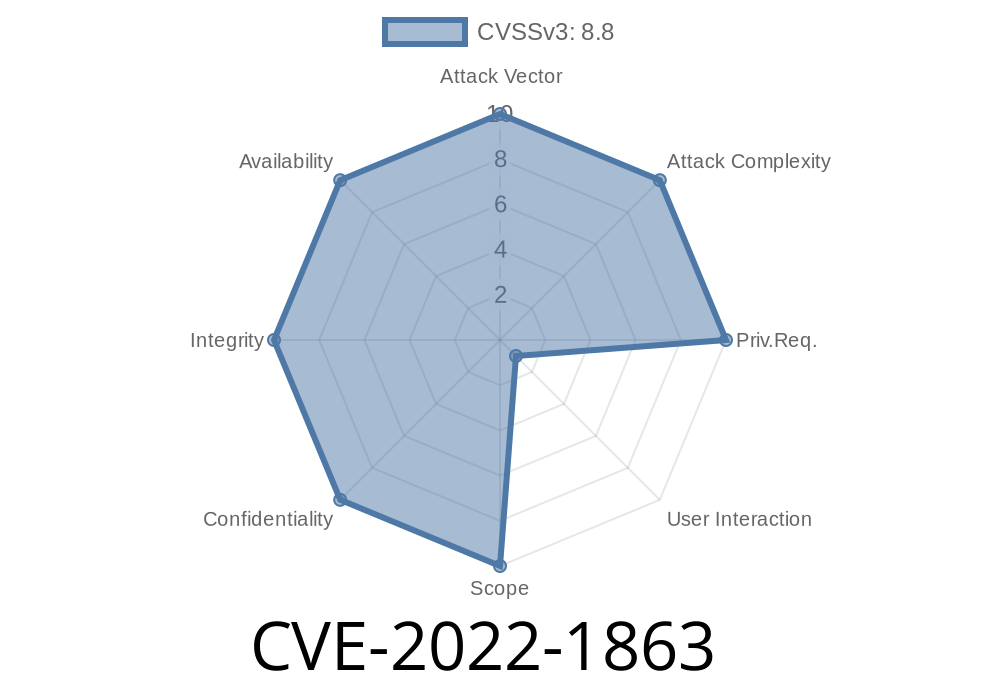
Exploitation resulted in a potentially exploitable crash and another potential vector for attack. Google Chrome prior to 102.0.5 prior to allowing insecure extensions to open web pages that they have access to via Navigation Timing caused issues with some third party extensions that could allow an attacker to inject arbitrary code into a privileged context.
An attacker could convince a user to install an extension from a malicious site and then deliver content that exploited this issue to run arbitrary code.
An example of such an attack is an email with a malicious PDF sent in an attachment.
An attacker could convince a user to install an extension from a malicious site and then deliver content that exploited this issue to run arbitrary code.
An example of such an attack is an email with a malicious PDF sent in an attachment.
An attacker could convince a user to install an extension from a malicious site and then deliver content that exploited this issue to run arbitrary code.
An example of such an attack is an email with a malicious PDF sent in an attachment.
An attacker could convince a user to install an extension from a malicious site and then deliver content that exploited this issue to run arbitrary code.
An example of such an attack is an email with a malicious PDF sent in an attachment. Google Chrome prior to 102.0
Mitigation Strategies
If you are using a third party extension, make sure to use the web browser's built-in extensions.
If you are using a third party extension, make sure to use the web browser's built-in extensions.
If you are using a third party extension, make sure to use the web browser's built-in extensions.
Installing a malicious extension could allow arbitrary code execution
A malicious extension could allow an attacker to inject arbitrary code into a privileged context.
An example of such an attack is an email with a malicious PDF sent in an attachment.
An attacker could convince a user to install an extension from a malicious site and then deliver content that exploited this issue to run arbitrary code.
Timeline
Published on: 07/27/2022 22:15:00 UTC
Last modified on: 08/15/2022 11:17:00 UTC