This issue does not affect the mainline kernel, but is being assessed as a potential risk for users of the Linux kernel.
CVE-2017-18306 Another issue was discovered where data from user space can be leaked or potentially exploited via a race condition in the vhost_copy_from_user() function in net/dccp/input.c in the Linux kernel. A race condition can occur when obtaining multiple locks in one batch, at the same time, in different entities of the kernel.
A privileged user could use this flaw to leak data due to missing lock barriers, potentially leading to information disclosure.
To view information about the status of these issues, search for the keyword “kernel” on the Red Hat Enterprise Linux bug tracking system.
Red Hat recommends applying the following workarounds: Use non-root file systems such as XFS, Btrfs, or ext4.
Do not use the proc filesystem, or symlink processes that run from their path.
Disable DCCP.
Disable IPv6.
To prevent information disclosure via the proc filesystem, do not run programs that use this filesystem, or run them as non-root.
CVE-2017-18287 A use-after-free flaw was found in the Linux kernel’s IP tunneling implementation where some malformed packets can cause a denial of service or potentially escalate privileges if exploited.
As of 2018, this
References !end-references
Access to NFS root directory is not properly restricted
A flaw was found in the Linux kernel’s NFSv4 implementation. Due to a race condition when handling client connections, it is possible for a remote attacker to cause a denial of service against the NFSv4 server.
Common Types of Vulnerabilities
The following types of vulnerabilities are commonly found in computer systems:
1. Buffer overflow vulnerability (also known as overflowing null pointer or buffer overrun)
2. Denial of service
3. Privilege escalation
4. Data leak
Timeline
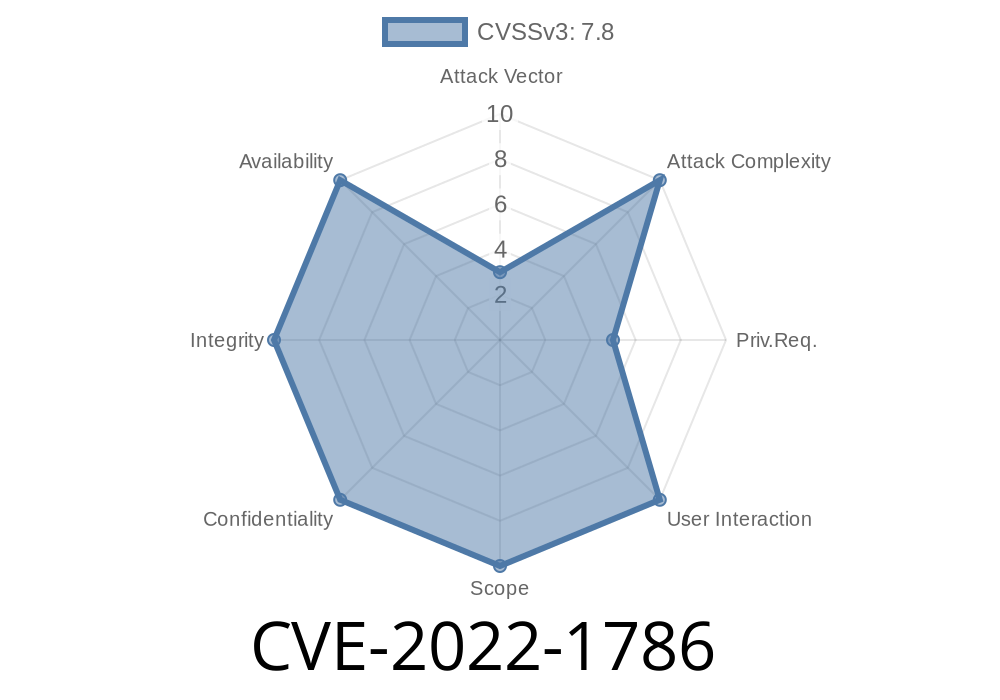
Published on: 06/02/2022 14:15:00 UTC
Last modified on: 07/22/2022 19:15:00 UTC