This resulted in a local low privileged user being able to perform system tasks as the System account. No other users were affected by this issue. A patch for this issue was released by MA for Windows on Apr 29th 2018. This issue was discovered by Dawid Golunski of Udub. Red Hat would like to thank Dawid Golunski for reporting this issue.
Open Red Hat Enterprise Linux 6 or 7 Update 6 and receive this update to the MA for Windows component.
Important Notes About This Advisory
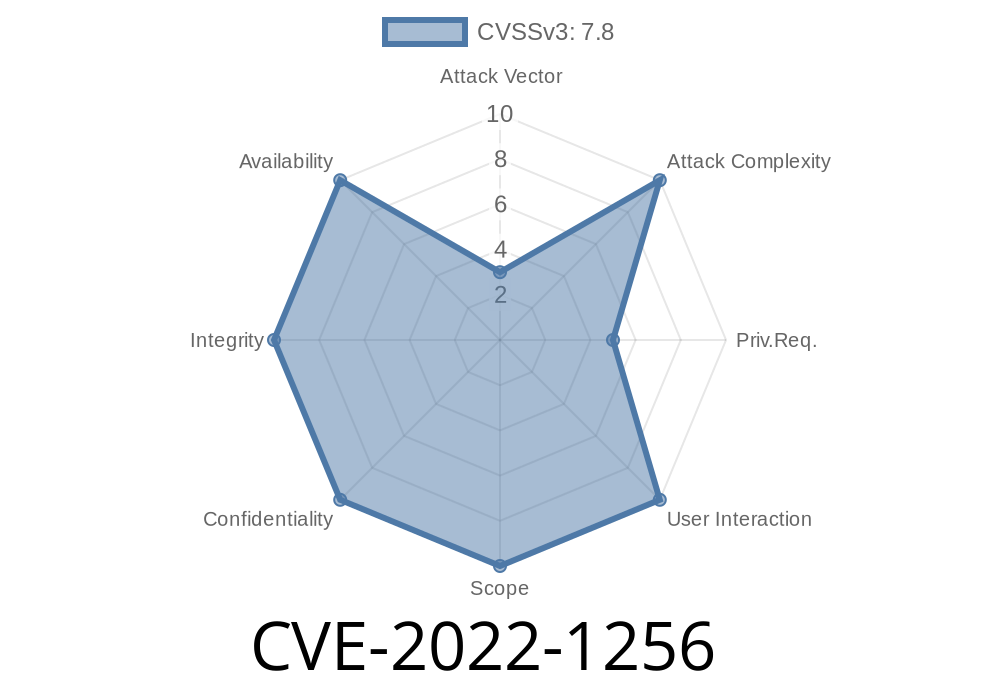
This advisory only addresses CVE-2022-1256 and it applies to MA for Windows. It does not affect System account privilege escalation issues in other products or software.
If you use the MA for Windows component, this issue has been resolved in Update 6 of Red Hat Enterprise Linux 6 or 7. If you are using a later version of Red Hat Enterprise Linux, upgrade to that version now.
Products Affected
All Red Hat Enterprise Linux 6 and 7 versions.
Ability to inject arbitrary code to Windows PowerShell
The vulnerability can be exploited remotely without authentication or interaction with the user.
Updates to the MA for Windows component
This update addresses a security issue. An attacker with local low privilege could gain access to the System account through a vulnerability in the MA for Windows component.
So, if you're using Red Hat Enterprise Linux 6 or 7 Update 6 and have this installed, it's time to install this update!
Timeline
Published on: 04/14/2022 15:15:00 UTC
Last modified on: 04/23/2022 02:22:00 UTC