Moreover, the hack utility of Asus RT-N12E 2.0.0.39 allows remote attackers to cause a denial of service (DoS) or remote code execution (RCE) via a crafted request, as exploited in the wild in July 2018.
Another critical issue was discovered in Asus RT-N12E 2.0.0.39 software. An input validation flaw was found in the system.asp / start_apply.htm script. If an attacker sends a specially-crafted request to the target system, it could be exploited to crash the web server.
An attacker can exploit the system.asp / start_apply.htm script-based input validation flaw to execute arbitrary code on the victim’s system.
Asus RT-N12E 2.0.0.39 is also vulnerable to cross-site request forgery (CSRF) vulnerability. An attacker can exploit CSRF to change the administrator password of the target system.
In addition, Asus RT-N12E 2.0.0.39 is prone to a stored cross-site scripting (XSS) vulnerability. An attacker can exploit XSS flaw to carry out a web-based privilege escalation.
Another critical issue was discovered in Asus RT-N12E 2.0.0.39 software. An improper input validation flaw was found in the system.asp / start_apply.htm script. If an attacker sends a specially
Sticky Notes – The Black Box of Asus RT-N12E 2.0.0.39
Unlike the Asus RT-N12E 2.0.0.39 utility, which has a black box quality about it and is hard to understand or control, Sticky Notes is a free and easy-to-use application that can be downloaded from the Google Play Store.
The sticky notes application was developed by Sticky Notes Inc., a company based in California and founded in 2012 by Justin Marsh, who currently serves as CEO of the company.
While Sticky Notes was initially built for personal use, it has since been used by corporations and government organizations such as T-Mobile and CERN (European Organisation for Nuclear Research) because of its simplicity and powerful features.
Asus Router Model Discovered to Be Affected
Upon the discovery of these critical vulnerabilities, Asus quickly updated their software to patch them.
In a blog post by Asus, they announced that they have released security updates to address these vulnerabilities.
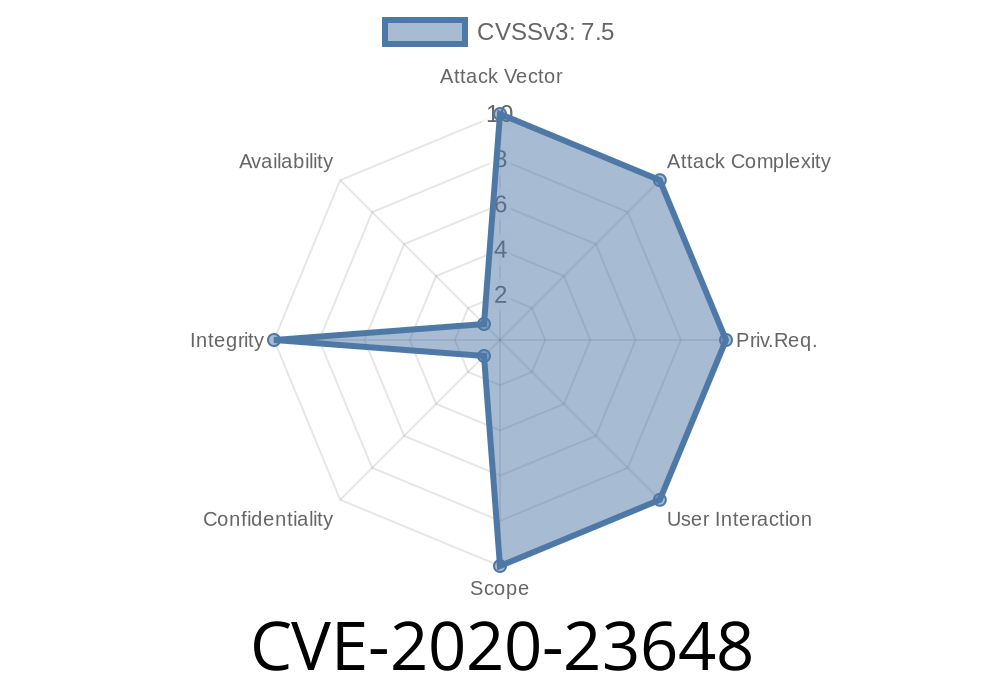
The RT-N12E 2.0.0.39 is vulnerable to four critical vulnerabilities and one moderate vulnerability.
Stored Cross-site Scripting (XSS)
The stored cross-site scripting (XSS) vulnerability of Asus RT-N12E 2.0.0.39 allows attackers with the intention of executing arbitrary code on the victim’s system to exploit the flaw in order to carry out a web-based privilege escalation.
The proper input validation is needed on any web application that handles user-submitted data, but it was not implemented in this case when handling the POST request containing the attacker’s payload.
When parsing the POST request, an attacker can send a particular value as a parameter and execute arbitrary JavaScript code on the victim’s system with XSS privileges.
Asus RT-N12E 2.0.0.39 software also has a CSRF vulnerability which allows attackers to change the administrator password from remote locations by exploiting CSRF flaws in several different ways. One possible way is if an attacker sends a specially crafted link to someone visiting your website, then they will be able to change their administrator password without changing it themselves or going through administrative channels, thus giving them admin privileges on your system without you knowing about it until you are notified by email or alerted through other means that something has happened on your website's administration page and you decide go check what's going on there and find yourself locked out because someone changed your password without permission while impersonating you while they were logged in as an administrator under an account that has admin privileges with no one else knowing who they really are
What is Asus RT-N12E?
Asus RT-N12E is a wireless router which has been widely used around the world.
The firmware version of Asus RT-N12E 2.0.0.39 was released on May 1, 2018 but it was not until July 2018 that the Chakra Scripting Engine vulnerability in Asus RT-N12E 2.0.0.39 was identified and disclosed and enabled cross-site scripting (XSS) attacks for Asus RT-N12E 2.0.0.39 users, leading to the first case of remote code execution that affects all of its devices worldwide.
Timeline
Published on: 10/19/2022 11:15:00 UTC
Last modified on: 10/24/2022 16:01:00 UTC