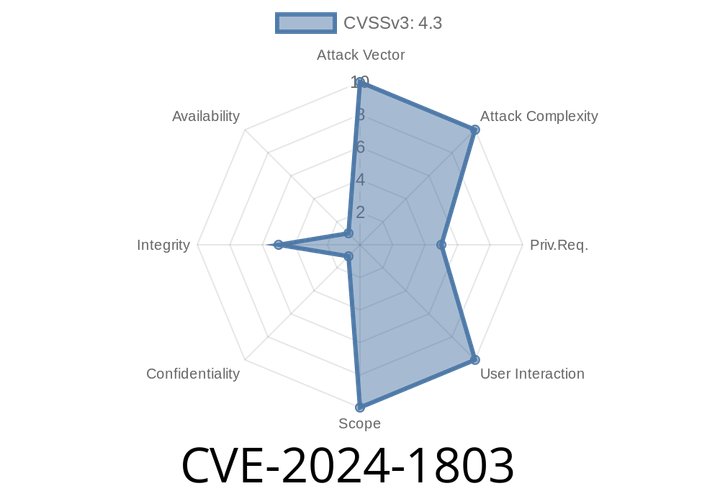
CVE-2024-1803 - Unpacking the WordPress EmbedPress PDF Block Vulnerability (Up to v3.9.12)
WordPress plugins make building and managing websites easier, but sometimes they also bring in security problems—especially when they don’t check who’s allowed
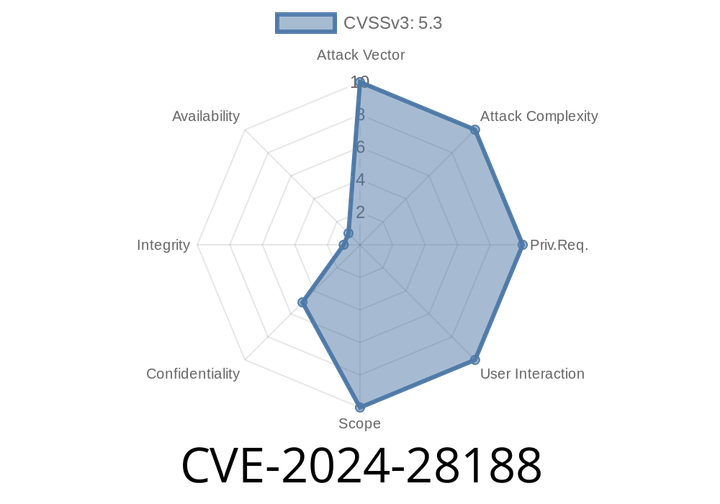
CVE-2024-28188 - Jupyter Scheduler’s Conda Environment Exposure Vulnerability Explained
If you use Jupyter Scheduler for handling tasks in your JupyterLab environment, it’s important to pay attention to a recent security issue: CVE-2024-28188. This
Episode
00:00:00
00:00:00