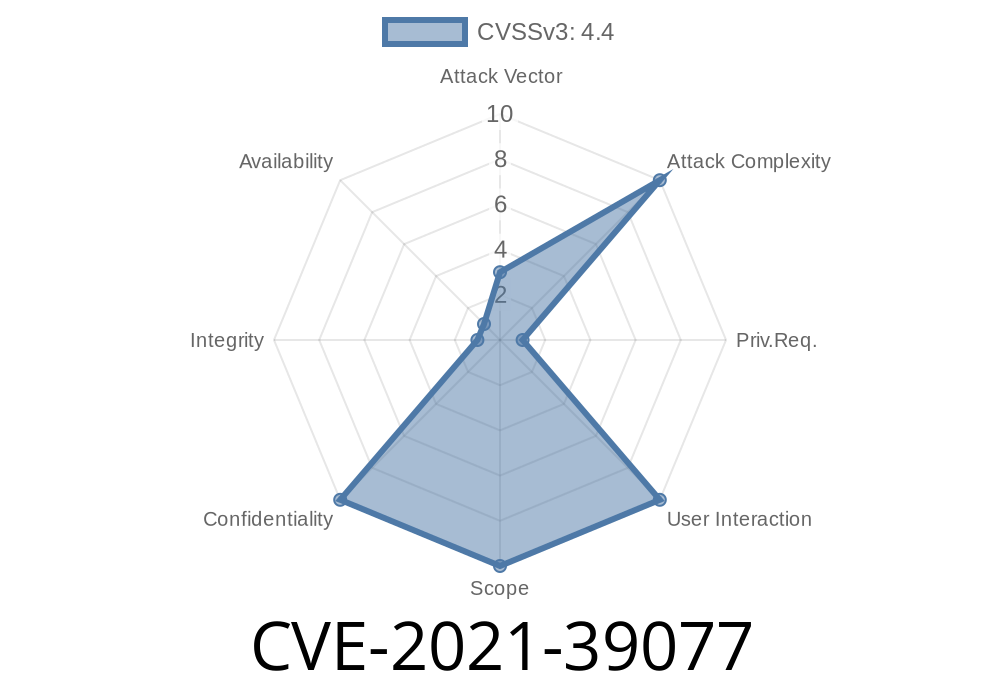
When talking about data protection, even security tools can sometimes have cracks in their armor. One such example is CVE-2021-39077, a vulnerability found in IBM Security Guardium versions 10.5 up to 11.4. In this deep-dive, we’ll break down what went wrong, look at how the flaw works, and even show code snippets to make it crystal clear.
What is IBM Security Guardium?
IBM Security Guardium is a widespread product used by enterprises to secure databases and enforce compliance. It monitors data traffic, discovers sensitive data, and helps detect unauthorized activity. Given its role, it typically has access to a lot of privileged information—including user credentials.
10.6
- 11.
11.4
store *user credentials* in clear text, or readable format, on the file system. This blunder means a user with access to the server and some privileges can simply read these secrets without breaking a sweat.
Official Description (IBM X-Force ID: 215587)
> "IBM Security Guardium (IBM X-Force ID: 215587) stores user credentials in clear text which can be read by a local privileged user."
– IBM Security Bulletin for CVE-2021-39077
Who is Affected?
Any organization running IBM Security Guardium on the versions listed above—especially if the system is shared, or not locked down to a minimal set of administrators.
*Attackers* don’t need to exploit advanced techniques—just a login with the right access can be enough.
Technical Details: How the Credentials Leak
During routine tasks, Guardium creates and saves configuration files. Some of these files contain username and password pairs in plain, readable text.
Where are the credentials?
The files are typically found in the Guardium configuration directory. Here’s an example file path (might differ depending on your setup):
/opt/guardium/config/dbconfig.conf
Inside, you might find something like
db_host=192.168..2
db_user=guard_user
db_password=SuperSecretPassword
db_port=3306
There’s no encryption or obfuscation—if you open the file with cat, less, or any text editor, you’ll see the actual password.
Here’s how a local, privileged user could read the stored credentials
#!/bin/bash
# Simple script to show how credentials can be leaked
config_file="/opt/guardium/config/dbconfig.conf"
if [[ -f $config_file ]]; then
echo "---- Contents of $config_file ----"
cat $config_file
else
echo "Config file not found. Check the path."
fi
Output might look like
---- Contents of /opt/guardium/config/dbconfig.conf ----
db_host=192.168..2
db_user=guard_user
db_password=SuperSecretPassword
db_port=3306
A privileged attacker (such as a local admin or someone with access to Guardium logs and configs) could harvest these credentials and use them to access databases or other infrastructure components.
Real-World Impact
- Data Breach Risk: Attackers could access sensitive databases, download confidential info, or tamper with monitoring setups.
- Pivoting: With valid server credentials, attackers can move deeper into the network, accessing more systems.
- Compliance Failure: For organizations bound by regulations (HIPAA, GDPR, SOX), failing to encrypt credentials is a red flag for audits.
Mitigation and Fix
IBM has released fixes for this issue. If you’re running an affected version, upgrade immediately or apply the necessary patches per the official advisory.
- IBM Official Advisory for CVE-2021-39077
Strictly limit access to Guardium servers.
2. Monitor file access and permissions on /opt/guardium/config/.
Never store passwords in clear text. Even trusted security tools can make mistakes.
- Always limit local/admin access, especially on servers with sensitive configs.
References
- IBM Security Bulletin: CVE-2021-39077
- NVD Entry for CVE-2021-39077
- IBM X-Force Exchange ID: 215587
Keep your guard up—even when it comes to Guardium. Mistakes like this show that zero trust should apply to your security tools, too. Please patch, review permissions, and remember: Plaintext passwords are a hacker’s best friend!
Timeline
Published on: 11/03/2022 20:15:00 UTC
Last modified on: 11/09/2022 22:15:00 UTC