This issue was fixed in version 2.6.2, released on December 20, 2017. In the latest version, 2.6.5, released on March 27, 2018, the developer removed all inline event handlers. We recommend upgrading the plugin to version 2.6.2 or higher as soon as possible. If you cannot upgrade the plugin, you can remove the inline event handlers from the source strings to prevent XSS.
Description:
The vulnerable code is when the developer has inline event handlers in the source strings. In other words, the developer has not taken any precautions to make sure that data sent to the inline event handler is sanitized before it is used. This leaves the possibility of an XSS vulnerability where users can inject harmful scripts into your site's HTML and JavaScript.
Summary
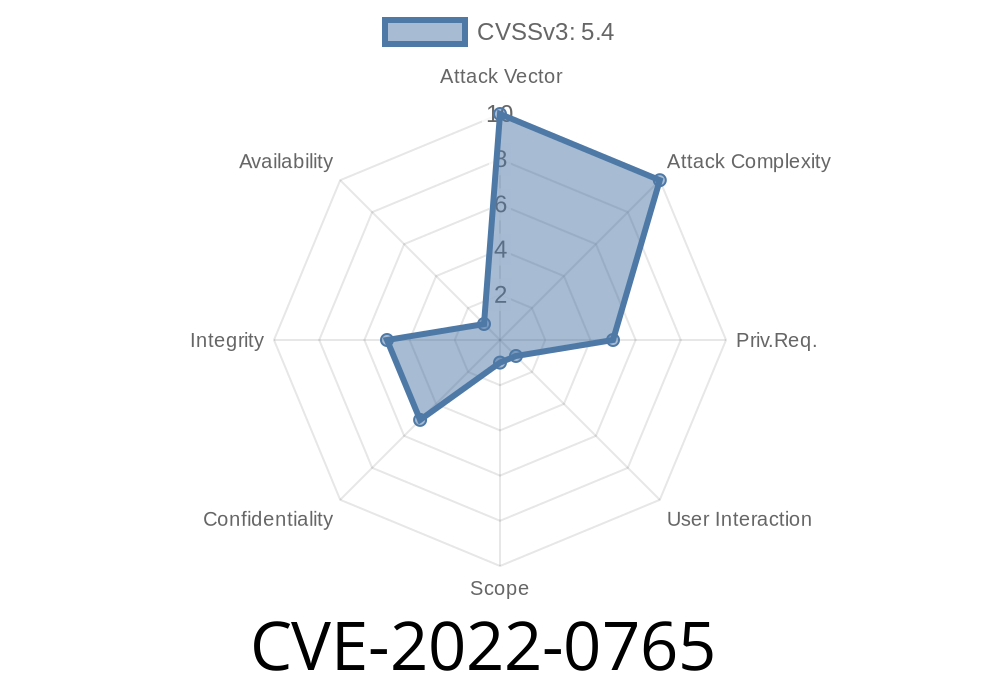
An XSS vulnerability was found in the 'WooCommerce' plugin. By exploiting this vulnerability, you can steal data from a server by sending an HTTP request. The vulnerability was fixed in 2.6.5 released on March 27th, 2018 which removed all inline event handlers. We recommend upgrading to version 2.6.2 or higher as soon as possible. You can find out more information on how to remove the inline event handlers here: https://docs.woothemes.com/document/plugin-injection-protection-removal
The WooCommerce plugin has an XSS vulnerability that would allow hackers to steal data from your server by sending an HTTP request to the website's admin panel through input fields with malicious code present in them like "xss=1& xsrf=1". This issue was fixed in version 2.6.2, released on December 20th, 2017, and it is recommended that you upgrade your plugin as soon as possible if you cannot upgrade the plugin then you can use a tool like Tamperdata (or similar) to find and remove the inline event handlers to prevent exploitation of this vulnerability
Inline event handler vulnerability example
Description
The WordPress plugin Cross Site Scripting (XSS) Scanner was found to be vulnerable to XSS attacks.
It is possible for an attacker to post content on a WordPress website that would allow them to steal a users session cookies and execute javascript code in the context of the browser.
Timeline
Published on: 04/18/2022 18:15:00 UTC
Last modified on: 04/27/2022 00:07:00 UTC