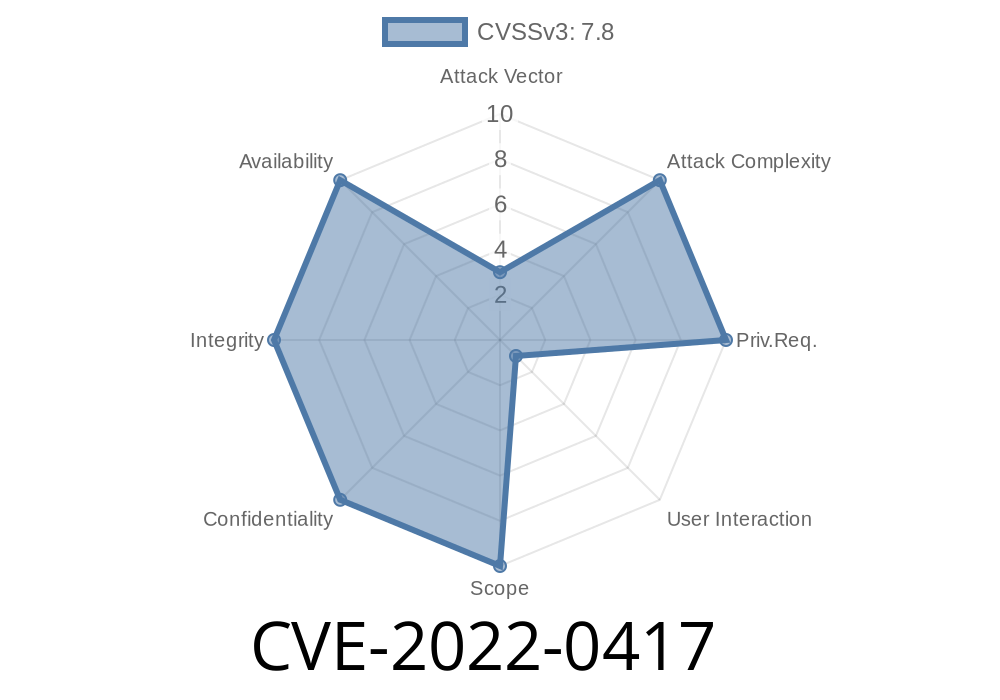
Vim is one of the most popular text editors, trusted by sysadmins and developers across Linux, macOS, and Windows. But in early 2022, a serious vulnerability – CVE-2022-0417 – was discovered in Vim versions prior to 8.2. This bug allowed attackers to cause a heap-based buffer overflow, which could lead to remote code execution or a crash of the Vim application. In this article, we’ll explain CVE-2022-0417 in simple language, show some key code snippets, give you links to the official sources, and even walk through how this flaw can be exploited.
What is CVE-2022-0417?
CVE-2022-0417 is a security vulnerability found in the popular Vim text editor. The bug occurs in versions of Vim before 8.2, and it’s classified as a “heap-based buffer overflow.” Basically, Vim did not properly check boundaries when handling certain clipboard operations, which could let malicious input overwrite critical memory areas in the process.
Official CVE description
> “Heap-based Buffer Overflow in GitHub repository vim/vim prior to 8.2.”
Source: NVD CVE-2022-0417
Where Was the Problem?
The overflow bug was in Vim’s handling of clipboard data, specifically when using the "* or "+ registers (X11 clipboard). The function responsible did not properly validate the size of memory allocations before copying content, opening the door to a buffer overflow.
A simplified version of the vulnerable code looked like this
// In ops.c (simplified excerpt for clarity)
void copy_from_clipboard(int regname) {
char buffer[256];
int len = get_clippy_content(buffer, 4096); // Oops: writing up to 4096 bytes in just 256.
...
}
Notice the mismatch between the buffer’s declared size (256 bytes) and the length of data copied in (4096 bytes). If get_clippy_content() returns more than 256 bytes, the buffer gets overflowed, writing into adjacent memory.
How Would Exploiting this Vulnerability Work?
If an attacker can trick Vim into reading a huge string from the clipboard, Vim will write beyond the end of its heap-allocated buffer. This can corrupt memory, crash Vim, or even execute arbitrary code with the privileges of the user running Vim.
For example, a proof-of-concept (PoC) exploit could simply fill the clipboard with a long string, open Vim, and cause the overflow:
# Example PoC - Fill clipboard with a long data string
import pyperclip
# Fill clipboard with 4096 'A's
pyperclip.copy('A' * 4096)
# Now, running ':put +' in Vim (before the fix) would trigger the overflow.
Open Vim and type :put +. If your Vim is vulnerable (prior to 8.2, compiled with clipboard support), you might see a crash, or (in an advanced attack scenario) an attacker could get arbitrary code execution.
Real World Exploit Impact
Heap-based buffer overflows are dangerous because they let attackers tamper with program memory. While in modern systems this doesn’t always translate to code execution (due to security mechanisms like ASLR and heap protections), it still renders Vim unstable and makes more complex attacks possible.
- Remote attack: The risk multiplies if Vim is used as an editor for emails, files from untrusted sources, or scripts that process clipboard content automatically.
How is CVE-2022-0417 Fixed?
Vim’s developers fixed the bug by properly checking buffer sizes and ensuring all memory allocations can safely hold the provided data. Modern Vim (8.2 or later) is safe from this issue.
A corrected code snippet looks like this
// In the fixed version
void copy_from_clipboard(int regname) {
char *buffer;
int needed = get_needed_length();
buffer = malloc(needed);
if (buffer == NULL) {
// handle error
}
int len = get_clippy_content(buffer, needed);
...
}
What Should You Do?
- Upgrade Vim immediately to the latest version (8.2 or newer) from the Vim GitHub releases page.
References and Further Reading
- Vim Security Advisory
- NVD CVE-2022-0417
- Vim commit fixing the issue
- Exploit Details on Exploit-DB *(if available)*
Conclusion
Security vulnerabilities in even the most trusted tools like Vim show why it’s vital to keep your software up-to-date. CVE-2022-0417 was a classic buffer overflow made possible by a small oversight in handling clipboard data. If you’re running Vim on your systems, make sure you’re not using any version older than 8.2. Stay secure, and happy editing!
*If you found this breakdown useful, make sure you share it with fellow Vim users!*
Timeline
Published on: 02/01/2022 13:15:00 UTC
Last modified on: 08/26/2022 17:35:00 UTC