---
What is CVE-2022-20454?
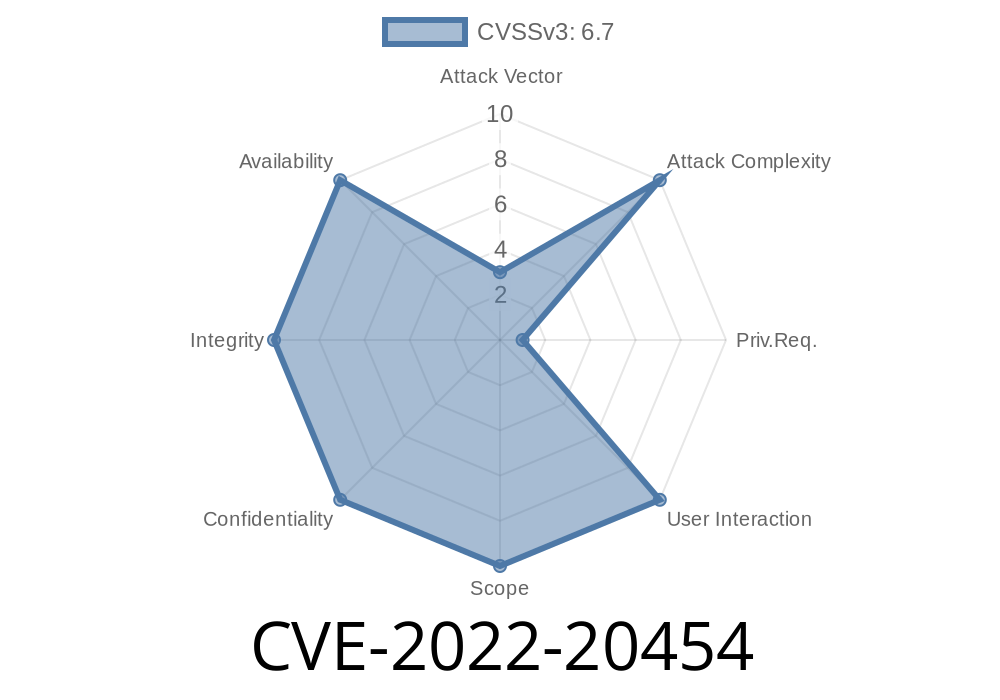
CVE-2022-20454 is a vulnerability found in Android’s device tree handling code (specifically, in the fdt_next_tag function in fdt.c). If exploited, this bug can allow a malicious app or process to gain higher privileges — up to System level — without requiring any user interaction. The vulnerability affects Android versions 10, 11, 12, 12L, and 13.
Exploitation: No user interaction required
- Original Android Bug ID: A-242096164
How Does the Vulnerability Work?
The bug lies in how the code parses the Flat Device Tree (FDT) binary. The function fdt_next_tag() is responsible for processing different “tags” within the device tree structure. Due to missing checks, it’s possible to trigger an integer overflow when calculating the size of the next tag. This can cause a subsequent out-of-bounds write, corrupting memory, and possibly leading to code execution with System privileges.
Let’s look at a simplified version of the vulnerable code.
Vulnerable Code Snippet (Simplified)
uint32_t fdt_next_tag(const void *fdt, int offset, int *nextoffset) {
// ... [other code]
int tag = fdt32_to_cpu(*(uint32_t *)((char *)fdt + offset));
int len = fdt32_to_cpu(*(uint32_t *)((char *)fdt + offset + 4));
int new_offset = offset + sizeof(uint32_t) * 2 + len;
// Missing check for integer overflow here!
*nextoffset = new_offset;
// ... [other code]
return tag;
}
What goes wrong?
- If len is very large, offset + sizeof(uint32_t) * 2 + len can overflow, wrapping around to a small value.
- Later, this offset is used to write data, potentially overwriting critical memory outside the intended buffer.
Step 2: When fdt_next_tag() processes the blob, integer overflow occurs.
- Step 3: Out-of-bounds memory is written, which can let the attacker overwrite sensitive structures or code.
Step 4: Attacker executes arbitrary code with System privileges.
No user interaction (like clicking or permissions) is required — just the ability to supply a malformed FDT file.
Proof-of-Concept (PoC) Overview
A full, working PoC would require a controlled Android environment and a deep understanding of the target process loading FDTs. However, the general technique is as simple as:
Pseudo-code
# FDT blob crafting (oversimplified)
fdt_blob = b''
fdt_blob += b'\x00\x00\x00\x01' # Valid tag
fdt_blob += b'\xFF\xFF\xFF\xFF' # len = xFFFFFFFF (very large)
# ... [rest of blob with controlled data]
Android Security Bulletin — Nov 2022:
Upstream Patch in AOSP:
NVD Entry:
How Was It Fixed?
The patch adds proper integer overflow checks before using the calculated offsets. If an invalid size is detected, processing stops and an error is returned, preventing the out-of-bounds access.
Mitigation and Recommendations
- Update your device. Make sure your Android phone or tablet is updated to the latest security patch (Nov 2022 or later).
Stay safe. Keep your Android updated!
Share or cite this article with a link to the original Android bug tracker (A-242096164) and Google's security bulletin for further details.
Timeline
Published on: 11/08/2022 22:15:00 UTC
Last modified on: 11/09/2022 16:31:00 UTC