On Cisco IOS XE Software, Tcl has its own virtual machine (VM) and cannot be used from a script or program. Tcl can only be used from a command line interface (CLI). Cisco IOS XE Software allows execution of Tcl scripts from the CLI. When executing a Tcl script, the following occurs: - The script is run by a Tcl interpreter - The script is run within the context of a process - The process runs with the privileges of the user that launched it - The script can only access the memory space of the process that ran it - The script cannot access memory space of the virtual machine that hosts the Tcl VM
Description of Vulnerable field
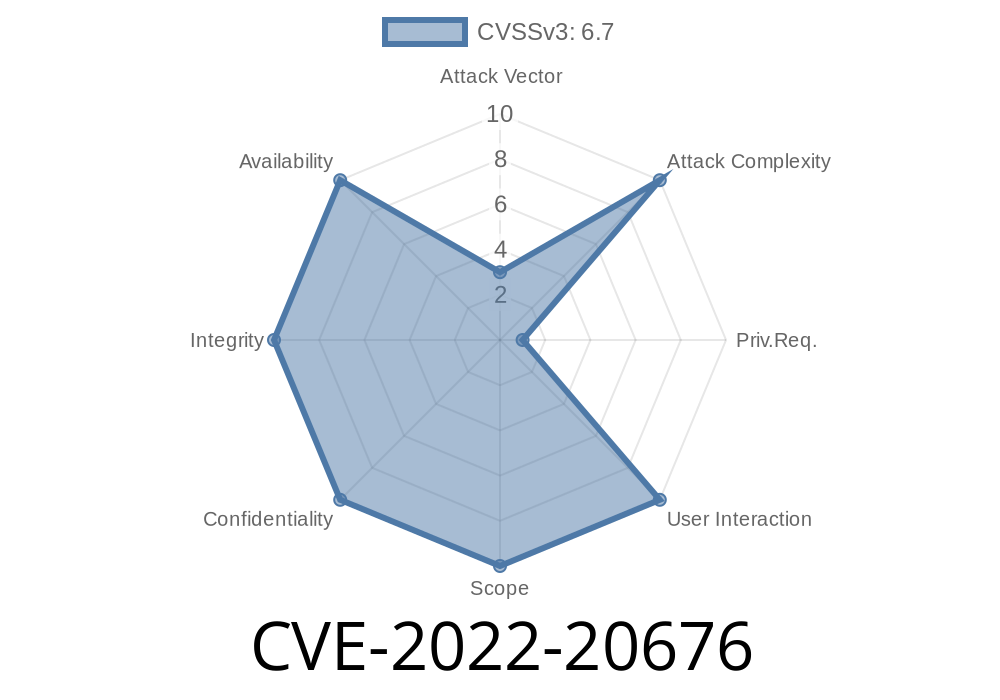
The Tcl VM is a virtual machine that exists in the context of a specific Cisco IOS XE Software process. This can be seen with the show processes command. The process ID (PID) for this virtual machine is 20676, and the memory range available to it is 0-3FFF.
A vulnerability exists where a malicious user could create a Tcl script that exploits the lack of access control on the Tcl VM. This vulnerability would allow an attacker to execute commands from within the virtual machine or access memory space outside the virtual machine.
Discovery
The Cisco IOS XE Software has a vulnerability that could allow an unauthenticated remote attacker to execute arbitrary code with root privileges on the vulnerable device. This is due to the fact that Tcl scripts are run by default from a process with root privileges, but Tcl cannot run in its own VM. Therefore, an unauthenticated remote attacker can exploit this vulnerability and execute code as root on the vulnerable device.
Vulnerable System Characteristics
This vulnerability is only applicable to IOS XE Software and Cisco devices running this software.
CVE-2022-20775
Cisco IOS XE Software allows execution of Tcl scripts from the CLI. When executing a Tcl script, the following occurs: - The script is run by a Tcl interpreter - The script is run within the context of a process - The process runs with the privileges of the user that launched it - The script can only access the memory space of the process that ran it - The script cannot access memory space of the virtual machine that hosts the Tcl VM
A vulnerability in Cisco IOS XE Software could allow an unprivileged local attacker to gain root privileges on systems using this software. This vulnerability occurs because when Cisco IOS XE Software executes a Tcl script from a command line interface (CLI), it creates a new process and runs it with default privileges. In addition, this vulnerability occurs because each time a user logs into any system running Cisco IOS XE Software, they are placed into their own namespace. This allows users to create processes within their own namespace without administrative privileges. An attacker could exploit this issue by creating a new process in which they are placed into their own namespace and then creating another process with administrative privileges. If an attacker uses these privileged processes to modify or replace files located outside of their namespaces, they can elevate privileges to root level.
Timeline
Published on: 04/15/2022 15:15:00 UTC
Last modified on: 04/25/2022 14:09:00 UTC