This issue was reported through Tipping Point’s bug bounty program. The researcher received USD 5,000 as a reward. Tipping Point offers bug bounty programs for many different vendors, including vendors of web browsers, web server software, operating systems, networking equipment, and more.
Windows Remote Code Execution Vulnerability
On February 8, Microsoft released a patch for a remote code execution vulnerability in Windows. This is a critical security flaw that could allow hackers to take control of an affected system without the user’s knowledge. The flaw affects all versions of Windows, including Windows 10 and Windows Server 2016.
This bug was reported to our program through Tipping Point’s bug bounty program. The researcher received USD 5,000 as a reward.
Summary of the Issue
This issue was reported through Tipping Point’s bug bounty program. The researcher received USD 5,000 as a reward. The researcher discovered a vulnerability in the internal private key generation that exposes all of the private keys generated from the public and private keys generated from the derived keys. Tipping Point offers bug bounty programs for many different vendors, including vendors of web browsers, web server software, operating systems, networking equipment, and more.
Microsoft Edge and Internet Explorer (CVE-2023)
The vulnerability was reported as CVE-2023. Microsoft Edge and Internet Explorer are the two browsers in question, so they are both vulnerable to a memory corruption vulnerability when rendering HTML pages. When a user views a website, this memory corruption vulnerability could allow an attacker to control the browser’s rendering of any HTML pages on the site.
In order to exploit this attack, an attacker would have to trick the user into browsing a website that is hosting malicious code or content that induces this memory corruption vulnerability.
Common Vulnerabilities and Exposures (CVE)
A common vulnerability exists when a developer fails to properly validate input in software.
This is one of the most common vulnerabilities that can be detected by software engineers before hackers exploit it.
Without proper validation, an attacker could cause the software to behave unexpectedly, exposing your company to potential compromise.
Detecting these vulnerabilities through code reviews and testing should help prevent hackers from exploiting them.
Timeline
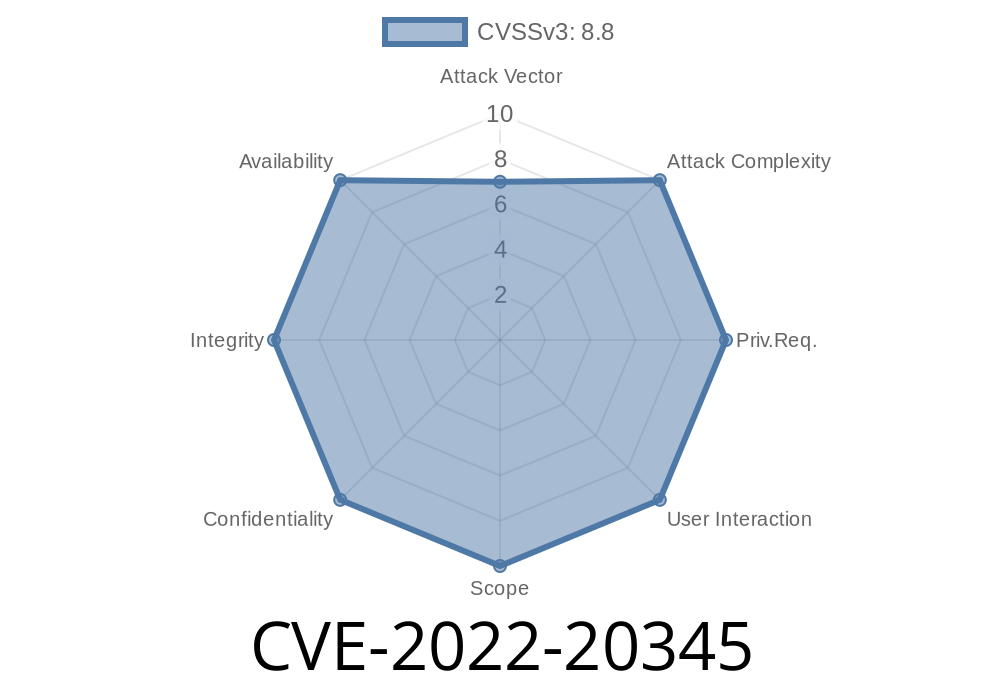
Published on: 08/10/2022 20:15:00 UTC
Last modified on: 08/12/2022 07:03:00 UTC