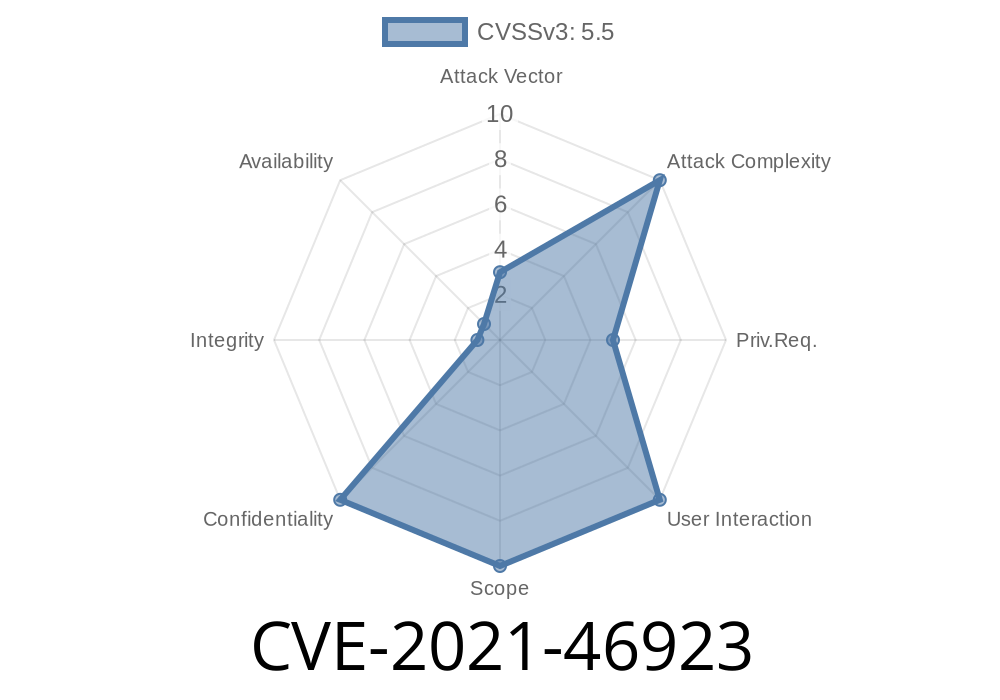
The Linux kernel is the backbone of countless systems, powering everything from Android smartphones to powerful servers. Because it’s so widely used, any security hole is a big deal. One such vulnerability was CVE-2021-46923, impacting the fs/mount_setattr code. This post breaks down what the bug was, how it happened, why it was dangerous, and how it was fixed—using simple language, with code snippets and links to learn more.
What Is CVE-2021-46923?
CVE-2021-46923 is a vulnerability resolved in the Linux kernel’s file system mounting code. In simple terms, when mount_setattr() tried to apply new properties to a mounted file system, there was a way a reference to an internal structure could be leaked and *never freed*. This would eat away at available resources. In a worst-case scenario, clever attackers could use this to cause the system to misbehave or even crash.
The Technical Details
mount_setattr() is a Linux kernel feature that allows users to modify mount properties of a file system, such as making it read-only. It uses a structure called mount_kattr. Think of mount_kattr as a package of attributes the kernel uses to update a file system’s mount. If you’re not careful managing these packages ("references"), you can end up “leaking” them—leaving data in memory that won’t be reused or freed.
This bug happened because finish_mount_kattr()—the function that cleans up after mount_kattr—was not always called in error cases.
Here’s a simplified version of what the buggy code looked like
struct mount_kattr *kattr = build_mount_kattr(...);
if (path_lookup_failed) {
// early return, but kattr is not cleaned up here
return -error;
}
// normal path
...
finish_mount_kattr(kattr);
- Problem: If path_lookup_failed, the code *returned* early without cleaning up the kattr reference.
- Impact: Each time this happened, a reference to kattr would leak—over time, these leftover references would pile up in the system.
Why Was This a Big Deal?
Leaking references in this way can slowly reduce the available memory or resource pool, causing system performance to degrade and even crash (“denial of service”). Worse, certain users could intentionally trigger this scenario to attack the system.
This was especially problematic when using “idmapped mounts,” a newer Linux feature for remapping user and group IDs in container environments. If path lookup failed while requesting an idmapped mount, the bug would surface and leak an extra reference, exposing the system to potential attack.
The Fix
The kernel developers fixed this by making sure finish_mount_kattr() always gets called if mount_kattr was built, even on errors.
Here’s the corrected code flow
struct mount_kattr *kattr = build_mount_kattr(...);
if (path_lookup_failed) {
finish_mount_kattr(kattr); // clean up before returning!
return -error;
}
// normal path
...
finish_mount_kattr(kattr);
By ensuring the cleanup function is always called, any references taken during build_mount_kattr() get properly released, and no memory is leaked.
The Actual Patch
You can read the kernel patch here:
kernel.org commit: mount_setattr: always cleanup mount_kattr
Or, here’s the critical part of the change
- if (path_lookup_failed)
- return -error;
+ if (path_lookup_failed) {
+ finish_mount_kattr(kattr);
+ return -error;
+ }
Can This Be Exploited?
On its own, the bug is mainly a *resource exhaustion* vulnerability—someone could try to repeatedly hit the error case and slowly fill up resources on the system, causing slowdowns or crashes (denial of service). There’s no straightforward way to use it to gain unauthorized access or run code, but it still posed a threat to system stability.
How to Protect Yourself
- Update Your Kernel! The best way to stay safe is to run a Linux kernel version that includes this patch (look for 5.12 and later, or check your distro’s security advisories).
- Monitor Kernel News: Subscribe to security mailing lists or your Linux distribution’s update feed.
Resources & References
- Linux Kernel Patch – Always cleanup mount_kattr
- CVE-2021-46923 on NVD
- Red Hat Security Advisory
- Man page: mount_setattr() system call
Summary
CVE-2021-46923 was a subtle but important bug in the Linux kernel’s file system code. It shows how even small ecosystem mistakes—forgetting to call a cleanup function—can impact system stability and security over time. Thankfully, the open-source community caught and patched this, so just keep your kernel updated. If you want to read the code or try your hand at finding bugs, check out the links up above!
Timeline
Published on: 02/27/2024 10:15:07 UTC
Last modified on: 04/10/2024 15:25:34 UTC