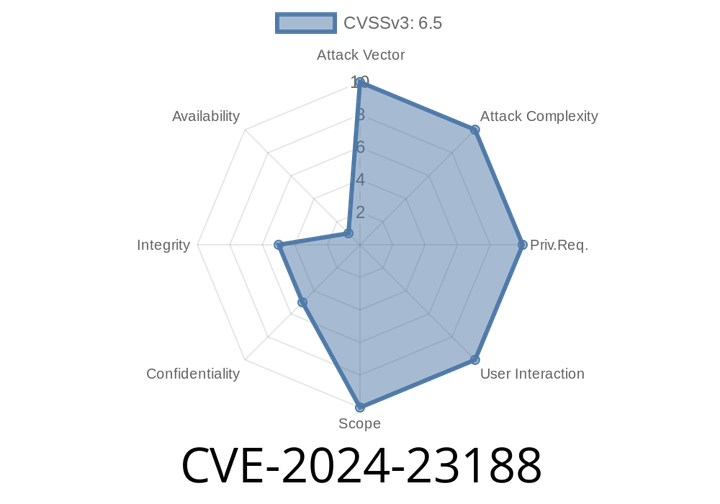
CVE-2024-23188 - How Malicious Email Attachments Can Trigger Script Execution in Your Browser
On June 12, 2024, a new vulnerability was disclosed: CVE-2024-23188. This security issue affects users of certain web-based email platforms. In simple terms, an attacker
CVE-2024-34447 - How Bouncy Castle’s Java APIs Let DNS Poisoning Slip Through — Details, Code, and Exploitation
If you use Java for SSL communication, chances are you've bumped into Bouncy Castle, a popular library for cryptographic functions. But until version
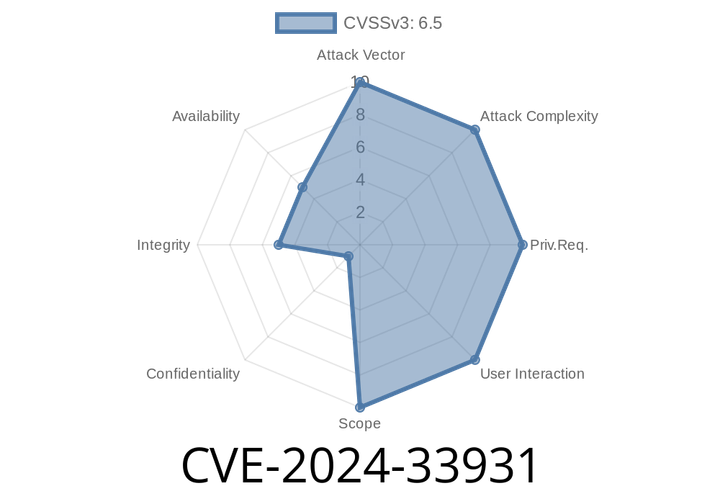
CVE-2024-33931 - Missing Authorization in ilGhera JW Player for WordPress (<= 2.3.3) - Exploit and Analysis
---
WordPress plugins are common targets for attackers, especially when they miss basic security checks. Recently, CVE-2024-33931 was identified in ilGhera JW Player for WordPress
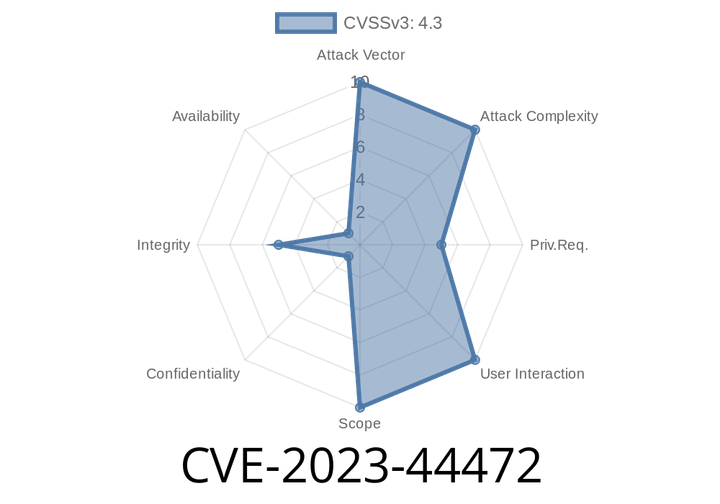
CVE-2023-44472 - How a Missing Authorization Bug Opened Thousands of WordPress Sites to Hackers (Unyson <= 2.7.28)
WordPress is the go-to platform for millions of websites, and it thrives on plugins and themes that add cool new features. But what happens when
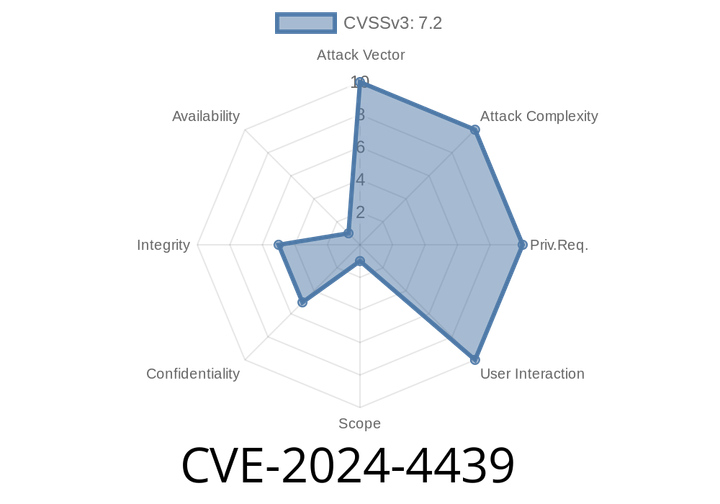
CVE-2024-4439 - Critical Stored XSS in WordPress Core via Avatar Block—Exploit Analysis and Guidance
Published: June 2024
Severity: High
Affected WordPress Versions: Up to 6.5.2
Overview
A new vulnerability tracked as CVE-2024-4439 has rocked the WordPress community.
Episode
00:00:00
00:00:00