In the heart of Linux, many drivers and subsystems interact closely with hardware. One such subsystem is I2C (Inter-Integrated Circuit), a widely-used interface for connecting low-speed devices like sensors, EEPROMs, and clocks to processors and microcontrollers.
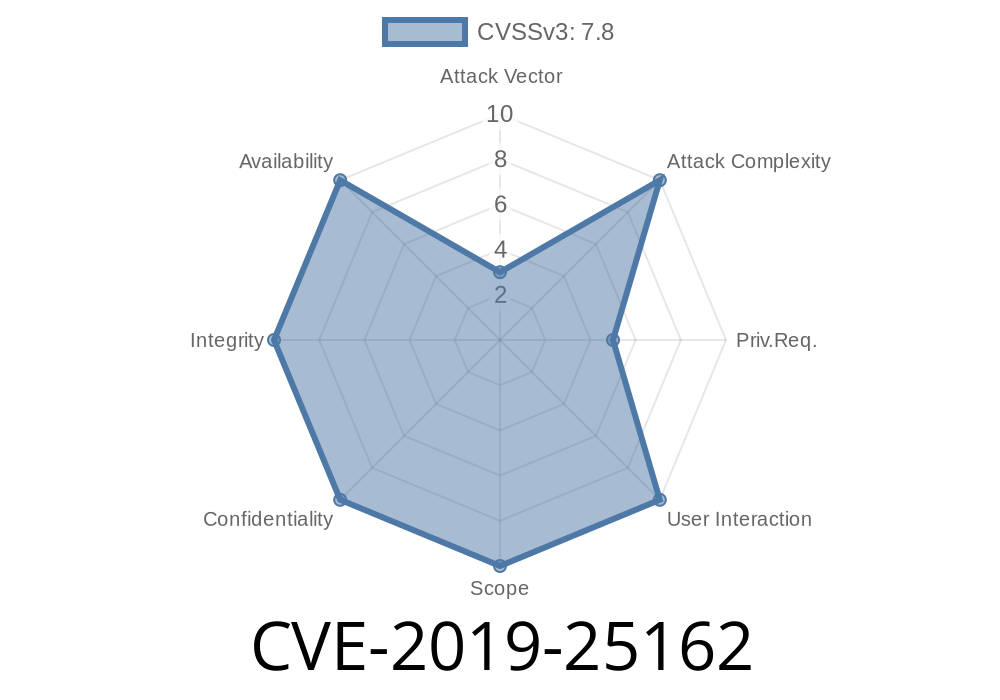
In 2019, security researchers discovered a vulnerability in the Linux kernel's implementation of the I2C subsystem, recorded as CVE-2019-25162. This long-read post explores the details behind this bug, how it can be exploited, and how it was fixed. We’ll keep things simple and guide you through code snippets, the patch, and useful resources for your learning.
What’s CVE-2019-25162 About?
The bug is a classic use-after-free vulnerability. This means the code tries to access memory (or a “structure”) after it’s already been released or “freed.” Specifically, this happened to the adap structure in the I2C subsystem.
What is the adap Structure?
- The adap variable stands for the “adapter” device in the I2C subsystem. It represents a physical or virtual I2C bus.
- Kernel code often uses reference counting and special routines to manage the lifecycle of such objects.
Original Bug
The issue occurred because the code called put_device(&adap->dev) while still potentially using the adap structure just after. This allowed a tricky race condition where other kernel code could reuse or release the same memory, opening up risks for crashes or potential security exploits.
Here’s a simplified version of the buggy code, showing the problem area
struct i2c_adapter *adap = i2c_get_adapter(id);
if (!adap)
return -ENODEV;
do_something_with_adapter(adap);
put_device(&adap->dev); // Frees adap structure
// ... Oops, potentially using adap after it's been freed!
if (adap->something) {
// This can be dangerous! 'adap' memory might be invalid now.
}
The issue is that *put_device* can actually remove the adapter structure from memory if no one else is using it. Any code using adap after this call accesses freed memory, which is undefined behavior and a security risk.
The Fix
The fix is simple in concept: Only free the adap structure after we’re completely done using it. The patch moves the call to put_device down, making sure no code tries to use adap after it might have been freed.
Fixed Code Snippet
struct i2c_adapter *adap = i2c_get_adapter(id);
if (!adap)
return -ENODEV;
do_something_with_adapter(adap);
if (adap->something) { // Now, it's safe to use adap here!
// Do more work safely.
}
/* Release the adapter only at the very end */
put_device(&adap->dev);
> [wsa: added comment to the code, added Fixes tag]
Is This Vulnerable in the Real World?
- If a user or attacker could trigger this code path intentionally (e.g., by repeatedly opening and closing an I2C device or racing multiple operations), they may be able to:
Get a reference to the I2C adapter device (e.g., via user-space interfaces or ioctl calls).
2. Cause kernel code to use the adap structure after it has already been put or freed (perhaps by racing open/close or via buggy drivers).
Real-World Impact
- Local Privilege Escalation: Unlikely but theoretically possible, if code can be executed after the use-after-free.
- Crashes/Denial of Service: More likely; kernel panic can be triggered.
Patch Commit:
i2c: Fix a potential use after free (LKML)
Excerpt from the actual patch message
> "Free the adap structure only after we are done using it. This patch just moves the put_device() down a bit to avoid the use after free."
CVE Entry
Relevant Source Files
- drivers/i2c/i2c-core.c
- Linux source code for I2C core
Conclusion
CVE-2019-25162 is a classic case of how small pointer and memory mistakes can lead to big security holes in low-level systems. Fortunately, with rigorous patching and review, the Linux community moves quickly to keep everyone secure.
References
- Official Patch on LKML
- CVE-2019-25162 NVD Entry
- Linux I2C Documentation
- Linux I2C Code (Elixir Bootlin)
*If you want to learn more about Linux kernel vulnerabilities, follow our blog for regular technical deep-dives.*
Timeline
Published on: 02/26/2024 18:15:07 UTC
Last modified on: 04/17/2024 17:38:07 UTC