This can happen if a URL Filtering profile is configured to allow all URLs that start with example.com and a malicious user-controlled hostname (e.g. test.example.com) has been entered into the profile. Another example of this is when a URL Filtering profile is configured to block all URLs that start with example.com and a malicious user-controlled hostname (e.g. test.example.com) has been entered into the profile.
Conditions for Vulnerable Behavior
If the hostname is not malicious (e.g., it does not contain a path traversal sequence) then the URL Filtering profile should not be configured to allow all URLs that start with example.com, as this will cause an error in the URL filter and will result in an HTTP 404 response. If a malicious user-controlled hostname is entered into the profile, it can result in a security issue by allowing access to websites blocked by the URL Filtering profile.
Conditions That Could Cause Incorrect URL Filtering Results
The following conditions could cause incorrect URL filtering results.
On the server, all URLs that start with example.com are allowed to be accessed from a malicious user-controlled hostname without restriction.
The URL Filtering profile is configured to allow all URLs that start with example.com and the malicious user-controlled hostname has been entered into the profile.
There is a misconfiguration of a URL Filtering profile rule on the server in which there is no rule for the malicious user-controlled hostname (e.g., all URLs that start with example.com are blocked).
ID: 20220
IDS is an important part of any organization's security program. One of the most common tasks for a security professional or administrator is to ensure that your application or system is protected with a default deny profile policy. It's important to create policies that are strong and not too permissive, so that attackers cannot exploit vulnerabilities in your network.
IDS - important for security purposes
One of the most common tasks for a security professional or administrator is to ensure that your application or system is protected with a default deny profile policy. This task becomes even more critical when you consider that organizations have been targeted by targeted attacks on the web, mobile apps, and other digital platforms such as DNS and email. These targeted attacks can be highly damaging to an organization since they often result in information leaks, data breaches, identity theft, brand damage, and online reputation poisoning. This makes it even more important to protect all assets from being compromised by implementing strong IDS policies.
If you're still having trouble understanding how IDS works, here's some helpful information:
* What does IDS stand for?
IDS - stands for intrusion detection systems
* What does an IDS do?
An intrusion detection system (IDS) monitors network traffic and alerts administrators if suspicious activity is detected on a host machine. An IDS uses heuristics and signatures to detect malicious activity in network traffic between hosts. Some implementations also use behavioral analysis techniques
* How does it work?
IDSs monitor
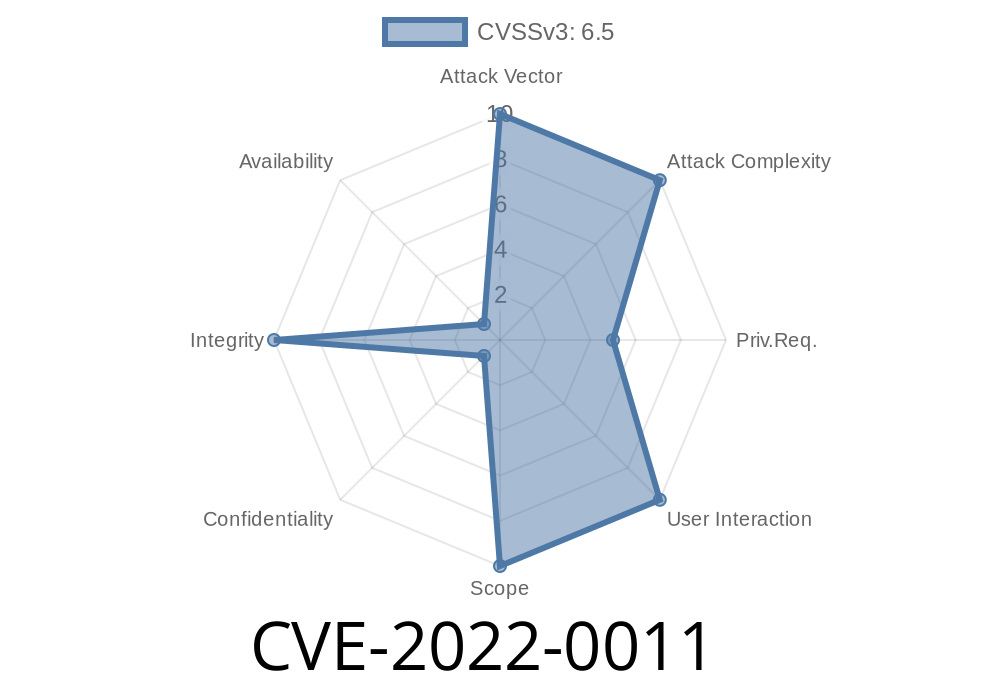
How do I verify if my site is affected by CVE-2022-0011?
You can verify if your site is affected by CVE-2022-0011 by using the following URL Filtering source IP address range:
192.0.2.1/32-255.
How do I know if I am affected?
Affected users will be unable to access the profile.
Timeline
Published on: 02/10/2022 18:15:00 UTC
Last modified on: 02/17/2022 13:41:00 UTC