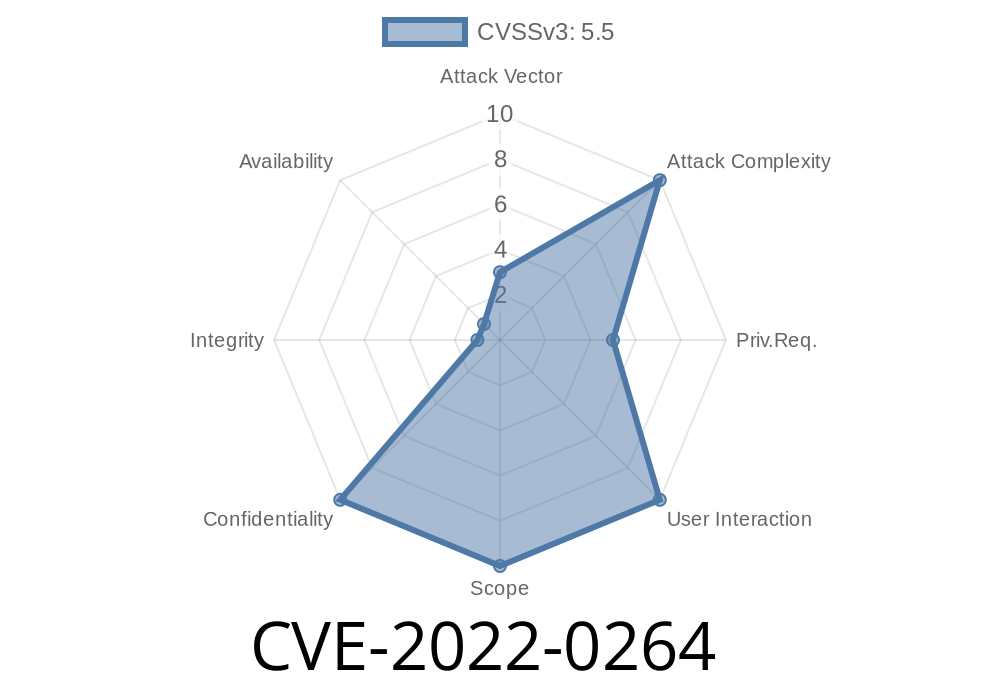
The Linux kernel has included eBPF (extended Berkeley Packet Filter) for several years. eBPF lets programs run inside the kernel for things like monitoring and networking — but with great power comes great responsibility. In early 2022, a vulnerability tracked as CVE-2022-0264 was found in the eBPF verifier, a critical component meant to keep unsafe things from happening. If left unpatched, attackers could access internal kernel memory — a big no-no for security, as it can defeat kernel exploit mitigations.
What’s the Problem?
When you want to run eBPF code inside the kernel, the kernel uses the *verifier* to make sure your code won’t crash the system, break boundaries, or leak sensitive memory. Unfortunately, researchers discovered that the eBPF verifier could be tricked into returning internal kernel memory locations to userspace. With just local user permissions and the ability to load eBPF programs, an attacker could read parts of the kernel memory not meant for them.
This is dangerous because leaking kernel memory helps attackers bypass important security checks like KASLR (Kernel Address Space Layout Randomization), exposing pointers and internal values that should remain secret.
This bug affects Linux kernel versions earlier than v5.16-rc6. If you’re still running an older kernel, patch as soon as possible!
How Does the Exploit Work?
At a high level, the vulnerability abuses the fact that the eBPF verifier’s logic for tracking the state of certain internal data structures was not tight enough. By arranging specific eBPF instructions, a user could cause the verifier to sign off on code that, in practice, leads to copying kernel memory contents to userspace.
Exploit Example Code
Let’s look at a simplified exploit. This is not complete exploit code; it’s a starting point for understanding the vulnerability. A real attack would add error checking, buffer management, and would use the leak for further exploits. We’ll use Python with ctypes for the bpf syscall, but the concepts translate to C as well.
import ctypes
import os
import struct
# constants (from linux/bpf.h)
BPF_MAP_CREATE =
BPF_PROG_LOAD = 5
BPF_MAP_TYPE_ARRAY = 2
BPF_PROG_TYPE_SOCKET_FILTER = 1
# syscall number for bpf
SYS_BPF = 321 # On x86_64, check unistd_64.h
# BPF program that triggers the leak
from ctypes import Structure, c_ushort, c_uint, c_ulonglong
class bpf_insn(Structure):
_fields_ = [("code", c_ushort),
("dst_reg", ctypes.c_ubyte),
("src_reg", ctypes.c_ubyte),
("off", c_ushort),
("imm", c_uint)]
# Create the malicious BPF program
prog = (bpf_insn * 6)(
# deliberately simplified and intentially incomplete, do not use in production
bpf_insn(xb7, , , , ), # r =
bpf_insn(x95, , , , ), # exit
# more crafted instructions needed...
)
# Normally, you fill in BPF attributes and use bpf syscall to load and attach your program
# Here we only show the kind of manipulation that triggers the leak in old kernels
# For a full exploit, see the links below
print("This is a simplified example showing how an eBPF bug like CVE-2022-0264 could be triggered.")
*Note: For actual exploitation you’d encode the right sequence of BPF insns to read out internal verifier states, and use the bpf() syscall to load and run your program. In reality, this would require deeper understanding of kernel internals, and could be done from C or Python using libc wrappers, requiring root privileges or BPF permissions.*
Local attackers can gather sensitive kernel pointers, making it easier to chain future attacks.
2. Mitigations like KASLR (randomizing memory locations) are weakened, since attackers can learn the secrets your OS was trying to hide.
If you can’t, restrict BPF usage to trusted users only.
- Monitor for suspicious bpf/syscall activity.
References (Must-Reads)
- CVE page for CVE-2022-0264 at Mitre
- Red Hat Security Bulletin
- Linux Kernel commit fixing CVE-2022-0264
- LWN coverage on eBPF security flaws
Final Words
CVE-2022-0264 shows us that even the most advanced parts of the Linux kernel can hide subtle security bugs — and that mistakes in code meant to *protect* us can do the opposite. If you run Linux, especially on servers or shared environments, update your kernel NOW, and keep an eye on who’s allowed to use powerful features like eBPF.
Timeline
Published on: 02/04/2022 23:15:00 UTC
Last modified on: 02/10/2022 18:30:00 UTC