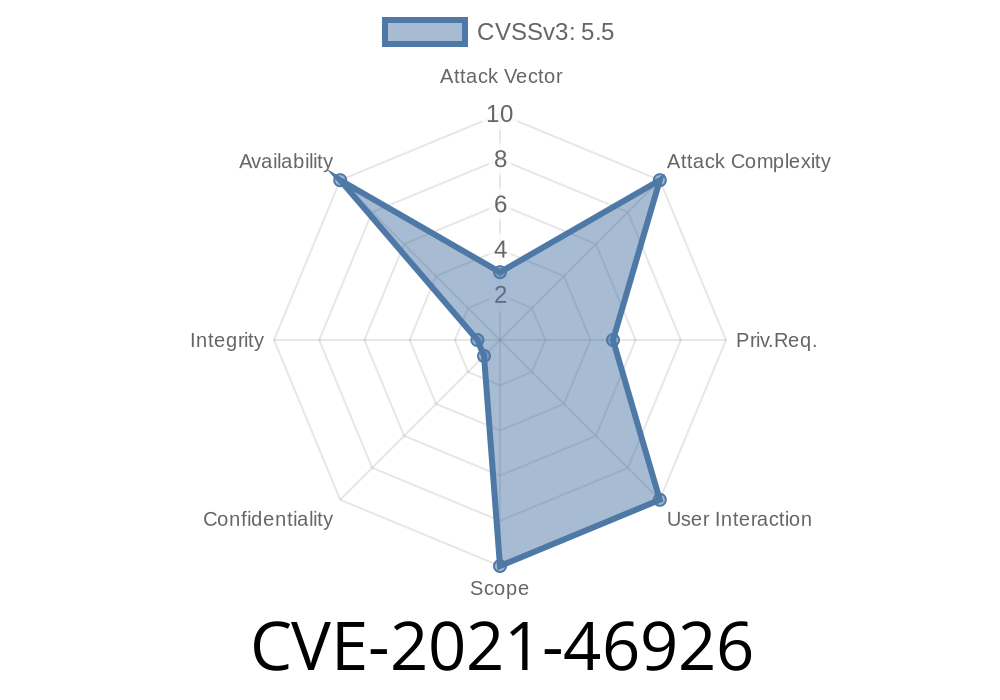
The Linux kernel is the backbone of many systems, from desktops and laptops to embedded devices and servers. With such important software, kernel bugs can have broad impacts. In this long read, we’re going to dive deep into a now-fixed security issue, CVE-2021-46926, which affected the SoundWire controller detection logic in the ALSA HDA Intel driver, specifically around ACPI pointer handling. We'll break down what the vulnerability was, how it was resolved, and why it mattered, all in simple and understandable terms.
What is CVE-2021-46926?
CVE-2021-46926 refers to a vulnerability discovered in the Linux kernel, specifically in the code responsible for detecting SoundWire controllers on Intel platforms using the ACPI (Advanced Configuration and Power Interface). This vulnerability involved how pointers were managed during the detection process.
A quick summary
- The code set an ACPI handle pointer before actually confirming if the device was a valid SoundWire controller.
As a result, in some scenarios, the pointer could reference an invalid or unexpected object.
- This might not directly crash the system, but could lead to unpredictable behavior, potential dereferencing of wrong/malicious pointers, and made the kernel less robust in handling certain hardware configurations.
Where Did It Happen?
This behavior was found in the intel-sdw-acpi part of the ALSA (Advanced Linux Sound Architecture) subsystem. SoundWire (SDW) is a hardware interface for audio devices.
Here's a simplified version of the problematic code
/* Vulnerable code snippet: */
*sdw_handle = acpi_get_next_child(...); // << sets pointer too early
if (!is_sdw_controller(*sdw_handle)) {
// it's not a controller, but pointer was already set
return NULL;
}
The problem? *sdw_handle is set even if the child is not a valid SoundWire controller. This means the calling function could later try to use this handle improperly.
The Fix
The patch hardened (made more strict) the logic for detecting the controller, making sure the handle pointer is only set after verifying the device is truly a SoundWire controller.
Here’s the improved (patched) version
/* Secure and fixed code */
possible_handle = acpi_get_next_child(...);
if (is_sdw_controller(possible_handle)) {
*sdw_handle = possible_handle; // Only set if it REALLY is a controller
return possible_handle;
} else {
return NULL; // Don't set the pointer at all
}
Now, the pointer will only be valid and ready to be used if the device actually matches all criteria.
If the kernel sets pointers incorrectly, it could accidentally point to the wrong device, leading to
- Incorrect device configuration: The system might try to configure or communicate with devices that don’t exist as SoundWire controllers.
- Crashes or instability: Using a pointer in a way the kernel did not expect can destabilize your system.
- Security risks: While there's no direct remote exploit, manipulating kernel pointers poorly is never safe. A maliciously crafted device tree could potentially trigger unwanted behavior.
How Could It Be Exploited?
Though there is no known practical exploit in the wild, a determined attacker with control over the platform’s ACPI tables (such as in some virtualized or compromised environments) could potentially use this bug to:
How Was CVE-2021-46926 Reported and Fixed?
- Discovery: The issue was found and discussed on the Linux kernel mailing lists and tracked as CVE-2021-46926.
Patch: The fix was applied upstream and circulated to distributions.
- Patch commit: You can browse the fix in the kernel’s mainline via this commit.
References
- CVE-2021-46926 at NIST NVD
- Kernel.org commit fixing the issue
- Linux Kernel changelog entry
- SoundWire Protocol Overview (Intel)
How to Check If You’re Safe
1. Kernel Version: Make sure your Linux kernel is updated after March 2023 if you’re on Intel platforms using HDA/ALSA SoundWire.
2. Vendor Patches: Most major distributions (Ubuntu, Red Hat, Fedora, etc) have already patched this vulnerability.
Check dmesg: If you’re unsure, look for ACPI-related errors in dmesg related to SoundWire.
Simple Tip: If you apply kernel security updates regularly, you should already be protected from this bug.
Final Thoughts
This CVE shows that even small pointer mis-handlings can have unwanted consequences in the Linux kernel. They might seem minor, but they are critical for keeping our systems secure, stable, and predictable.
Keep your systems updated. Pay attention to kernel security alerts—even if they seem “minor.”
*Written exclusively for you, with simple language and direct insights. Stay safe, and keep those kernels patched!*
Did you find this breakdown helpful? Share it with fellow Linux users or kernel enthusiasts who care about security!
Timeline
Published on: 02/27/2024 10:15:07 UTC
Last modified on: 04/10/2024 16:26:55 UTC