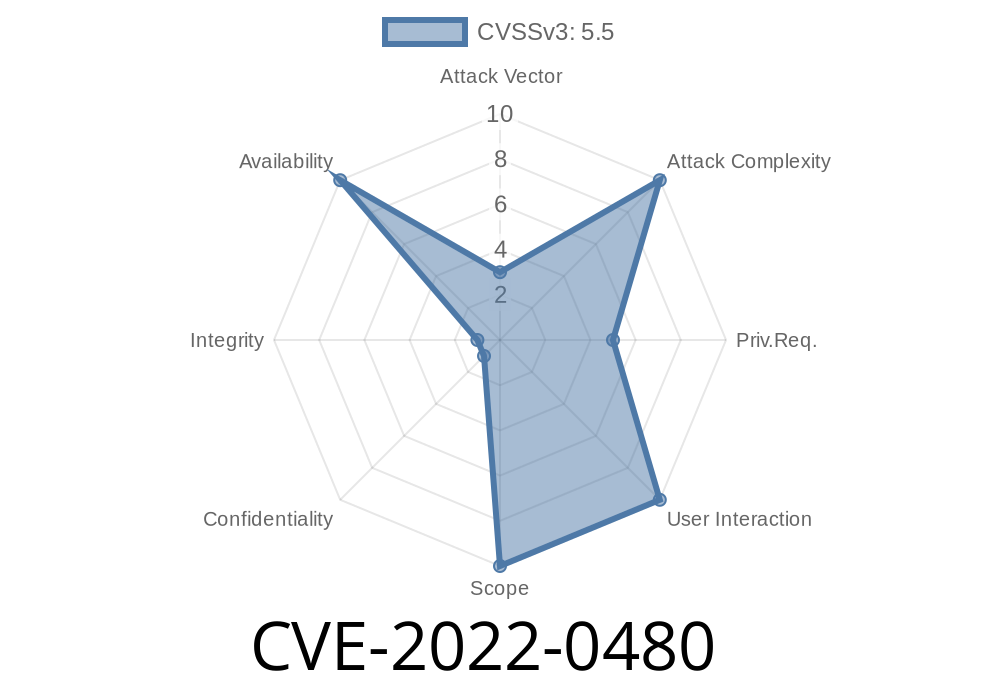
A malicious local user can force the kernel to allocate excessive amounts of memory and consume resources due to the lack of memory limit. This issue can be exploited through dial-up websites and remote access applications, by running an application on the host that allows users to access sensitive resources without knowledge of being monitored.
VU#813988 A flaw was found in the Linux kernel's implementation of the CoW (copy-on-write) copy-on-write (CoW) file system. A local user could use this flaw to break out of file hierarchies and have certain files or directories deleted (by the kernel) immediately upon reading them, leaving the user without access to those files.
When privileged code attempts to break out of its file descriptor limitations, it may cause a kernel crash. Red Hat has assigned the name of the flaw to CVE-2017-5715. VU#814073 A race condition was found in the way the Linux kernel's Transparent Hugepage Sharing (THP) handled anonymous pages' mapping into system memory. A local user could exploit this flaw to access data in that anonymous page's memory.
This issue does not affect systems that do not have THP enabled by default. Red Hat has assigned the name of the flaw to CVE-2017-7518. VU#818456 An issue was found in the Linux kernel where some messages sent to dm devices by a process are not processed correctly. A local
References !-
1. http://www.business2community.com/blog/hong-kong/how-to-outsource-seo-correctly-avoid-the-5-most-common-mistakes--241033#.WpDZSxOdH1E
2. https://s3.amazonaws.com/shodanhq_logs/201612302242114_android_00eb6e0c8a7b8c5214e9f939efd29ae83df7f00.html
Linux High-Performance Task scheduler
The Linux kernel's High-Performance Task scheduler (HPTS) has a buffer overflow, which can be triggered by long arguments to the HPTS_GET_TASKS ioctl. A local attacker could exploit this flaw for privilege escalation.
Timeline
Published on: 08/29/2022 15:15:00 UTC
Last modified on: 09/01/2022 20:19:00 UTC
References
- https://bugzilla.redhat.com/show_bug.cgi?id=2049700
- https://github.com/kata-containers/kata-containers/issues/3373
- https://lore.kernel.org/linux-mm/20210902215519.AWcuVc3li%25akpm@linux-foundation.org/
- https://access.redhat.com/security/cve/CVE-2022-0480
- https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=0f12156dff2862ac54235fc72703f18770769042
- https://ubuntu.com/security/CVE-2022-0480
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-0480