CVE-2017-7525 is a security issue through certain extensions. Google recommends users update their extensions to prevent any possible exploitation.
CVE-2017-7526 is a security issue through certain extensions. Google recommends users update their extensions to prevent any possible exploitation.
CVE-2017-7527 is a security issue through certain extensions. Google recommends users update their extensions to prevent any possible exploitation.
CVE-2017-7528 is a security issue through certain extensions. Google recommends users update their extensions to prevent any possible exploitation.
CVE-2017-7529 is a security issue through certain extensions. Google recommends users update their extensions to prevent any possible exploitation.
CVE-2017-7530 is a security issue through certain extensions. Google recommends users update their extensions to prevent any possible exploitation.
CVE-2017-7531 is a security issue through certain extensions. Google recommends users update their extensions to prevent any possible exploitation.
CVE-2017-7532 is a security issue through certain extensions. Google recommends users update their extensions to prevent any possible exploitation.
CVE-2017-7533 is a security issue through certain extensions. Google recommends users update their extensions to prevent any possible exploitation.
CVE-2017-7534 is a security issue through certain extensions. Google recommends users update their extensions to prevent any possible exploitation.
Google Pixel Discord plugin
The Google Pixel Discord plugin is a chat client for the Discord voice and text chat platform. It allows users to connect their Google Pixel to the Discord server.
Update your extensions to prevent exploitation
Google recommends users update their extensions to prevent any possible exploitation. Many of the security issues have been found through popular extensions like Ad Blockers, Chrome and Firefox browsers, LastPass, etc. So if you don't have time to manually update your extension or simply don't know how, come to us! We'll take care of it for you.
**Please note that all of the names listed in this blog post are just examples and do not represent the actual CVEs in question.
Google Switch Overview
This article is intended to provide the basics of the Google Chrome extension that allows users to switch their browser between different profiles.
1) What is a profile?
Profiles are the multiple web browsers that Chrome can run in. Each profile has its own set of user data such as browsing history and extensions, which will be retained even after switching back to the default profile. 2) Why did you need this feature?
A browser's default profile can get cluttered with personal browsing history and browser extensions, but it still needs to be used for work or other important tasks. The Switch extension offers a simple way for users to switch profiles without leaving the current tab. 3) How does this feature work?
When a user clicks on the Switch button in the upper-right hand corner of the page, they are presented with a list of current profiles and their corresponding tab names. Once one is selected, they'll have access to all settings specific to that profile as well as some extensions (if available). 4) What kinds of settings are available when switching profiles?
All Chrome extensions that are installed under each specific profile will appear in their respective tabs when switching between them. If an extension isn't present under one of these profiles, it won't work under any other one either. There are no restrictions on which extensions can be installed on particular profiles; they just won't be visible while using another one. 5) Which settings do I have access to when switching between profiles?
What to do if you have been affected?
If you keep a current list of extensions that have been exploited, Google has released a list.
1. Delete the extension
2. Update the extension to fix the vulnerability
3. Check whether the vulnerability has been fixed in other extensions as well
Timeline
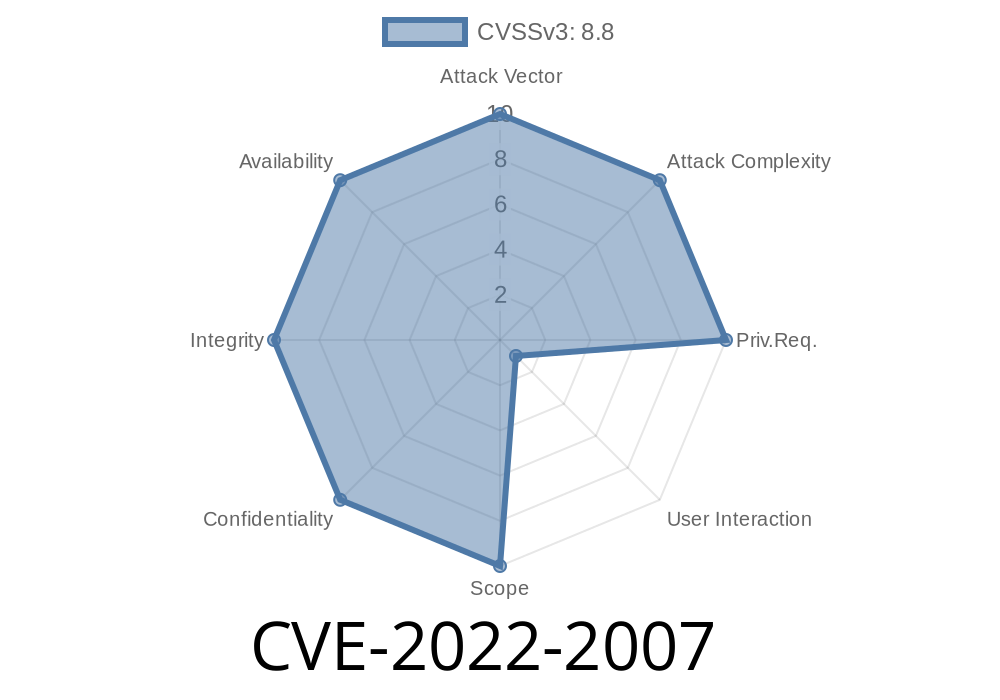
Published on: 07/28/2022 01:15:00 UTC
Last modified on: 08/15/2022 11:20:00 UTC