This vulnerability was discovered by a Redis contributor and resulted in a CVE assignment. Redis is not the only vulnerable piece of software. In fact, all major databases are at risk of remote code execution. This is due to the fact, that many of these databases, when relying on external libraries for code handling, lack of adequate input sanitization and failure to validate the source of input results in remote code execution. Redis is not the only database affected by this issue. All major databases are at risk of remote code execution. We’re going to explore the details of this issue and discuss the steps you can take to protect your database and application against it. Redis is a key-value data store, often compared to memcached or MongoDB. Redis is often deployed in large scale applications as caching layer. Redis is often deployed in large scale applications as caching layer.
Overview of Remote Code Execution in Redis
It has been reported that Redis is vulnerable to remote code execution, which is a result of an input validation error. This vulnerability was discovered by a contributor and resulted in a CVE assignment. Redis is not the only vulnerable piece of software. In fact, all major databases are at risk of remote code execution. This is due to the fact, that many of these databases, when relying on external libraries for code handling, lack of adequate input sanitization and failure to validate the source of input results in remote code execution.
Remote Code Execution in Redis
Redis is not the only database affected by this issue. All major databases are at risk of remote code execution. Remote code execution occurs when an attacker sends a malicious response to a request from the server and can be triggered by sending crafted input to the application.
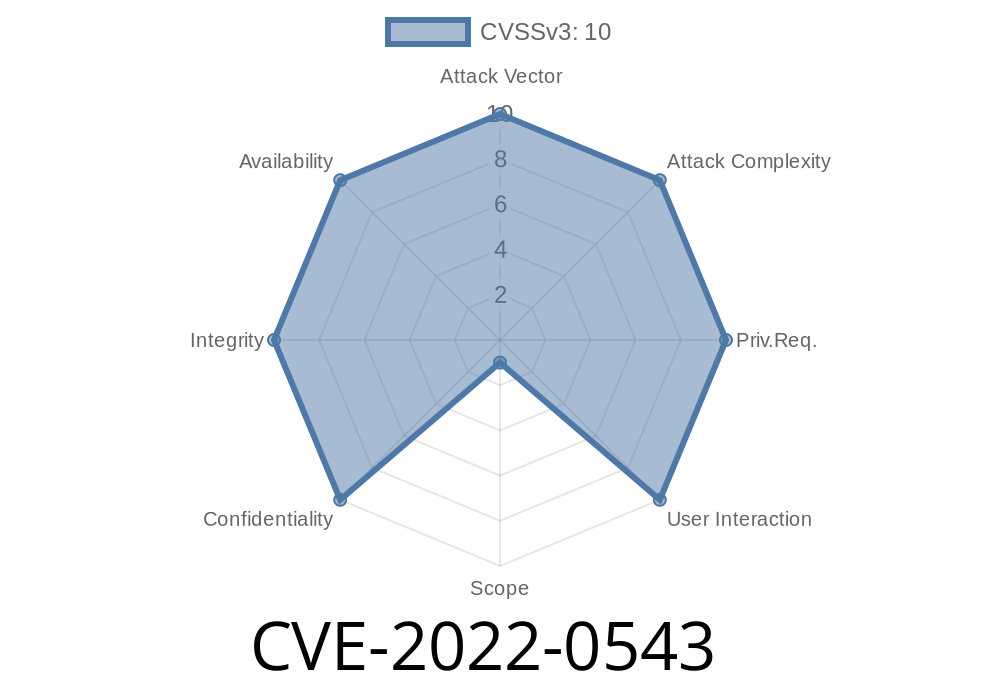
The vulnerability in Redis, CVE-2022-0543, is caused by a flaw in how memory is allocated for buffers within Redis. When using the command line utility redis-cli, it’s possible to send an arbitrary value as input that can result in remote code execution on the server. This was discovered by one of Redis contributors, who reported it to the team on October 28th, 2018.
Overview of Redis Remote Code Execution Vulnerability
The vulnerability was discovered by a Redis contributor and resulted in a CVE assignment. Redis is not the only vulnerable piece of software. In fact, all major databases are at risk of remote code execution. This is due to the fact, that many of these databases, when relying on external libraries for code handling, lack input sanitization and failure to validate source of input results in remote code execution.
Remote Code Execution in Redis
In order to exploit this vulnerability, attackers need to make a specially crafted request. The attack will work even if no authentication is required.
Timeline
Published on: 02/18/2022 20:15:00 UTC
Last modified on: 06/05/2022 02:35:00 UTC
References
- https://bugs.debian.org/1005787
- https://www.debian.org/security/2022/dsa-5081
- https://www.ubercomp.com/posts/2022-01-20_redis_on_debian_rce
- https://lists.debian.org/debian-security-announce/2022/msg00048.html
- https://security.netapp.com/advisory/ntap-20220331-0004/
- http://packetstormsecurity.com/files/166885/Redis-Lua-Sandbox-Escape.html
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-0543