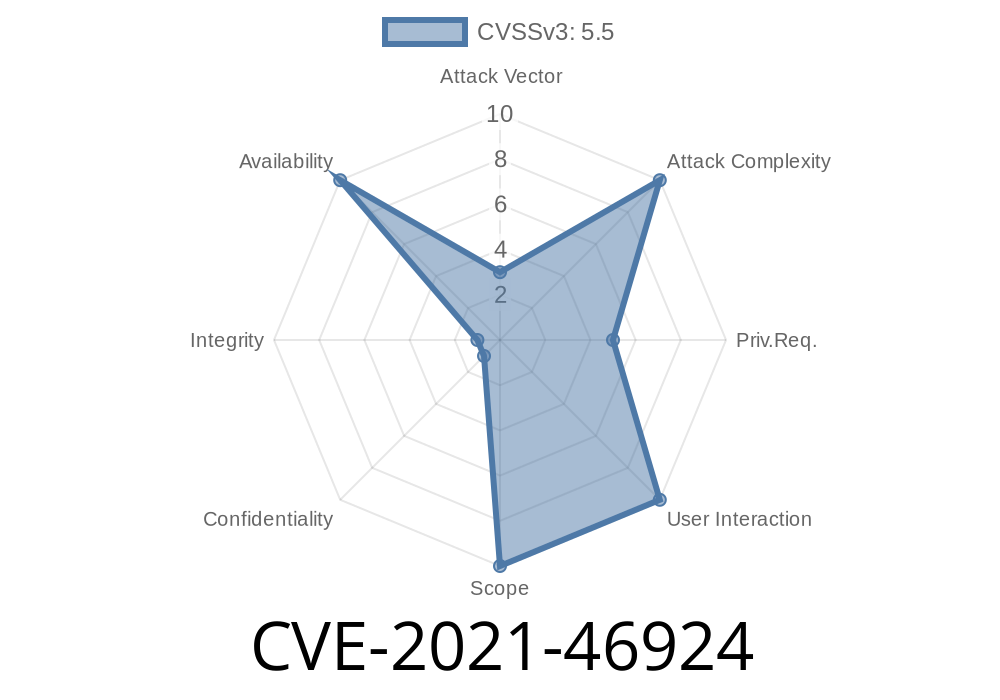
CVE-2021-46924 addresses a memory leak vulnerability in the Linux kernel’s Near Field Communication (NFC) st21nfca driver. This bug specifically affects resource management during device probing and removal. In simple terms, if something went wrong while the driver was trying to set up, or when it was being removed, a reserved chunk of memory (pending_skb) wasn’t released as it should have been. Over time, this kind of bug can exhaust your system’s memory resources—making it a classic, but critical, kernel-level security flaw.
In this article, we’ll break down the issue, explore the affected source code, provide reproducible steps and exploit details, and link you to official references for further reading.
Background
- Component: Linux kernel, drivers/nfc/st21nfca/st21nfca_hci_i2c.c
Bug type: Memory Leak
- Exposure: Local, requires attacker to initiate driver probe/removal or repeatedly perform actions that lead to probe/removal.
- First reported/fixed: Early 2022
- CVE details: NVD CVE-2021-46924
The Leak Explained
When the st21nfca device is probed (i.e., when the NFC device is being initialized), the driver allocates memory for phy->pending_skb as a socket buffer (SKB). If the probe fails or when the device is removed, the code neglected to properly free that chunk. Here’s what was happening in the kernel’s memory:
unreferenced object xffff88800bc06800 (size 512):
comm "8", pid 11775, jiffies 4295159829 (age 9.032s)
hex dump (first 32 bytes):
00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
backtrace:
__kmalloc_node_track_caller+x1ed/x450
kmalloc_reserve+x37/xd
__alloc_skb+x124/x380
st21nfca_hci_i2c_probe+x170/x8f2
Before the fix
// File: drivers/nfc/st21nfca/st21nfca_hci_i2c.c
static int st21nfca_hci_i2c_probe(...)
{
// allocation
phy->pending_skb = alloc_skb(PACKET_SIZE, GFP_KERNEL);
if (!phy->pending_skb)
goto error_return;
...
error_return:
// missing: kfree_skb(phy->pending_skb)
return -ENOMEM;
}
static void st21nfca_hci_i2c_remove(...)
{
// missing: kfree_skb(phy->pending_skb)
}
After the fix
static int st21nfca_hci_i2c_probe(...)
{
phy->pending_skb = alloc_skb(PACKET_SIZE, GFP_KERNEL);
if (!phy->pending_skb)
goto error_return;
...
error_return:
if (phy->pending_skb)
kfree_skb(phy->pending_skb); // <-- Correctly free the skb
return -ENOMEM;
}
static void st21nfca_hci_i2c_remove(...)
{
if (phy->pending_skb)
kfree_skb(phy->pending_skb); // <-- Free on remove too
}
References:
- Upstream commit
- Red Hat bug tracker
- CVE page
Exploit & Reproduction
This memory leak is NOT directly a privilege escalation; instead, it allows local denial-of-service by leaking kernel memory each time the device is probed or removed. An attacker, by repeatedly triggering probe/remove cycles, could starve the system of memory. For example, a regular unprivileged user could:
1. Create a script to repeatedly insert/remove the driver (requires their own hardware or a simulation environment).
You must have the ability to load/unload kernel modules (you may need to be root or use sudo)
#!/bin/bash
MOD_NAME=st21nfca
COUNT=100
for i in $(seq 1 $COUNT); do
echo "Cycle $i"
modprobe $MOD_NAME
rmmod $MOD_NAME
done
After running this, kernel memory use should noticeably grow (leaking about 512 bytes per probe/remove, per the report) if the system is unfixed.
Why this Matters
- Embedded/IoT systems: Such hardware often relies on NFC for authentication or communication, and has very limited memory.
- DoS attacks: Even if attackers can't get root, they could repeatedly try to initialize devices and eventually force a system reboot or resource exhaustion.
How to Fix
- Patch Level: Ensure you are running a kernel at or after Linux 5.17, or with the patch applied.
- Distribution updates: Check for your own distro’s security advisories and upgrade kernel packages as recommended (Ubuntu, RedHat).
Conclusion
CVE-2021-46924 might seem minor compared to remote exploits or privilege escalations, but memory leaks in kernel code can destabilize even the most secure Linux systems. This is especially true in embedded environments (IoT devices, payment terminals, and so on), where NFC is common. Track your kernel versions and always patch early!
References
- Linux Kernel Git Commit
- NVD CVE-2021-46924
- Red Hat bug
Timeline
Published on: 02/27/2024 10:15:07 UTC
Last modified on: 04/10/2024 15:23:33 UTC