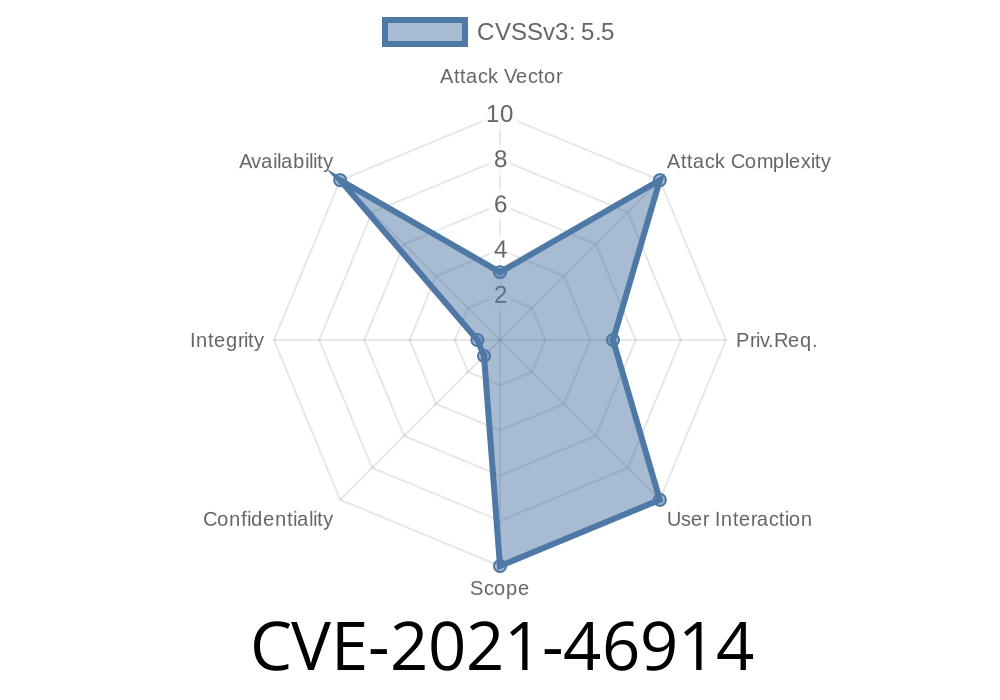
In early 2021, a subtle but potentially disruptive vulnerability was discovered in the Linux kernel’s ixgbe driver—the driver responsible for Intel 10 Gigabit PCI Express network cards. Filed as CVE-2021-46914, this bug revolved around improper handling of the device’s power management during suspend and resume cycles, which could lead to kernel errors or even device malfunctions in certain situations.
In this article, we break down the vulnerability, show the root cause with code samples, discuss its impact, and provide exploit and fix details in plain language for system administrators and enthusiasts.
What is CVE-2021-46914?
CVE-2021-46914 describes a logic error in the ixgbe kernel driver. When a Linux system suspends and resumes (such as during sleep or hibernation), the driver failed to properly balance calls enabling and disabling the PCI device.
Here’s the summary
- pci_disable_device() was being called on shutdown, decreasing the device’s enable counter (dev->enable_cnt).
- However, pci_enable_device_mem() (which increases the counter) was removed from the resume code in a previous update.
- This mismatch led to an unbalanced enable/disable cycle, triggering warnings like
ixgbe 000:17:00.1: disabling already-disabled device
- Over time, this could make the device unusable after multiple suspend/resume events.
Here’s how the kernel warning typically looked
ixgbe 000:17:00.1: disabling already-disabled device
Call Trace:
__ixgbe_shutdown+x10a/x1e [ixgbe]
ixgbe_suspend+x32/x70 [ixgbe]
pci_pm_suspend+x87/x160
? pci_pm_freeze+xd/xd
dpm_run_callback+x42/x170
__device_suspend+x114/x460
async_suspend+x1f/xa
async_run_entry_fn+x3c/xf
process_one_work+x1dd/x410
worker_thread+x34/x3f
? cancel_delayed_work+x90/x90
kthread+x14c/x170
? kthread_park+x90/x90
ret_from_fork+x1f/x30
Technical Analysis
In simpler terms, think of the enable/disable functions as a matching pair of “on” and “off” switches. If you call “off” too many times, problems start.
### The Broken Suspend/Resume Logic
- Before, whenever the device resumed, the driver would call pci_enable_device_mem() to correctly re-enable the hardware.
- A code cleanup in commit 6f82b2558735 removed this resume call.
That means
- For each suspend/resume cycle, the "device disable" counter goes out of sync.
Before the fix, the resume code looked roughly like
static int ixgbe_resume(struct device *dev)
{
// ...previous code...
// pci_enable_device_mem() call was REMOVED
// ...next code...
}
But, on shutdown
static void __ixgbe_shutdown(struct pci_dev *pdev)
{
// ...shutdown routines...
pci_disable_device(pdev);
// ...more code...
}
The patch added back the missing line in ixgbe_resume()
static int ixgbe_resume(struct device *dev)
{
// ...previous code...
pci_enable_device_mem(pdev); // <-- RESTORED
// ...next code...
}
See the fix commit
- ixgbe: fix unbalanced device enable/disable in suspend/resume
Exploit Details
This is not a remote exploit—it’s a reliability bug, not a security hole in the classic sense. However, it could be abused locally or unintentionally:
- Repeatedly suspending/resuming a machine (by the user, or a malicious script) could push the device into an error state.
- Network connectivity could fail, essential hardware might be lost until restart, or logs could overflow due to spamming with error messages.
`
4. Check network state: Eventually, the NIC (network interface card) could stop functioning, requiring a reboot.
Update your kernel to a fixed version (>=5.13, or with backported patches for LTS).
- If you manage servers with Intel 10G cards, check dmesg logs for these errors after suspend/resume cycles.
- For distros: ensure your kernel contains this fix PR.
References
- Original Fix Commit - Torvalds Linux
- ixgbe: use generic power management
- Patch on Netdev Mailing List
- CVE-2021-46914 at NVD
Conclusion
CVE-2021-46914 is a simple illustration of how small mistakes in kernel driver bookkeeping can cause outsized problems. While it wasn’t a critical security hole, it could seriously impact production systems, especially in environments relying on power management or with frequent suspend/resume operations. Always keep your systems patched, and be on the lookout for kernel messages—sometimes, they’re your best friend!
Want to check if you're affected? Monitor your logs, update your systems, or dive into kernel source code using the links above!
Timeline
Published on: 02/27/2024 07:15:07 UTC
Last modified on: 04/10/2024 14:03:21 UTC