Vim is one of the most popular text editors in the world. But like any software, it can have dangerous bugs. One such bug, CVE-2022-0361, is a critical heap-based buffer overflow issue found in the vim/vim GitHub repository before version 8.2. In this post, we'll break down what this vulnerability is, look at a code snippet that helps explain it, link you to original references, and talk about how attackers might exploit it.
What Is CVE-2022-0361?
CVE-2022-0361 is a heap-based buffer overflow vulnerability that existed in versions of Vim prior to 8.2. A buffer overflow happens when a program writes more data to a block of memory (the "buffer") than it actually allocates. On the heap, this can let attackers overwrite neighboring memory regions, often leading to a crash, arbitrary code execution, or making the system do things it shouldn't.
Official CVE entry:
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0361
Affected software: Vim (prior to 8.2)
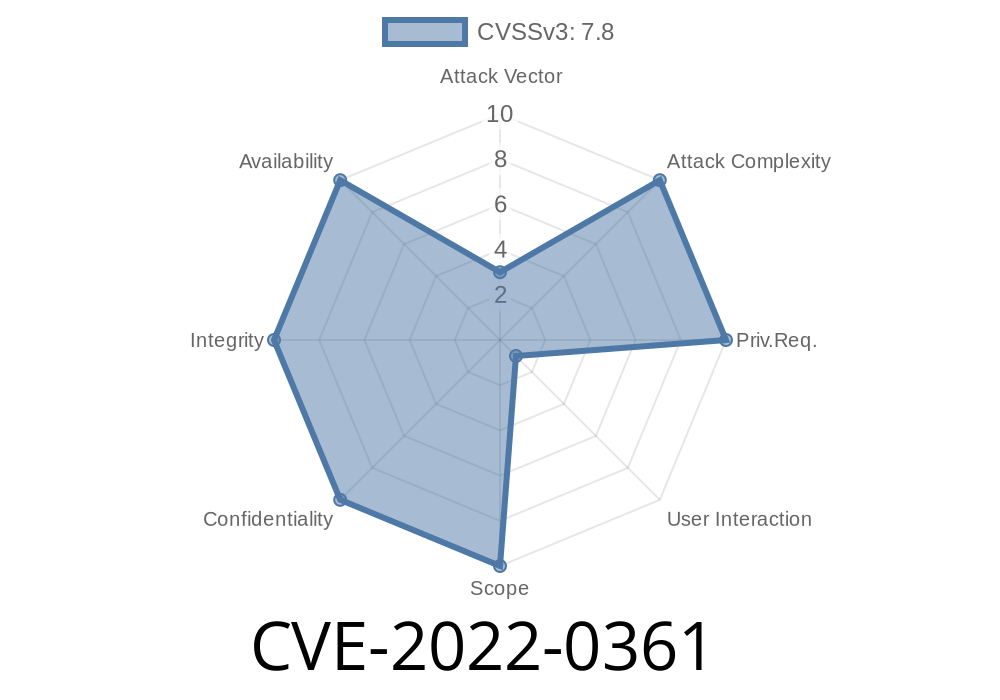
Severity: High
Where Did the Vulnerability Happen?
The vulnerability was reported and fixed in the vim/vim GitHub repository. According to this commit, the problem involved unsafe handling of certain commands that could be triggered with malformed input.
Code Snippet: Understanding the Issue
Suppose Vim fails to check buffer sizes while handling certain string operations. That’s what happened here. Here's a simplified version of code that could lead to the bug (note: not the actual vulnerable code, but it highlights the problem):
// Hypothetical buffer handling in Vim source code
void process_input(const char *input) {
char *buffer = malloc(256); // allocates 256 bytes
// Vulnerable: assumes 'input' is never longer than 256 bytes
strcpy(buffer, input); // Does not check length!
// ...do something with buffer...
free(buffer);
}
If an attacker controlled input and provided a string longer than 256 bytes, this would overflow the heap memory.
The Real Fix
After discovering the bug, the Vim developers patched it. Instead of strcpy, they used safer functions and checks.
strncpy(buffer, input, 255); // Copy only up to 255 bytes
buffer[255] = '\'; // Null-terminate to avoid overflow
How Can Attackers Exploit This?
In real-world attacks, an adversary could craft a specially-made file or input to Vim. When a vulnerable version of Vim opens or interacts with this file, the overflow is triggered, corrupting heap memory.
Exploit Example (Conceptual)
Suppose a malicious user creates a text file with a long, malformed line that Vim tries to process.
python3 -c 'print("A" * 300)' > evil.txt
Then someone opens this with a vulnerable Vim version
vim evil.txt
If Vim's processing code uses unsafe copying (like our earlier example), the memory overflow might allow code execution, letting the attacker run arbitrary commands as the user (or possibly with higher privileges, depending on setup).
Upgrade Vim: Make sure to use Vim version 8.2 or later.
- Validate Input: If you work on open source, always check memory handling and use safe string functions.
References
- NVD CVE-2022-0361 Detail
- GitHub vim/vim Commit Fix
- Red Hat Security Advisory
Conclusion
CVE-2022-0361 is a serious vulnerability in Vim that could let attackers gain control of your system using a simple buffer overflow. Always update to the latest software and be careful with files from untrusted sources, even if you're just editing text!
*Did you enjoy this breakdown? Let us know if you have questions about CVEs or want to see other vulnerabilities explained.*
Timeline
Published on: 01/26/2022 13:15:00 UTC
Last modified on: 08/26/2022 17:44:00 UTC