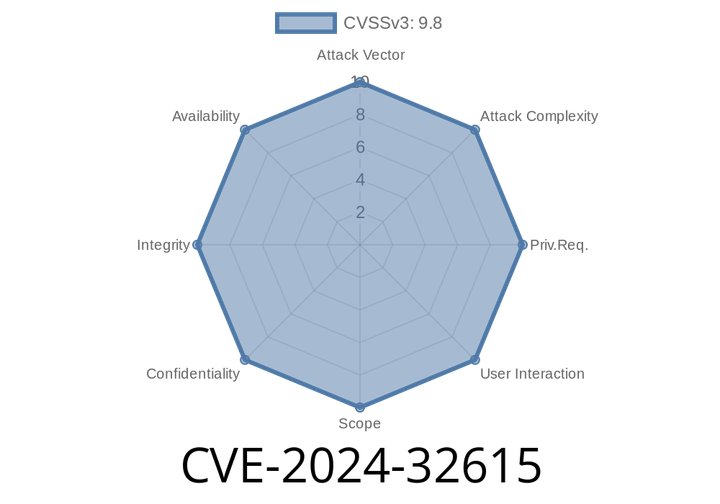
CVE-2024-32615 - Exploiting a Heap-Based Buffer Overflow in HDF5's N-Bit Decompression
A recently discovered vulnerability, CVE-2024-32615, shook confidence in the reliability of HDF5, one of the world’s most popular open file formats and libraries for
CVE-2024-30172 - Bouncy Castle Ed25519 Infinite Loop Exploit Explained (with Code Examples)
*Published June 2024*
Bouncy Castle is a popular set of cryptography libraries in Java and other languages. But even the most trusted security tools sometimes
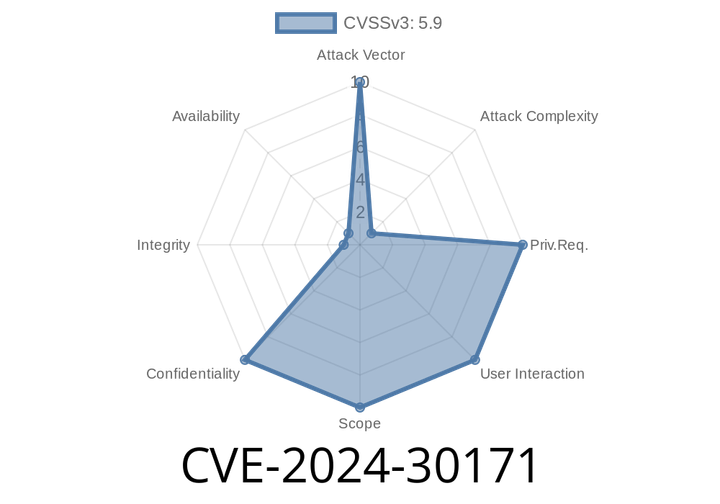
CVE-2024-30171 - Timing Attack Risk in Bouncy Castle’s Java TLS API and JSSE Provider – Explained, Exploited, and Patched
Bouncy Castle is one of the most trusted libraries for cryptographic operations in Java. Used by developers and organizations worldwide, its TLS API and JSSE
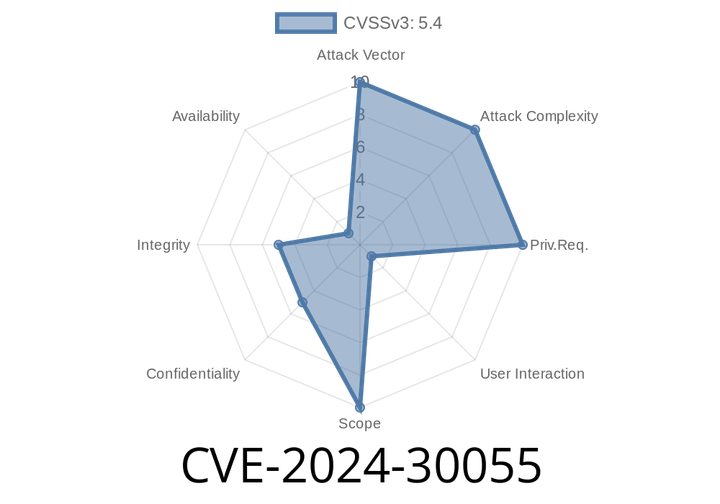
CVE-2024-30055 - Inside the Microsoft Edge (Chromium-based) Spoofing Vulnerability
---
Microsoft Edge is one of the most widely used browsers, especially in workplace environments. It’s fast, secure, and built on Chromium — the same
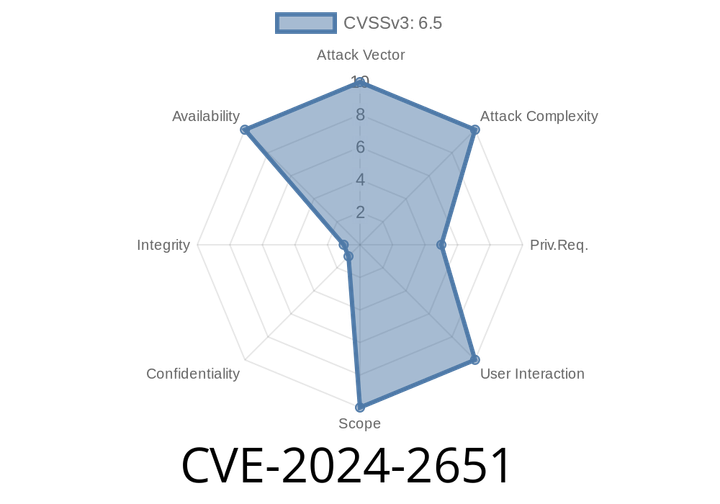
CVE-2024-2651 - Exploiting a GitLab Markdown Denial-of-Service Vulnerability (Exclusive Guide)
A major security flaw, CVE-2024-2651, was discovered in GitLab’s popular CE/EE products. This bug lets attackers crash GitLab by simply using specially crafted
Episode
00:00:00
00:00:00