This issue results because of the NULL pointer dereference during handling of the ICMP table when it is operated upon by xt_conn_netfilter. A local user can take advantage of this issue to cause a denial of service (host/network/system hang) or corruption of data.
Another issue was found in the Linux kernel. This issue causes the system to ignore some invalid data (e.g. invalidaely formed TCP packets), resulting in a denial of service.
Lastly, a race condition was found in the Linux kernel. This issue results because of the unprivileged process being able to access information from other, privileged processes.
The user could exploit this flaw to cause a denial of service (system crash) or possibly gain privileges.
A flaw was found in the Linux kernel in the way the keyring (a component of the file system) handled user-created keys. A local user could create keyring-stored data in an arbitrary way, causing a file system corruption.
A race condition was found in the way the Linux kernel’s virtual memory implementation handled request from the virtual to the physical memory mapped to theio devices. An unprivileged user in a guest operating system could possibly use this flaw to escalate their privileges inside the guest.
An out-of-bounds write flaw was found in the way the EXT4 file system’s i_version data structure was handled when performing write operations
Linux kernel: canaries and testing
The Linux kernel has a well-known flaw that can be used to bypass ASLR and make the system vulnerable to a local attack.
While this issue is mitigated by default in the latest Linux kernel, it can still be exploited if certain conditions are met.
Linux kernel (no CVE assigned yet)
A flaw was found in the Linux kernel’s virtual memory implementation. An unprivileged user may be able to gain elevated privileges.
As a result of this issue, an out-of-bounds write flaw was found in the way the EXT4 file system’s i_version data structure was handled when performing write operations.
Operating system level attacks
A race condition was found in the Linux kernel. This issue results because of a privileged process being able to access information from other, unprivileged processes. The user could exploit this flaw to cause a denial of service (system crash), or possibly gain privileges.
A flaw was found in the Linux kernel in the way the keyring (a component of the file system) handled user-created keys. A local user could create keyring-stored data in an arbitrary way, causing a file system corruption.
An out-of-bounds write flaw was found in the way the EXT4 file system’s i_version data structure was handled when performing write operations
Timeline
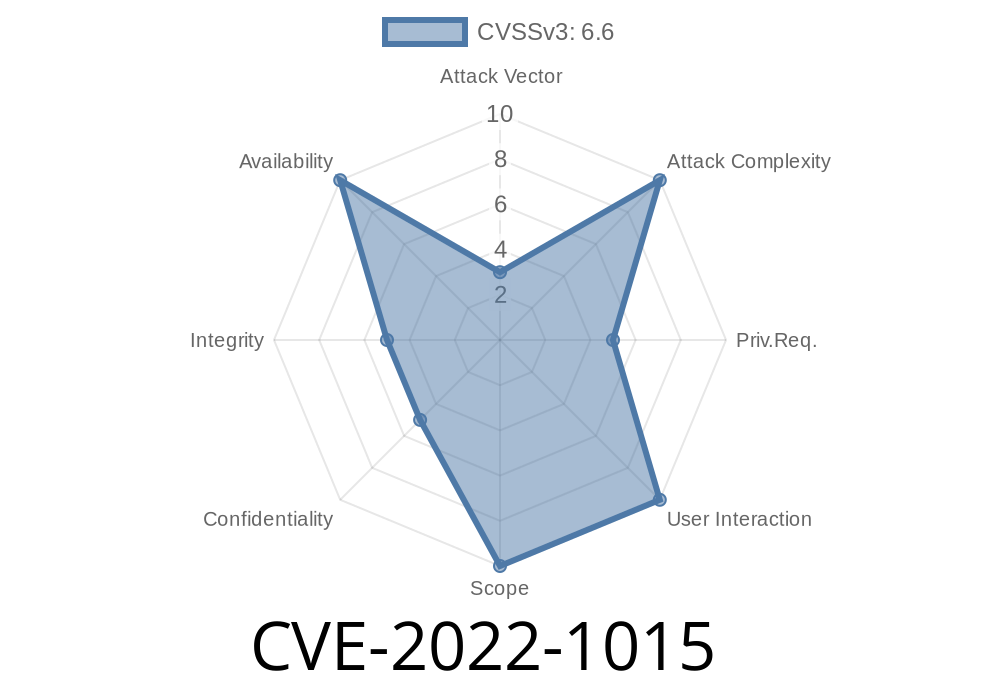
Published on: 04/29/2022 16:15:00 UTC
Last modified on: 08/25/2022 15:15:00 UTC