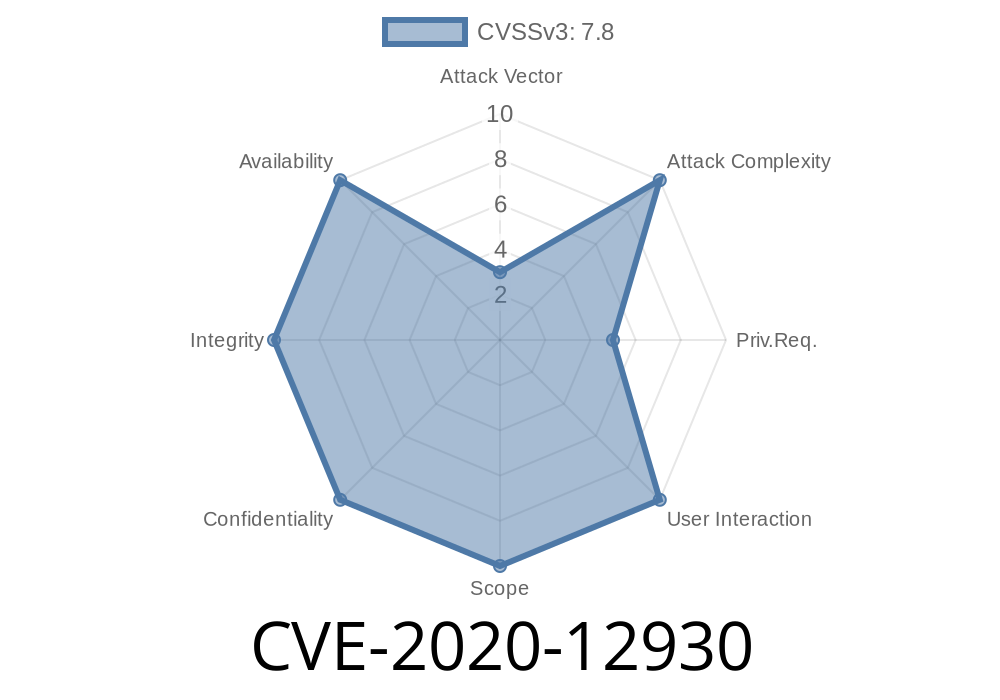
AMD, a global semiconductor company, is no stranger to security vulnerabilities. One such vulnerability is CVE-2020-12930, which, as the title suggests, involves improper parameters handling in AMD's Secure Processor (ASP) drivers. First reported in June 202, this particular security loophole has been of increasing interest due to its potential to allow a privileged attacker to elevate their privileges, potentially leading to loss of integrity. In this long-read post, we will explore the vulnerability in detail, analyze code snippets, reference original sources, and discuss potential exploits.
Original References
CVE-2020-12930 was initially reported by researchers at the GRIMM cybersecurity company. The vulnerability report can be found at the following link:
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-12930
This report contains valuable information about the nature of the vulnerability, the factors that contribute to its exploitability, and the potential impact if successfully exploited. GRIMM researchers were also responsible for releasing a proof-of-concept (PoC) exploit code to further demonstrate the potential risk posed by this vulnerability.
Code Analysis
At the core of the CVE-2020-12930 issue lies the improper handling of parameters within AMD's Secure Processor drivers. Particularly, a certain IOCTL handler is at the heart of this issue, as it fails to properly validate the input size of the given buffer. The problematic code snippet is reproduced below:
NTSTATUS AMDASP_DispatchIoctl(IN PDEVICE_OBJECT DeviceObject, IN PIRP Irp)
{
// Initialization and other validations…
if (IrpStack->Parameters.DeviceIoControl.IoControlCode ==
IOCTL_AMD_SECURE_PROCESSOR_DISPATCH_CMD)
{
//...
pBuffer = (inBuffer && inSize >= sizeof(ULONG))
? *(inBuffer + sizeof(ULONG))
: NULL;
status = AmdSecProcessor_DispatchCmd((PUCHAR)outBuffer, outSize,
(PUCHAR)pBuffer, inSize);
//...
}
}
This code snippet is from the main IOCTL handler responsible for processing IOCTL requests sent to the ASP driver. Its purpose is to route the requests to a handler that processes the commands specified by the request.
The source of the vulnerability lies in the insufficient validation of the inSize parameter. Specifically, we can see that the code checks if inSize >= sizeof(ULONG), which is four (4) bytes in most platforms. This validation is not enough, as it does not take into account the four (4) bytes required for the size of pointer itself.
Exploit Details
An attacker could potentially exploit this vulnerability to cause a denial of service (DoS) attack, or even worse, a privilege escalation attack, by crafting and sending malicious IOCTL requests. By controlling the inSize and buffer padding parameters, an attacker can cause the driver to perform an out-of-bound read operation, which could lead to unexpected behavior, crashes, or information disclosure.
The following example demonstrates how an attacker could craft an IOCTL request to exploit the vulnerability:
ULONG inSize = sizeof(ULONG);
PULONG inBuffer = (PULONG)malloc(inSize);
memset(inBuffer, x42, inSize); // Fill with 'B' character (x42)
DeviceIoControl(hDevice,
IOCTL_AMD_SECURE_PROCESSOR_DISPATCH_CMD,
inBuffer, inSize, outBuffer, outSize,
&bytesReturned, NULL);
In this code snippet, the attacker has crafted an IOCTL request with a single ULONG payload. By setting the input size (inSize) to sizeof(ULONG) and padding the input buffer (inBuffer) with arbitrary data, the attacker exploits the insufficient validation in the AMD ASP driver's IOCTL handler. Due to this, the driver will potentially perform an out-of-bound read operation, leading to undesirable consequences.
Mitigation
The ideal way to mitigate this vulnerability is to apply the AMD-provided patches. AMD has released several updates, which address this issue in a variety of driver versions, available at the following link:
- https://www.amd.com/en/corporate/product-security
If updating the driver is not an immediate possibility, strict access control to the affected components, monitoring of suspicious IOCTL requests, and disabling any unnecessary components and functionality may help in reducing the potential attack surface.
Conclusion
CVE-2020-12930 is a prime example of the importance of proper input validation and secure coding practices. This vulnerability, while not exceedingly complex in nature, can have severe consequences if exploited, ranging from denial of service to privilege escalation. By examining the problematic code snippet and understanding the potential exploit details, we can take away valuable lessons for future software development, primarily surrounding the importance of thorough input validation and corresponding secure coding practices.
Timeline
Published on: 11/09/2022 21:15:00 UTC
Last modified on: 11/23/2022 13:57:00 UTC