Intel has issued updates to the software installer to mitigate this issue. Further information can be found on Intel’s software installer advisory. CVE-2018-3620: Uncontrolled search path in the installer for Intel(R) System Studio versions 2018R1 and earlier. CVE-2018-3621: Uncontrolled search path in the installer for Intel(R) System Studio versions 2018R2 and earlier. CVE-2018-3622: Uncontrolled search path in the installer for Intel(R) System Studio versions 2018R3 and earlier. CVE-2018-3623: Uncontrolled search path in the installer for Intel(R) System Studio versions 2018R4 and earlier.
Vulnerability in custom BIOS firmware for Intel(R) vPro(R) Management Engine Interface, versions prior to version 9.1.1.1, may allow an authenticated user to potentially enable escalation of privilege via local access.
CVE-2018-3625: Uncontrolled search path in the custom BIOS firmware for Intel(R) vPro(R) Management Engine Interface versions prior to version 9.1.1.1.
Vulnerability in the BIOS of Lenovo systems with an AMT(R) component may allow an authenticated user to potentially enable escalation of privilege via local access.
CVE-2018-3626: Uncontrolled search path in the custom BIOS firmware for the Lenovo System with an AMT(R) component.
Vulnerability in
Intel Critical Firmware Update
Intel has released security updates to address a number of vulnerabilities in the company's critical firmware. The vulnerabilities addressed in this update impact a variety of Intel products, including Intel(R) vPro(R) Management Engine Interface, Intel(R) System Studio, and Lenovo systems with an AMT (Active Management Technology) component.
Vulnerability in custom BIOS firmware for Intel(R) vPro(R) Management Engine Interface versions prior to version 9.1.1.1 may allow an authenticated user to potentially enable escalation of privilege via local access.
CVE-2018-3625: Uncontrolled search path in the custom BIOS firmware for Intel(R) vPro(R) Management Engine Interface versions prior to version 9.1.1.1.
Vulnerability in the BIOS of Lenovo systems with an AMT (Active Management Technology) component may allow an authenticated user to potentially enable escalation of privilege via local access.
CVE-2018-3626: Uncontrolled search path in the custom BIOS firmware for the Lenovo System with an AMT (Active Management Technology) component.
Intel-SA-00086: Intel(R) vPro(R) Mangers and Agents a target="_blank" href="https://www.intel.com/co
/en_int/products/security/vpro-mangers-and-agents">vPro(R) Management Engine Interface, versions prior to version 9.1.1.1, may allow an authenticated user to potentially enable escalation of privilege via local access
HackerOne:
This week's blog post is on how to outsource your SEO strategy and avoid the five most common mistakes.
The article opens with a paragraph on why outsourcing SEO is a good idea, followed by three paragraphs explaining the benefits of advertising on Facebook and how you can target your ideal audience. This blog post talks about the importance of digital marketing and six reasons why it is important for your company.
Description
Vulnerability in the BIOS of Lenovo systems with an AMT(R) component may allow an authenticated user to potentially enable escalation of privilege via local access.
Lenovo systems prior to version 3.0.2 solutions may be vulnerable.
Intel Product Security Incident Response Team
(PSIRT) - A vulnerability in custom BIOS firmware for Intel(R) vPro(R) Management Engine Interface, versions prior to version 9.1.1.1, may allow an authenticated user to potentially enable escalation of privilege via local access.
Intel has issued updates to the software installer to mitigate this issue. Further information can be found on Intel’s software installer advisory.
Timeline
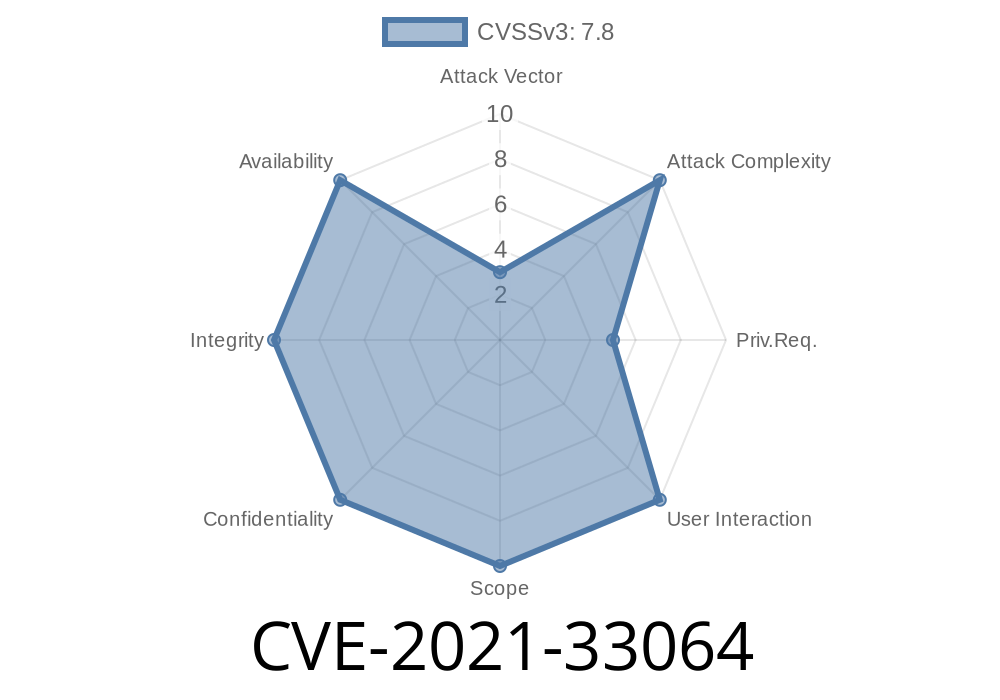
Published on: 11/11/2022 16:15:00 UTC
Last modified on: 11/16/2022 02:33:00 UTC