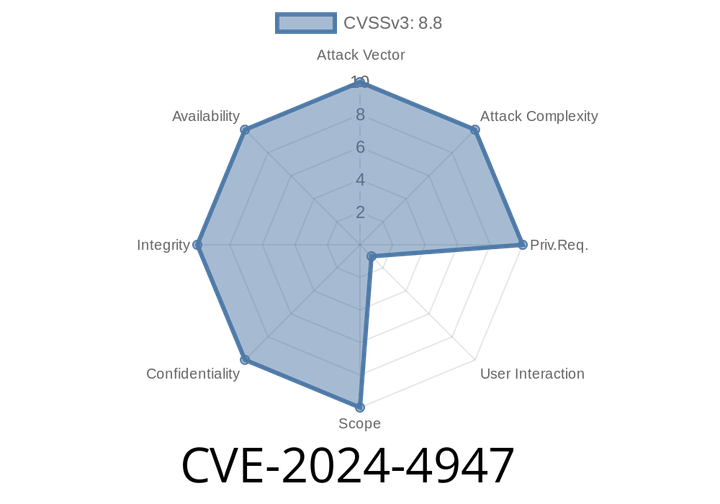
CVE-2024-4947 - Breaking Down a V8 Type Confusion Bug in Google Chrome
In May 2024, security researchers identified a significant vulnerability—CVE-2024-4947—affecting Google Chrome’s JavaScript engine, V8. This bug, present in Chrome versions before 125.
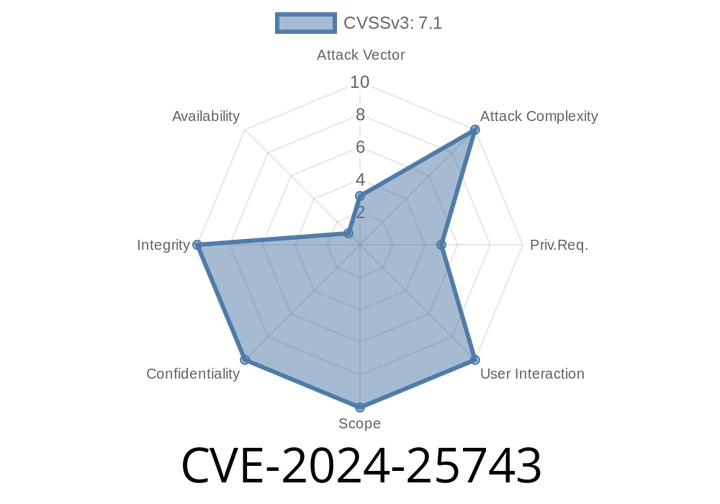
CVE-2024-25743 - Linux Kernel AMD SEV-SNP/SEV-ES Virtual Interrupt Injection Vulnerability Explained
In early 2024, a serious vulnerability—CVE-2024-25743—was discovered in the Linux kernel up to version 6.9. This flaw allows an untrusted hypervisor to
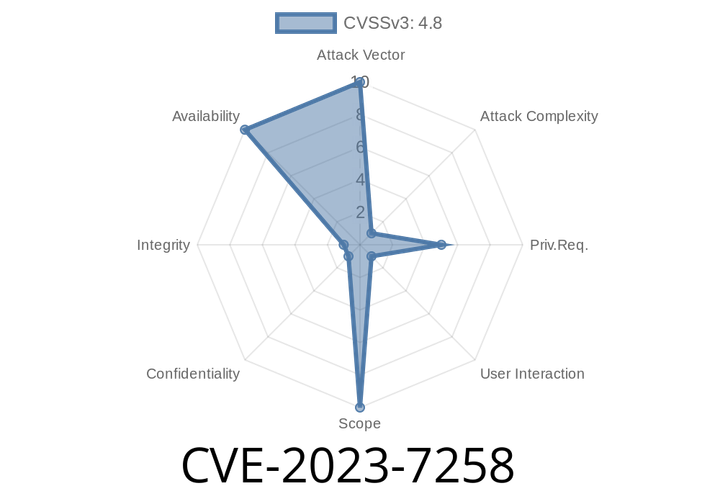
CVE-2023-7258 - Root User Can Crash gVisor Sandbox with Mount Point Reference Counting Bug
---
TL;DR
A bug in how gVisor keeps track of mounted volumes lets a root user crash the sandbox. If they mount and unmount
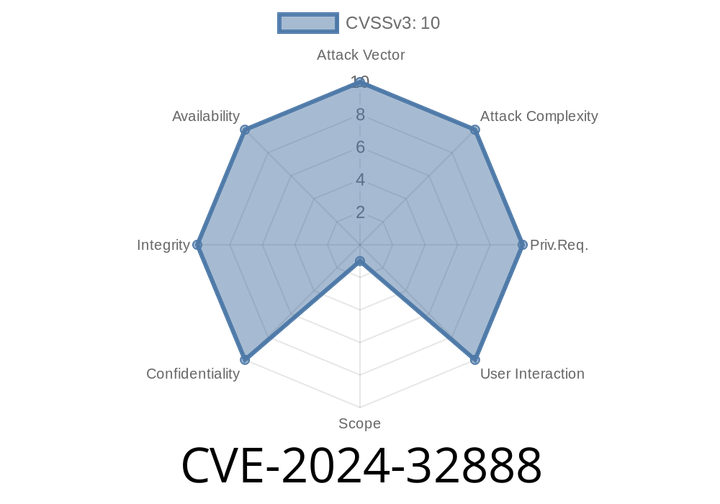
CVE-2024-32888 - Exploiting SQL Injection in Amazon Redshift JDBC Driver (`preferQueryMode=simple`)
In June 2024, a new security vulnerability was disclosed in the Amazon Redshift JDBC Driver, tracked as CVE-2024-32888. This vulnerability allows SQL injection attacks when
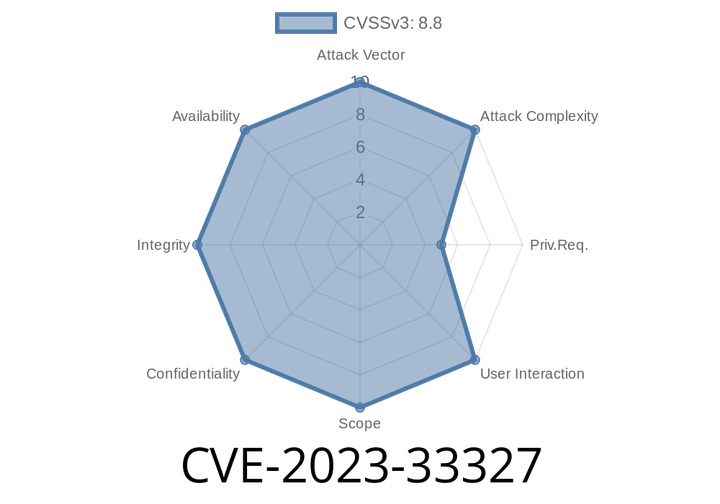
CVE-2023-33327 - How Improper Privilege Management in Leyka Opens Doors for Hackers (Including Exploit Example)
CVE-2023-33327 is an Improper Privilege Management vulnerability in the Leyka plugin, developed by Teplitsa of Social Technologies. Leyka is a popular donation and fundraising solution
Episode
00:00:00
00:00:00