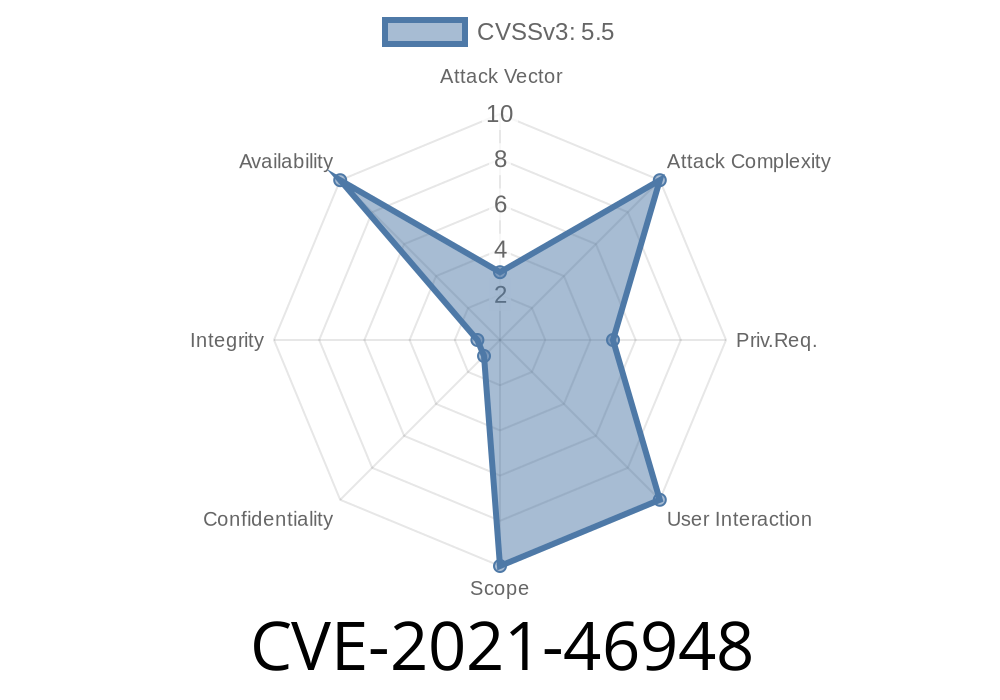
Linux is the backbone of the internet, but even its drivers are not immune from bugs. In early 2021, a serious issue was discovered and fixed in the 'sfc' (Solarflare network card) driver, tracked as CVE-2021-46948. This post explains what went wrong, how it could cause a crash, and how the maintainers fixed the vulnerability.
What Is CVE-2021-46948?
CVE-2021-46948 is a vulnerability in the Linux kernel’s 'sfc' (Solarflare Family) network driver, specifically in how it handles TX (transmit) events. A logic bug made the driver look up a TX queue using the *wrong method*, which could result in NULL pointer errors and system panics (kernel crashes).
Linux Stable mailing list:
commit 29be11447651 ("sfc: farch: fix TX queue lookup in TX event handling")
How Linux Drivers Manage TX Queues
Network drivers often juggle multiple queues (think "lanes for sending packets"). Each queue has an *ID* or *label*.
TXQ type: Different types of queues (for TX, RX, etc).
The problematic function was efx_channel_get_tx_queue(). This function expects a TXQ *type*, but the code was giving it a *label* instead. That’s mixing apples and oranges.
Imagine you need to find a person by their badge number, but you use their job title instead. You won’t find who you’re looking for!
The Crashing Scenario
Because of this mix-up, efx_channel_get_tx_queue() would return NULL (meaning “couldn’t find it!”). The calling code didn’t check if the result was NULL, and tried to use it anyway—boom: kernel panic or crash.
This bug could potentially be triggered by malicious traffic or simply bad luck with timing, causing a denial of service.
Vulnerable Code (Before Patch)
struct efx_tx_queue *tx_queue;
tx_queue = efx_channel_get_tx_queue(channel, tx_ev->txq_label);
...
do_something_with(tx_queue->...); // Crash if tx_queue is NULL
Why It’s Dangerous
When the function gets NULL but tries to use it like a valid pointer, the kernel can access memory it shouldn’t—causing an instant crash.
The Fix (Patched Code)
The fix, released in kernel versions 5.10.12, 5.4.95, 4.19.172, and 4.14.219, replaced the problematic line with direct lookup:
struct efx_tx_queue *tx_queue;
tx_queue = channel->tx_queue[tx_ev->txq_label];
// Now tx_queue is always properly found (or checked for)
This way, the label is used as an array index, so the correct TX queue is accessed every time.
Full Patch:
You can see the change in the official patch.
Proof-of-Concept: Can You Exploit It?
This bug is mostly a DoS (Denial of Service) risk. If you have local access (or root on a VM/host using this device), you could flood the network card with strange traffic to make the buggy code path run, possibly crashing the host.
A simple reproduction (for researchers)
1. Use an affected kernel on a physical/VM with a Solarflare card.
System could crash when the driver mishandles the TX event.
But a safe, direct exploit to “take over” the system doesn’t exist because it “just” crashes the kernel. That’s still bad if you care about uptime!
Systems with Solarflare NICs and kernels prior to the 2021 patch.
- Public servers, cloud platforms, VMs—if you don’t apply updates, attackers could crash your machine.
If you use Ubuntu, Red Hat, Debian, SUSE, etc., and have an sfc network card, check your kernel version and update right away!
References
- CVE Report: CVE-2021-46948
- LKML Patch Thread
- Official Patch Source
- Solarflare 'sfc' Driver Docs
Closing Thoughts
While not every kernel bug lets hackers take over the system, even crashing a server is serious business. CVE-2021-46948 is a good example of how subtle mix-ups—even in device drivers few people notice—can lead to real problems for users and companies.
Always update your kernel and drivers. Security is in the details!
If you found this helpful, share it with your sysadmin team or fellow Linux users. Stay safe and keep your machines patched!
Timeline
Published on: 02/27/2024 19:04:06 UTC
Last modified on: 04/10/2024 20:14:23 UTC