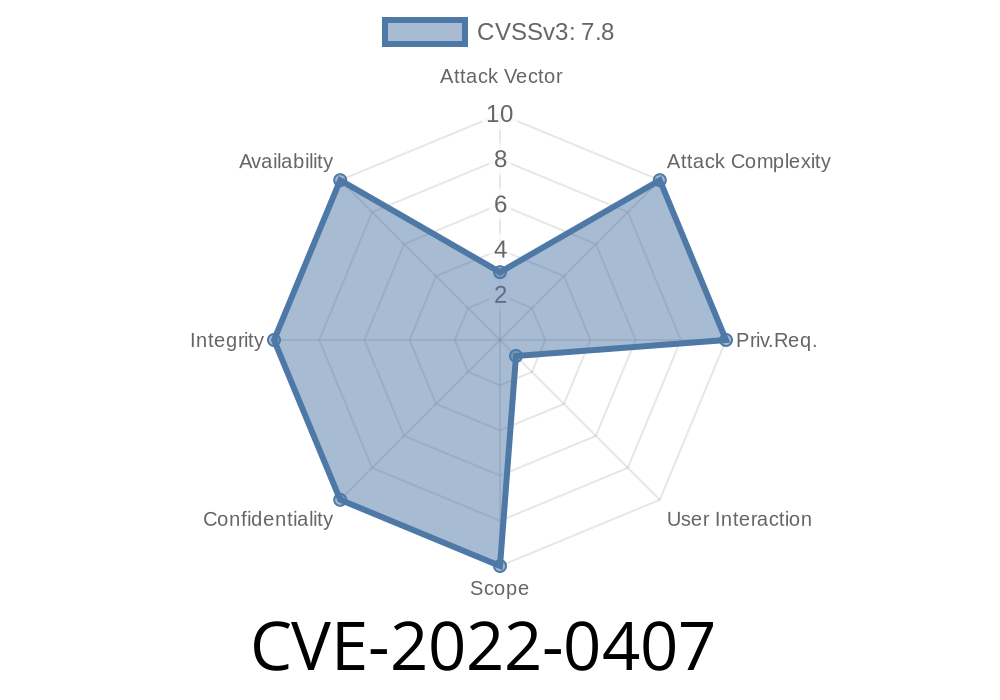
In early 2022, a vulnerability — CVE-2022-0407 — was discovered in the iconic open-source text editor, Vim. It relates to a heap-based buffer overflow, which can let attackers run arbitrary code or even take over your system if you open a malicious file.
In this post, we’ll walk you through what happened, show you relevant code snippets, and break down how an attack could work. At the end, you’ll find links to references and further reading. Whether you’re a developer, security enthusiast, or just a Vim user, this guide is written for you.
What Is Heap-based Buffer Overflow?
A buffer overflow occurs when a program writes more data to a buffer (a memory storage area) than it was supposed to. If the buffer is stored on the heap (dynamically allocated memory), it’s called a heap-based buffer overflow.
Why is this dangerous?
Because it lets attackers overwrite adjacent memory, possibly altering program control or forcing the program to execute attacker-chosen code.
Where's the Flaw in Vim?
The vulnerable code was in Vim, prior to version 8.2. Specifically, it happened when Vim processes certain crafted files (like a .vim script or modeline) containing long, malformed text. During operations like string copying, the program didn’t check if there was enough space in the heap-allocated buffer.
The patch for this bug is here:
https://github.com/vim/vim/commit/7ccafbfdd6c67363c5e3e8d0427fd6d7b1a2d3dc
Here’s a simplified example of the kind of dangerous pattern found in Vim’s C source
void vulnerable_copy(char *input) {
char *buffer = malloc(100);
strcpy(buffer, input); // NO length checking!
// ...
free(buffer);
}
If input is longer than 100 bytes, strcpy() will write past buffer and corrupt memory on the heap.
In Vim’s real code, the issue happened in functions handling modeline and substitute commands, where user-controlled strings could overrun allocated buffers.
Craft a Malicious File:
An attacker creates a text file with a specially formatted line. This line is much longer than the buffer Vim allocates and tricks Vim into copying it using unsafe string handling.
Payload Execution:
With careful memory layout, an attacker can overwrite adjacent structures or function pointers, sometimes resulting in arbitrary code execution. At the very least, it can crash Vim (Denial of Service).
A malicious file might look like this
<!-- This is pseudo-content: actual exploit strings are longer and more complex -->
vim: set modeline:
vim: set textwidth=99aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa:
Opening this file would trigger the vulnerable code path.
Update Vim! The fix was included in version 8.2.
- Download the latest version here.
References and Further Reading
- Official CVE report
- Vim Security Announcement
- GitHub Patch Commit
- What is a Heap-based Buffer Overflow? (OWASP)
Summary
CVE-2022-0407 was a classic heap-based buffer overflow in vim/vim before 8.2. Attackers could exploit this by tricking users into opening crafted files, which could lead to a crash or remote code execution. Keep your Vim updated and be wary of unknown files to stay safe.
If you want to dive deeper into the technical details, start by reading through the patch linked above — and maybe take a look at how modern C code manages buffers more safely today!
Timeline
Published on: 01/30/2022 14:15:00 UTC
Last modified on: 08/26/2022 17:35:00 UTC