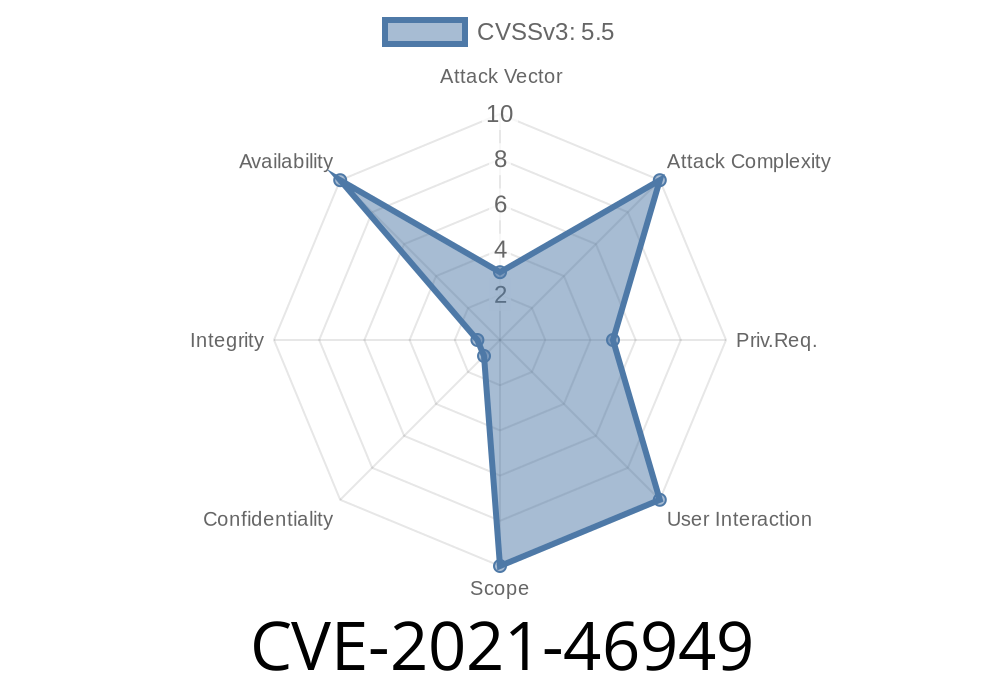
Linux operates at the core of much of the world’s infrastructure—for everything from cloud servers to Android phones. This makes kernel vulnerabilities a key target for attackers and a top concern for system administrators. In this exclusive long read, we’ll break down CVE-2021-46949, a vulnerability discovered and fixed in the “sfc” ethernet driver in the Linux kernel, focusing on the “farch: fix TX queue lookup in TX flush done handling” bug.
We’ll use plain language, share code snippets, reference original sources, and explain exploitability and patch details to help you understand both the risk and the solution.
What Is CVE-2021-46949?
CVE-2021-46949 is a flaw in the “sfc” driver used for Solarflare network cards in Linux. Specifically, it’s in the part of the codebase responsible for flushing (cleaning up) transmission (TX) queues. Due to improper lookup of TX queues after flush completion, calling code could receive a NULL pointer and cause the kernel to panic, leading to denial of service (crash).
Technical Explanation
- The function efx_get_tx_queue() was being called with an argument that wasn’t what the function expected.
The function expected a TXQ type, but the code was giving it a TXQ instance number.
- This mismatch could cause efx_get_tx_queue() to return NULL—and when code later tried to use that pointer as if it was valid, the Linux kernel would crash.
How Is It Triggered?
Any operation that causes the TX flush-done handler to be invoked with an unexpected or out-of-range queue identifier (qid) could trigger buggy lookup logic, causing a crash.
Vulnerable Code
Here’s a simplified code snippet for illustration (not the real kernel code, just a demonstration!):
void sfc_tx_flush_done(unsigned int qid) {
struct efx_tx_queue *tx_queue;
// Vulnerable: Passing TX queue instance to a function expecting a TXQ type
tx_queue = efx_get_tx_queue(qid);
if (tx_queue == NULL) {
// Oops! tx_queue is NULL. Further use will crash the kernel.
pr_err("NULL tx_queue, panic is near!\n");
// Crash or kernel panic may occur here...
}
// ...normal use of tx_queue...
}
The Problem
Here, if qid is outside the expected range or is just misinterpreted, efx_get_tx_queue(qid) returns NULL. Any dereference or use of tx_queue from there will crash the kernel, resulting in denial of service.
Patch and Resolution
Developers identified this type-mismatch and replaced the function with one that properly resolves the TX queue from the instance number.
Fix Commit (from Linus Torvalds’ kernel source):
- tx_queue = efx_get_tx_queue(efx, qid);
+ tx_queue = &efx->tx_queue[qid];
In Easy English:
Instead of asking a function to “find a queue of a specific type,” the patch directly references the array of TX queues by its number, which matches how it’s being called.
This eliminates the possibility of getting a NULL from mismatched expectations.
Who’s at risk: Anyone using the sfc (Solarflare) ethernet driver on a vulnerable kernel.
- Triggered by: Malformed or malicious packets, or users with system-level access forcing edge-case handling in the queueing logic.
- Remote exploitation: Unlikely, unless the TX flush logic is somehow triggerable by remote payload. More likely, an unprivileged user or local process could cause a crash if hardware and permissions are in play.
Exploit Scenario
If an attacker can cause the driver to flush a TX queue using an invalid or malicious qid, the kernel code will try to operate on NULL, leading to an immediate kernel panic (crash). This can be used for denial-of-service on shared servers.
This is not believed to lead to privilege escalation or code execution, but could nonetheless allow an attacker to reboot a system they can reach.
Linux commit log (the fix):
Linux kernel CVE page:
https://nvd.nist.gov/vuln/detail/CVE-2021-46949
LKML (Linux Kernel Mailing List) Patch Discussion:
https://lore.kernel.org/all/161375307369.31768.14974774755109924025.stgit@james-osl-desktop/
What Should You Do?
- Update your kernel: If your system uses the sfc driver and is running an unpatched Linux kernel, upgrade to a version after February 2021 or later, where the fix is present.
- Check for vendor patches: Distributions will often backport fixes. Check Red Hat, Ubuntu, or your vendor’s advisories.
- Audit kernel logs: Look for suspicious panics related to sfc or TX queue handling, which could indicate exploitation attempts.
Conclusion
CVE-2021-46949 is a classic example of how even small logic mismatches—passing the wrong identifier type—can cause critical stability issues in a complex system like the Linux kernel. While not a “remote code execution” flaw, it makes crashing a Linux host significantly easier for anyone with access, and shows why module and driver testing are so important.
For sysadmins, kernel devs, or security analysts, routine kernel updates and hardware-aware security policy are your best defense—especially for server-grade hardware like Solarflare network cards.
Further Reading
- Linux kernel source - sfc driver
- Kernel panic basics: what happens when things go wrong?
*If you found this writeup useful, consider subscribing for more clear, exclusive deep-dives into real-world software security!*
Timeline
Published on: 02/27/2024 19:04:06 UTC
Last modified on: 04/10/2024 20:14:05 UTC