On Linux systems, the kernel's networking code is critical for hardware support and connectivity. Sometimes, even fixes for old bugs can introduce new vulnerabilities. CVE-2021-46905 is an example—this bug emerged in the hso (Option High-Speed Mobile Devices) driver for certain USB serial devices. Let's break down what happened, why it was a problem, and how developers fixed it.
What Is CVE-2021-46905?
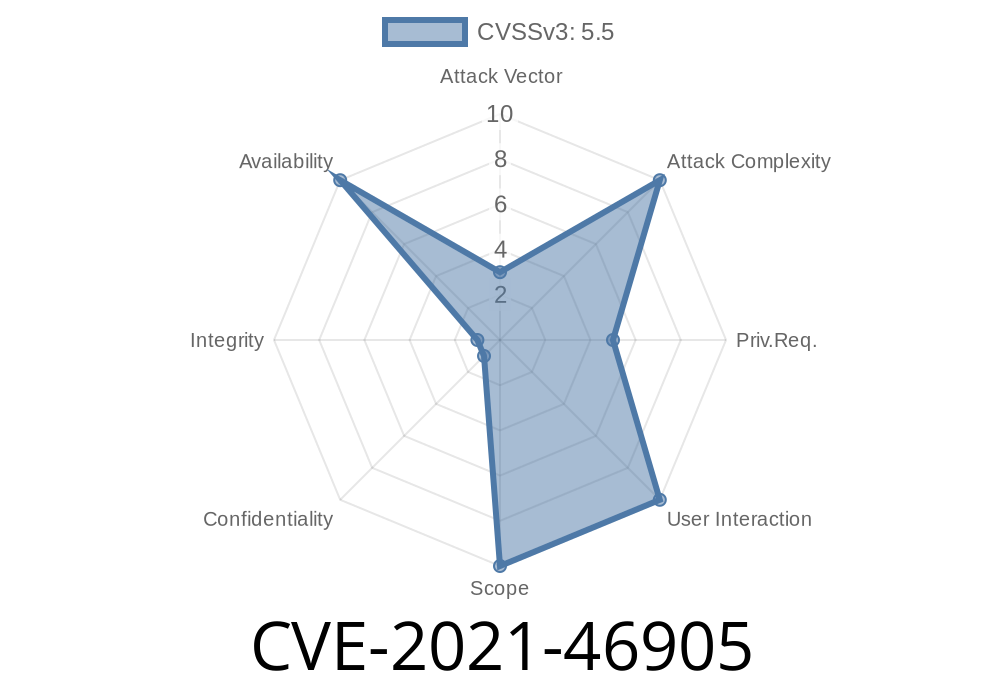
CVE-2021-46905 is a vulnerability in the Linux kernel's hso driver, used for some USB WAN modems. A previous fix intended to address a race condition ended up causing a NULL-pointer dereference, which could crash the system (kernel panic) if you unplugged certain USB devices.
Quick Timeline
1. Original bug: Race condition when unregistering a tty device (tracked by syzbot).
2. Commit 8a12f8836145: Tried to fix the race. Introduced a new bug—a NULL pointer dereference on every device disconnect.
Source of the Problem
The vulnerable code is in the hso_serial_tty_unregister function. After freeing up resources, the code continued to access the serial device table, which could now be NULL. Here’s a simplified view:
static void hso_serial_tty_unregister(struct hso_serial *serial)
{
// ... unregister from tty ...
serial->parent->serial_table[serial->minor] = NULL;
// At this point, serial_table[minor] is NULL
// Bad: Later code still tries to use serial_table[minor] unconditionally
}
When the device disconnects, later parts of the code may try to access serial->parent->serial_table[serial->minor], which is now NULL, leading to a kernel crash.
How to Exploit
An attacker (or even a regular user) could simply unplug a compatible USB modem at the right time, triggering the bug and causing a system crash. While this is a denial-of-service issue, it cannot directly lead to privilege escalation.
Real-World Impact
Although most people won't meet this bug unless they use the specific hardware (hso-supported devices), this kind of crash can be used to disrupt systems that rely on USB WAN devices for remote connectivity—think routers, kiosks, or critical IoT hardware.
The Patch
Here’s the essence of the fix as seen in kernel commit ea3e60131b7:
Key takeaway: Never access the serial device table after it's been released.
Patched code checks for NULL and avoids accessing freed memory
if (serial->parent->serial_table[serial->minor]) {
// Only access if not NULL
cleanup_function(serial->parent->serial_table[serial->minor]);
}
By properly managing the device table, the code no longer dereferences NULL pointers on disconnect.
References
- Original Syzbot Report
- Introduced by commit 8a12f8836145
- Fixed by commit ea3e60131b7
- CVE-2021-46905 at NVD
Summary
- CVE-2021-46905: Unplugging an hso USB device could crash the Linux kernel due to a NULL-pointer dereference after an earlier "fix" regressed device cleanup logic.
Mitigation: Update your kernel to a version that includes the fix.
Be sure to keep your system updated, especially if you're running networked hardware with USB WAN modems!
Final Advice
If you or your company uses mobile broadband hardware on Linux, check your kernel's version and ensure it's newer than kernel v5.10.53 (which contains the fix).
For developers: Always audit changes for race conditions and memory management bugs—even after bugfix patches.
Timeline
Published on: 02/26/2024 16:27:45 UTC
Last modified on: 04/17/2024 19:30:05 UTC