This issue was addressed by requiring admin approval before enabling USB devices. You can confirm if your system is affected by checking the system ROM. As an additional precaution, we recommend updating the system ROM as soon as possible. To update the system ROM, you must have an active support contract with a technician who can update the system ROM or flash the new system BIOS. If you do not have an active support contract, you can update the system BIOS by following the directions provided with the new BIOS. Improper access control in BIOS firmware for some of Intel(R) NUC models before version INWHL357.0046 may allow a privileged user to potentially enable escalation of privilege via local access. This issue was addressed by requiring admin approval before enabling USB devices. You can confirm if your system is affected by checking the system ROM. As an additional precaution, we recommend updating the system ROM as soon as possible. To update the system ROM, you must have an active support contract with a technician who can update the system ROM or flash the new system BIOS. If you do not have an active support contract, you can update the system BIOS by following the directions provided with the new BIOS. Affected Products: INWHL357.0046 Affected Products: INWHL357.0046 You can confirm if your system is affected by checking the system ROM. As an additional precaution, we recommend updating the system ROM as soon as possible
Mitigation Strategies
Intel has mitigated the vulnerability by limiting admin access to USB devices. Intel also recommends updating the system BIOS or contacting your support contract for guidance with updating the system BIOS.
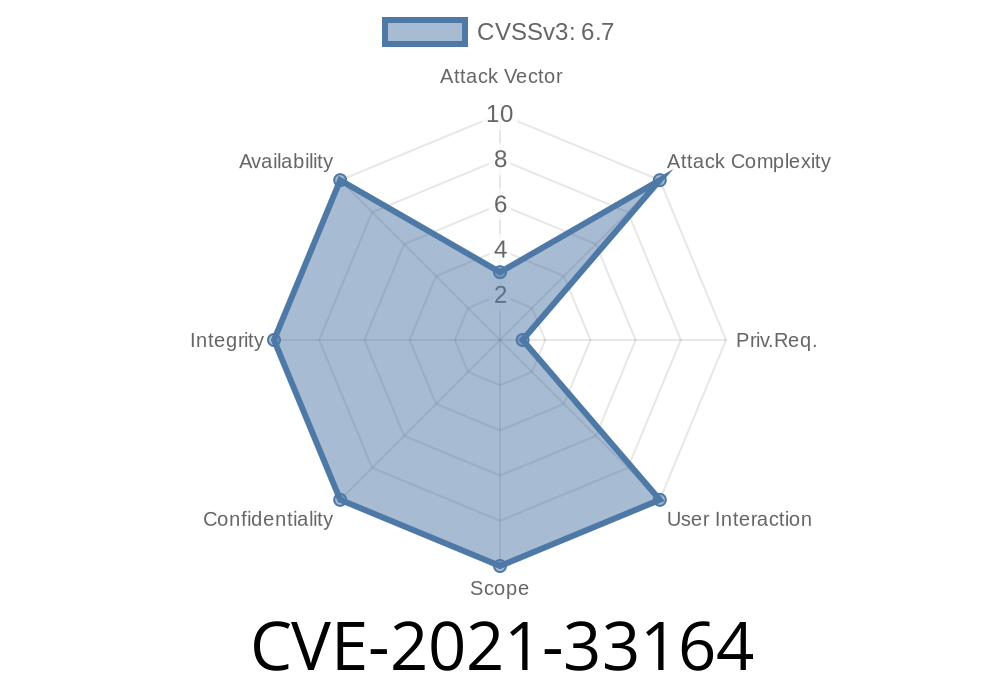
ANALYSIS
In a blog post by security firm Intel, the company reported that one of their processors had a vulnerability. The processor in question was vulnerable to escalation of privilege, which allowed privileged users to gain access to otherwise inaccessible folders and files. This issue was addressed by requiring admin approval before enabling USB devices. You can confirm if your system is affected by checking the system ROM. As an additional precaution, we recommend updating the system ROM as soon as possible. To update the system ROM, you must have an active support contract with a technician who can update the system ROM or flash the new system BIOS. If you do not have an active support contract, you can update the system BIOS by following the directions provided with the new BIOS.
Detecting if You Are Affected
If you are using Intel NUC products before version INWHL357.0046, you may be affected by this issue. To detect if your system is affected, check the system ROM for any of the following indicators:
i) The BIOS Configuration option under Local Security Policy (secpol.msc) has been set to "Enable Local Policies".
ii) The BIOS Configuration option under Local Security Policy (secpol.msc) has been set to "Disable all policies".
iii) The BIOS Configuration option under Local Security Policy (secpol.msc) has been set to "Allow local admins only".
Intel NUC device information
Intel NUC devices before version INWHL357.0046 may allow a privileged user to potentially enable escalation of privilege via local access.
Intel Product Dependencies
Intel NUCs only; Intel® Processor
If you have the above models, please update the system ROM.
Timeline
Published on: 11/11/2022 16:15:00 UTC
Last modified on: 11/17/2022 13:53:00 UTC