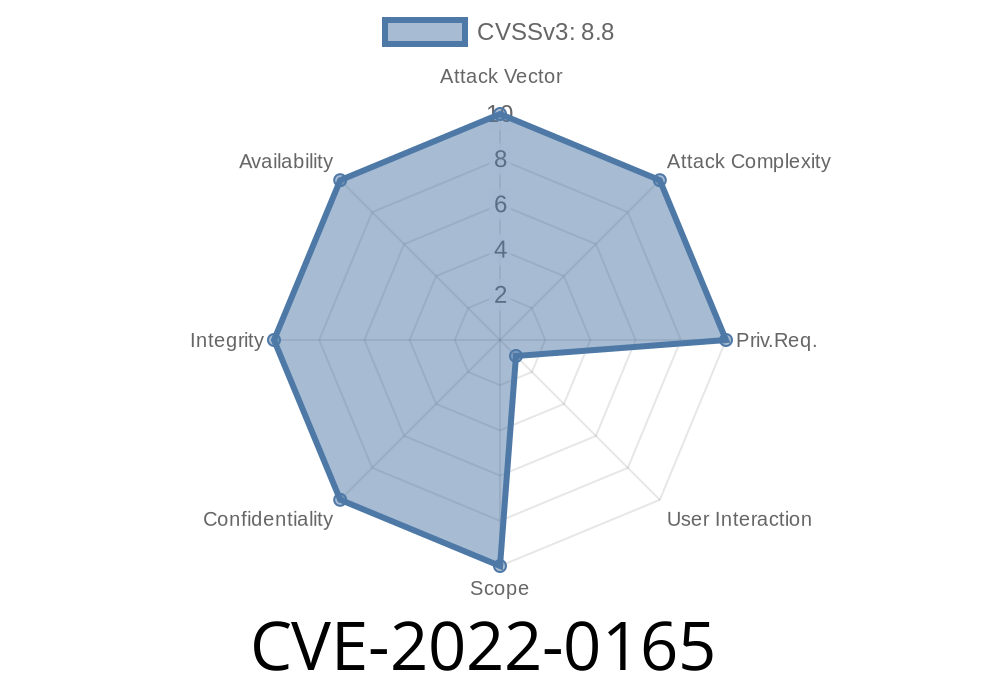
This results in a redirect loop where the user is redirected to the page they just edited but the page is not updated with the new data due to the id not being set. To fix this, you need to make sure you’re setting the id correctly on your custom post types. The Page Builder KingComposer WordPress plugin through 2.9.6 does not validate the id parameter before redirecting the user to it via the kc_get_thumbn AJAX action available to both unauthenticated and authenticated users. As a result, any value you set for this parameter will result in the redirect loop you saw in the previous section. You can avoid this issue by making sure the id you’re setting on your custom post types matches the URL you’re redirecting to.
WordPress Custom Post Type Attack Surface
The Page Builder KingComposer WordPress plugin has a large attack surface for the sake of customization. A lot of this is covered in the plugin’s documentation, but one area that deserves more attention is the use of custom post types.
Custom post types are becoming more and more popular with WordPress users as they provide a powerful way to create custom content types and manipulate how that content can be presented to visitors (beyond what is possible with traditional posts). It’s worth noting, however, that these custom post types can have an impact on your site’s security via their potential vulnerability to exploitation.
Command Line Interface (CLI)
The Command Line Interface (CLI) is the interface that you see when you type commands into your terminal. It allows you to run programs from the command line, which means it can be used for a variety of purposes, including managing WordPress sites and plugins.
Timeline
Published on: 03/14/2022 15:15:00 UTC
Last modified on: 03/21/2022 05:18:00 UTC