This issue can be exploited with the help of a packet sniffing tool in a remote attack scenario. It is worth noting that this flaw does not allow a remote user to gain access to a user’s system. It is also worth noting that this flaw does not affect the majority of Linux users. However, it is recommended to update the system to fix this issue as soon as possible.
In May 2018, a flaw was found in the Linux kernel’s networking subsystem when handling TCP packet splits during network storms. This flaw could be exploited by a remote user to cause a denial-of-service (DoS) condition. Note that Red Hat has released an updated kernel that fixes this issue. It is recommended to update the system as soon as possible.
Check for the Version of Linux
The Linux kernel has a TCP packet splitting feature that takes care of packet fragmentation. This feature is used during network storms and when packets are too big for the network to handle. It is worth noting that this flaw does not allow a remote user to gain access to a user’s system. However, it is recommended to update the system as soon as possible.
In order to check the version of Linux installed on your system, open up a terminal window and use the “uname -r” command. If you see “3.8.0-6-amd64,” then you have the latest version installed on your machine and should update the system accordingly.
Checking for Linux Kernel Networking Stack Vulnerability
The Linux kernel is used in a wide variety of operating systems such as desktop and server operating systems. It is also used in embedded devices.
There was a vulnerability found in the Linux network stack that could allow a remote user to cause a denial-of-service (DoS) condition by sending many TCP packets.
This vulnerability was found on May 23, 2018 and fixed on May 24, 2018 with an update to the Linux kernel patch set.
It is recommended that all users update their systems as soon as possible to fix this flaw.
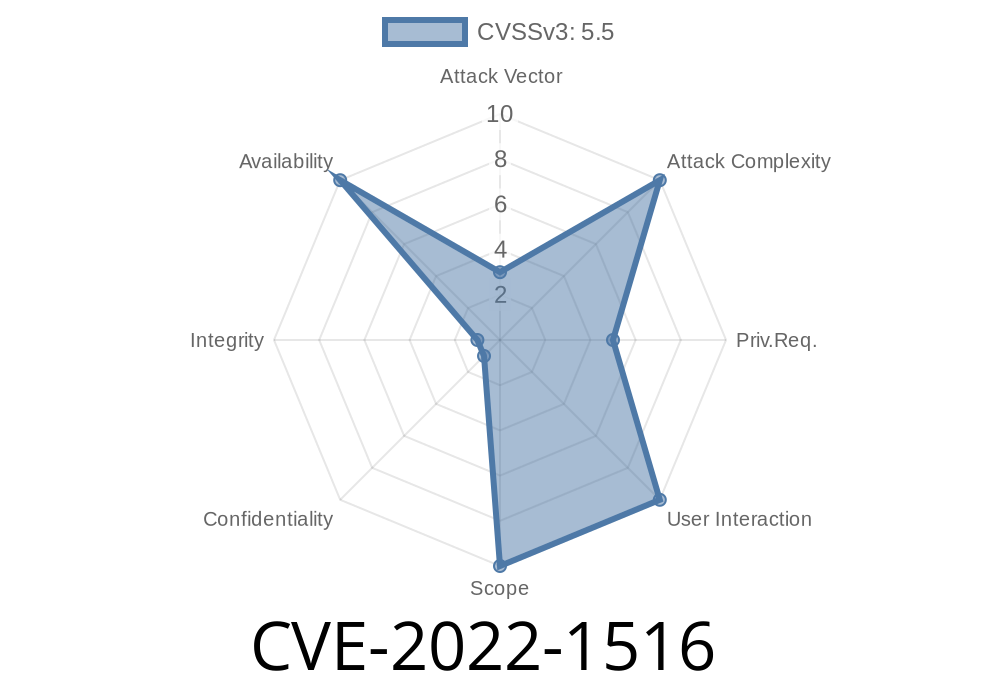
See more at: https://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-1516
How to check if my system is vulnerable to TCP SYN flood?
The following command can be used to check if your system is vulnerable to TCP SYN flood attack:
# cat /proc/net/bpf_jit/probability
If this number is 0, it means your system is not vulnerable to the TCP SYN flood attack. If the number is close to 1, it means that you are probably vulnerable and should update your system.
Timeline
Published on: 05/05/2022 15:15:00 UTC
Last modified on: 07/04/2022 11:15:00 UTC
References
- https://git.kernel.org/pub/scm/linux/kernel/git/netdev/net.git/commit/?id=7781607938c8
- http://www.openwall.com/lists/oss-security/2022/06/19/1
- https://lists.debian.org/debian-lts-announce/2022/07/msg00000.html
- https://www.debian.org/security/2022/dsa-5173
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-1516