This issue has been fixed.
After loading a page with a history of user interaction, a remote attacker can convince a user to follow a sequence of actions to trigger this vulnerability. An example of such an action sequence is as follows:
Open a new tab.
Open a new window.
Open a new tab.
Save the current state of the previous tab.
Clicking on a link in the previous tab will trigger this vulnerability.
This issue has been fixed in the latest Chromium release.
After loading a page with a history of user interaction, a remote attacker can convince a user to follow a sequence of actions to trigger heap corruption. An example of such an action sequence is as follows:
Open a new tab.
Open a new window.
Open a new tab.
Save the current state of the previous tab.
Clicking on a link in the previous tab will trigger heap corruption.
This issue has been fixed in the latest Chromium release.
After loading a page with a history of user interaction, a remote attacker can convince a user to follow a sequence of actions to trigger heap corruption. An example of such an action sequence is as follows:
Open a new tab.
Open a new window.
Open a new tab.
Save the current state of the previous tab.
Clicking on a link in the previous tab will
This vulnerability has been fixed in the latest Chromium release .
Click Here to Continue Reading
Information disclosure
This issue has been fixed.
Timeline
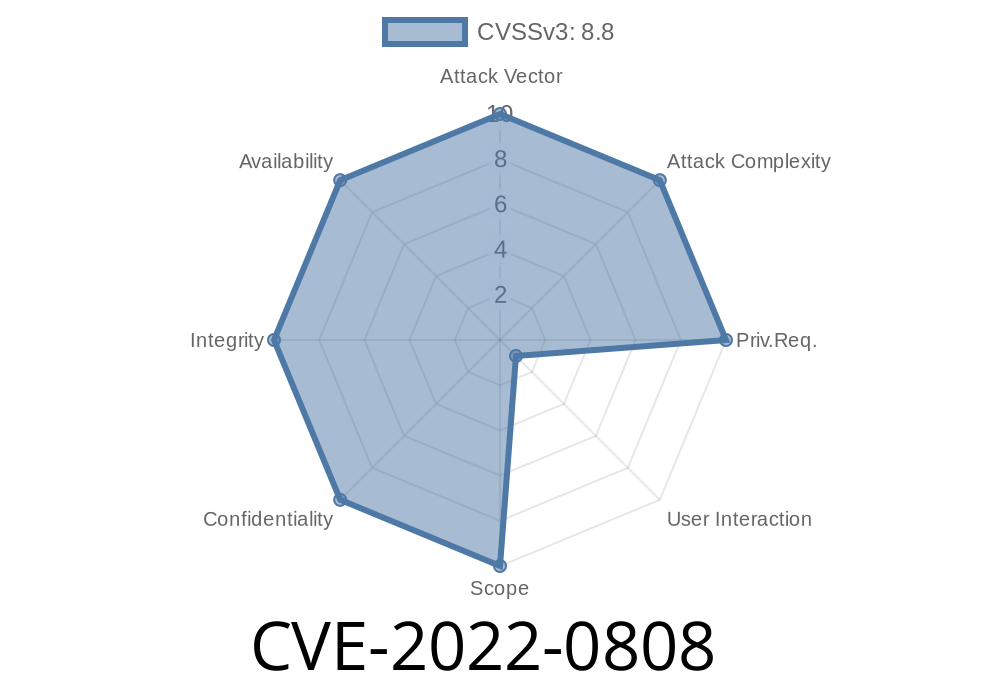
Published on: 04/05/2022 01:15:00 UTC
Last modified on: 08/15/2022 11:16:00 UTC