This flaw does not affect userspace or other vhosts. It was reported by Shachar Raina of VMware. A workaround is to update the page table entries manually.
An issue was found in the Linux kernel's FLAC audio cache daemon. On every audio interruption, FLAC's cache would purge old data and update the timestamp of the next chunk of audio. The interrupt handler did not check if the interruption was coming from a trusted source before updating the cache. As a result, an unprivileged local user could modify data in the cache, bypassing file-level sandboxes. This issue does not affect the majority of Linux distributions as FLAC is only used by a small number of distros. The issue was reported by James Simms of Red Hat. A fix was committed to the mainline Linux kernel in version 4.18.
An issue was discovered in the Linux kernel when handling ptrace system calls on a task with no vDS (virtual device state) capabilities active. Without the ability to mark a task as trusted using ptrace, an unprivileged local user could use an invalid ptrace system call to recover information from another task’s memory. This could be exploited by running a specially crafted program, allowing an attacker to obtain information from otherwise inaccessible processes. The issue does not affect Red Hat Enterprise Linux 7. Red Hat has not received any reports regarding the issue being exploited in enterprise environments.
In Red Hat Enterprise Linux 7, the
References a bug report
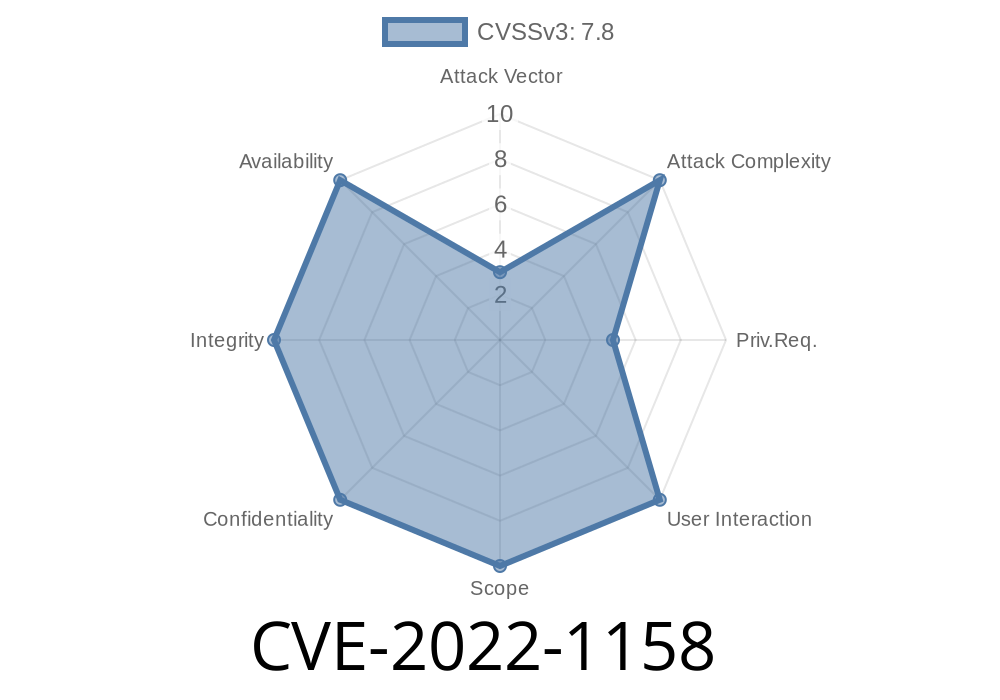
CVE-2022-1158
This flaw does not affect userspace or other vhosts. It was reported by Shachar Raina of VMware. A workaround is to update the page table entries manually.
An issue was found in the Linux kernel's FLAC audio cache daemon. On every audio interruption, FLAC's cache would purge old data and update the timestamp of the next chunk of audio. The interrupt handler did not check if the interruption was coming from a trusted source before updating the cache. As a result, an unprivileged local user could modify data in the cache, bypassing file-level sandboxes. This issue does not affect the majority of Linux distributions as FLAC is only used by a small number of distros. The issue was reported by James Simms of Red Hat. A fix was committed to the mainline Linux kernel in version 4.18.
An issue was discovered in the Linux kernel when handling ptrace system calls on a task with no vDS (virtual device state) capabilities active. Without the ability to mark a task as trusted using ptrace, an unprivileged local user could use an invalid ptrace system call to recover information from another task’s memory. This could be exploited by running a specially crafted program, allowing an attacker to obtain information from otherwise inaccessible processes. The issue does not affect Red Hat Enterprise Linux 7. Red Hat has not received any reports regarding the issue being exploited in enterprise environments.
What is the Red Hat Enterprise Linux 7 kernel?
The Red Hat Enterprise Linux 7 kernel is a standard kernel. It is used in Red Hat Enterprise Linux 7.
An issue was found in the Linux kernel's FLAC audio cache daemon. On every audio interruption, FLAC's cache would purge old data and update the timestamp of the next chunk of audio. The interrupt handler did not check if the interruption was coming from a trusted source before updating the cache. As a result, an unprivileged local user could modify data in the cache, bypassing file-level sandboxes. This issue does not affect the majority of Linux distributions as FLAC is only used by a small number of distros. The issue was reported by James Simms of Red Hat. A fix was committed to the mainline Linux kernel in version 4.18.
Security Fix: CVE-2022-1158
The vulnerability does not affect userspace or other vhosts. It was reported by Shachar Raina of VMware. A workaround is to update the page table entries manually.
References a blog post
If you want to grow your business, great search engine optimization (SEO) is a must. The challenge? Many small businesses don’t have the time, skills, or expertise necessary to handle everything that comes with a solid SEO strategy. From keyword research to content evaluation, from page optimization to internal linking, it’s easy for companies to end up with a generic web presence that doesn’t inspire engagement or drive conversions.
Timeline
Published on: 08/05/2022 17:15:00 UTC
Last modified on: 08/15/2022 23:01:00 UTC