The issue is caused by how unicode properties are handled during JIT. Due to the way JIT compiles regular expressions, the library will not check the full unicode value of the characters it uses. Instead, it will just check if the character is within the ASCII range. This is not a security issue, as JIT can be disabled in the regular expression to avoid it altogether. However, it is recommended to do so because it can cause issues with real-world usage of the library. Due to the nature of the issue, it is not possible to use the PCRE2 library with the JIT enabled. This means that users will not be able to checkout a regular expression from PCRE2 and see a JIT-compiled version of it. As a result, out-of-bounds reads can occur when valid user input is validated against the regexp.
How to upgrade to PCRE2 version 2.0.0
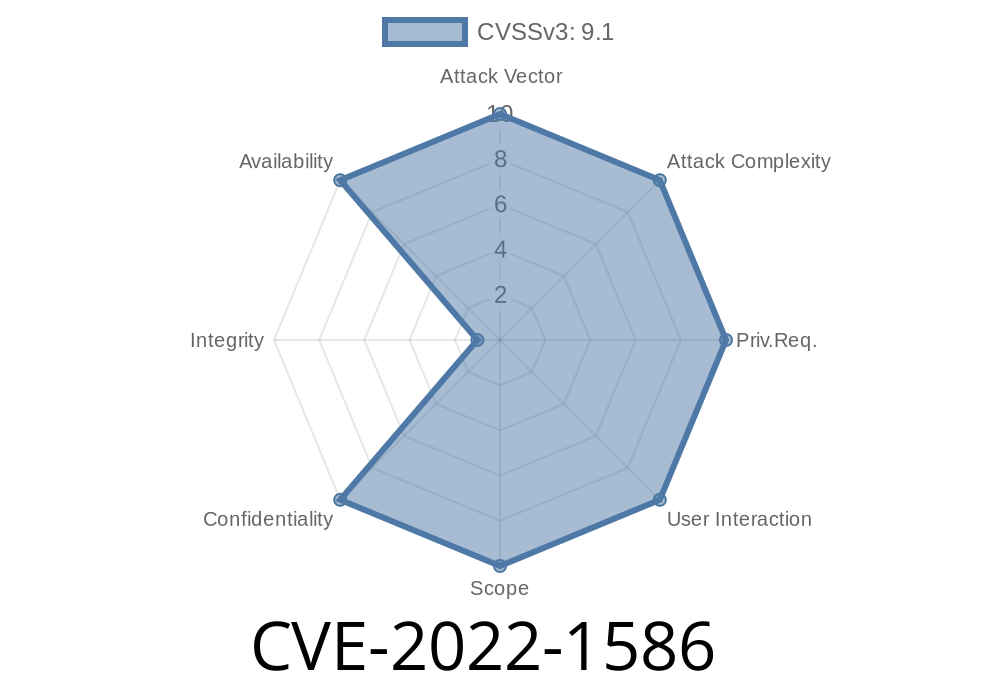
JIT and Unicode Property Issues with PCRE2
JIT can be enabled in PCRE2, which allows for a significant performance improvement. However, this comes with a huge trade-off: because PCRE2 does not check the full unicode value of the characters it uses and instead "checks" to see if they are within the ASCII range, out-of-bounds reads can occur when valid user input is matched against a regular expression.
The issue is caused by how unicode properties are handled during JIT compilation. Due to the way JIT compiles regular expressions, the library will not check the full unicode value of the characters it uses. Instead, it will just check if the character is within the ASCII range. This is not a security issue as JIT can be disabled in the regular expression to avoid it altogether. However, it is recommended that users disable JIT because it can cause issues with real-world usage of the library.
Fix code
// if the regular expression is compiled with JIT support
if (preg_jit) {
return len; // this will cause a read of out of bounds
} else {
return 0;
JIT Disabled
JIT is a feature of Regexp::JIT that enables the programmer to compile regular expressions into machine code. This can be done by using the JIT pragma in your regular expression, which will enable the compilation and give you access to optimizations. However, there is a downside to this convenience feature: it might cause security vulnerabilities.
In order to prevent this, you can disable the JIT compiler in your regular expression with the JIT_DISABLED pragma. It has been confirmed that PCRE2 does not support disabling the JIT compiler. This means that users will not be able to checkout a regular expression from PCRE2 and see a JIT-compiled version of it. As a result, out-of-bounds reads can occur when valid user input is validated against the regexp
Timeline
Published on: 05/16/2022 21:15:00 UTC
Last modified on: 06/02/2022 14:15:00 UTC
References
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/M2GLQQUEY5VFM57CFYXVIFOXN2HUZPDM/
- https://github.com/PCRE2Project/pcre2/commit/50a51cb7e67268e6ad417eb07c9de9bfea5cc55a,
- https://bugzilla.redhat.com/show_bug.cgi?id=2077976,
- https://github.com/PCRE2Project/pcre2/commit/d4fa336fbcc388f89095b184ba6d99422cfc676c
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/KAX7767BCUFC7JMDGP7GOQ5GIZCAUGBB/
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/DWNG2NS3GINO6LQYUVC4BZLUQPJ3DYHA/
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/JXINO3KKI5DICQ45E2FKD6MKVMGJLEKJ/
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-1586