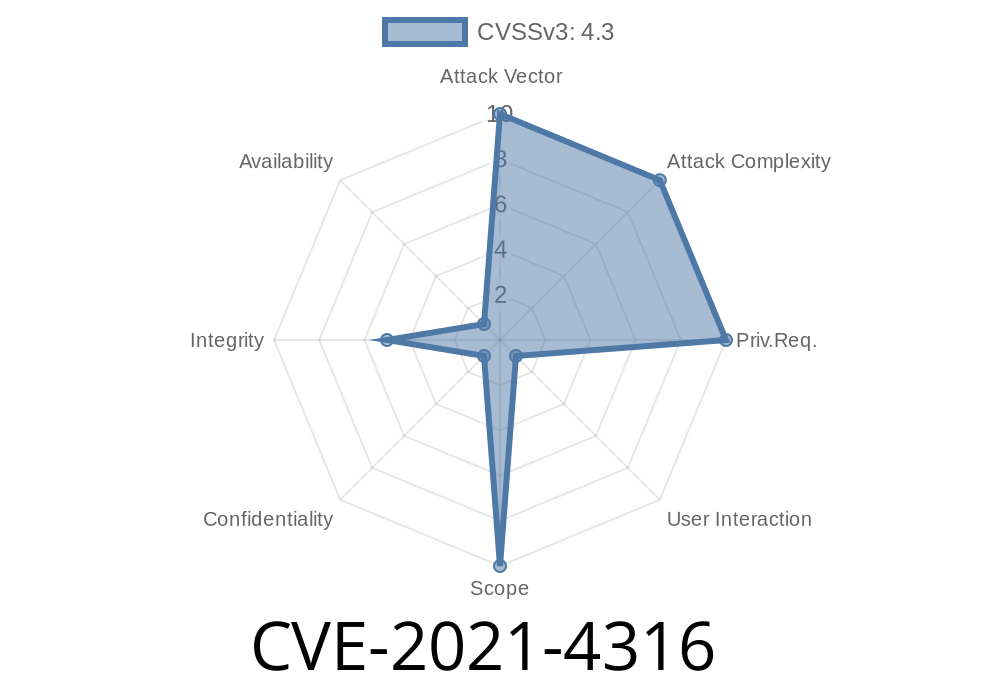
CVE-2021-4316 is a security vulnerability discovered in the Cast UI feature of Google Chrome before version 96..4664.45. This bug let remote attackers use a specially crafted HTML page to spoof parts of the browser’s user interface. In simple terms, that means a website could make some browser popups or panels look different – tricking you into believing you’re dealing with a trusted element, when you’re not.
While Google labeled this as a Low severity risk, if you’re curious about how browser spoofing happens or want a peek behind the scenes, let’s dig in.
What is the Cast UI in Chrome?
Chrome’s “Cast” feature lets you beam tabs, videos, or your desktop to a Chromecast or similar device. To do these things, Chrome shows built-in popups and panels (the “Cast UI”) that users generally trust.
If an attacker can make a website look like this trusted part of Chrome, they could attempt to trick you. Maybe they’d try to steal your login, or get you to click on something nasty.
Understanding the Vulnerability
CVE-2021-4316 comes down to this: The Cast UI in Chrome before v96..4664.45 didn’t block web pages from mimicking or interfering with how Chrome presents certain UI elements.
A user visits a malicious site.
2. The site uses tricky HTML and CSS to fake the Cast popup or status indicator, even showing a legitimate-looking Chrome UI.
3. The user thinks they’re interacting with Chrome, but actually, it’s just part of the webpage – controlled by the attacker.
Here’s a very simplified version of what a “spoofed” Cast popup could look like
<!-- Malicious page faking Chrome's Cast UI -->
<style>
#fakecast {
position: fixed;
top: 40px;
right: 20px;
width: 320px;
background: #fff;
border-radius: 8px;
box-shadow: 2px 8px rgba(,,,.12);
font-family: Arial, sans-serif;
border: 1px solid #EEE;
z-index: 99999;
padding: 20px;
}
#fakecast .header {
font-size: 18px;
font-weight: bold;
margin-bottom: 8px;
color: #333;
}
#fakecast .device-list {
margin: 12px ;
}
#fakecast .btn {
background: #1a73e8;
color: #fff;
border: none;
padding: 8px 16px;
border-radius: 4px;
cursor: pointer;
}
</style>
<div id="fakecast">
<div class="header">Cast Tab</div>
<div class="device-list">
<p>Living Room TV</p>
<p>Bedroom Chromecast</p>
</div>
<button class="btn" onclick="stealInfo()">Connect</button>
</div>
<script>
function stealInfo() {
alert("Malicious Action: Your data could be sent here!");
// Example: send cookies or other info to attacker
}
</script>
A page using this snippet could pop a “Cast” dialog that looks shockingly real.
Potential Risks and Impact
While this bug didn’t let hackers steal data directly, it enabled social engineering. Unsuspecting users could have been tricked into clicking links, entering passwords, or even downloading malware – all while thinking they were interacting with Chrome, not a website.
Imagine a popup asking you to “Sign in to Cast” with your Google account, but you’re really typing into a web form controlled by a crook.
How Was It Fixed?
Google patched this by further isolating the Cast UI from web content, making it impossible (or much harder) for a website to imitate or place elements exactly where system UI appears.
The fix landed in Chrome 96..4664.45. If you’re on a newer browser (and you really should be), you’re protected.
Here’s a conceptual exploit (“pseudo-code”)
// On page load
if (navigator.userAgent.includes('Chrome')) {
showFakeCastPanel();
}
function showFakeCastPanel() {
// Insert above HTML dynamically, matching Chrome’s styling as close as possible
// Add phishy actions, like 'Sign in to Chromecast' or 'Grant Access'
}
References
- Chromium Issues – Issue 1267232: Cast UI improperly implemented
- Chrome Releases Blog – Stable Channel Update for Desktop
- NIST NVD Entry for CVE-2021-4316
Conclusion
CVE-2021-4316 is a classic example showing that even “low severity” issues can put users at risk, especially when they involve UI and social engineering.
How to stay safe:
Always keep Chrome up to date.
- Be cautious of popups or elements that look like browser/system UI, especially when they ask for credentials or downloads.
Want more?
- See the official bug thread, or
- Read how Chrome’s team protects users from spoofing attacks.
If you learned something, share this post and help others spot these sneaky tricks!
Timeline
Published on: 07/29/2023 00:15:00 UTC
Last modified on: 08/02/2023 03:55:00 UTC