This vulnerability only exists if the CLI is enabled. The CLI is enabled by default on Cisco devices that contain SD-WAN functionality. The attacker would need to modify the CLI configuration of the device for this vulnerability to be exploited. Cisco devices running SD-WAN Software with the CLI enabled are susceptible to this issue. Cisco devices running Cisco SD-WAN Software with the CLI enabled are vulnerable if the system account is configured with the “system” role. There are several ways for an attacker to exploit this vulnerability. An attacker could exploit this vulnerability by attempting to modify certain files on the vulnerable device. If successful, the attacker could gain escalated privileges and take actions on the system with the privileges of the root user.
Cisco Nexus with Software-Only (WAN) and Software with CLI Enabled,
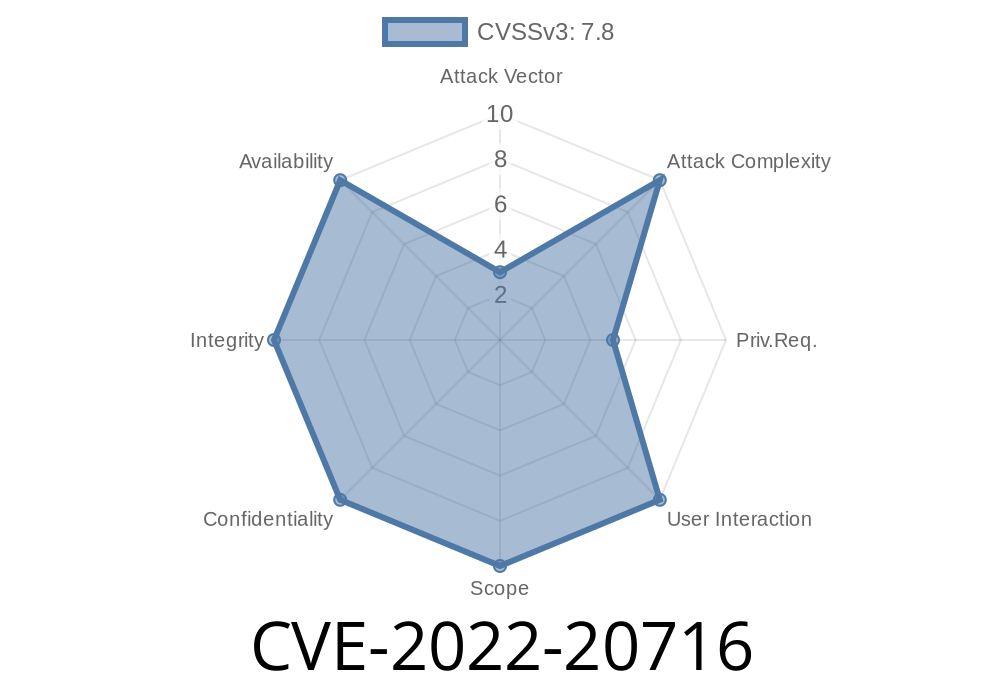
Security Vulnerabilities
Cisco Nexus with Software-Only (WAN) and Software with CLI Enabled, Security Vulnerabilities
This vulnerability only exists if the CLI is enabled. The CLI is enabled by default on Cisco devices that contain SD-WAN functionality. The attacker would need to modify the CLI configuration of the device for this vulnerability to be exploited. Cisco devices running SD-WAN Software with the CLI enabled are susceptible to this issue. Cisco devices running Cisco SD-WAN Software with the CLI enabled are vulnerable if the system account is configured with the “system” role. There are several ways for an attacker to exploit this vulnerability. An attacker could exploit this vulnerability by attempting to modify certain files on the vulnerable device. If successful, the attacker could gain escalated privileges and take actions on the system with the privileges of the root user.
Description of Cisco SD-WAN Software components
Cisco SD-WAN Software is a software suite that provides an end-to-end solution for provisioning and managing network connectivity between Cisco devices and third party clouds. The following components of Cisco SD-WAN Software are affected by this vulnerability:
* SD-WAN interface (Console)
* Cloud management interface
Vulnerable Device Overview
The Cisco SD-WAN software provides the user interface for configuring, provisioning, and monitoring network devices. If the CLI is enabled, an attacker could exploit this vulnerability. The vulnerable device must have been configured with the “system” role to be affected.
Vulnerable Devices and Recommended Actions
Cisco devices running SD-WAN Software with the CLI enabled are susceptible to this issue. Cisco devices running Cisco SD-WAN Software with the CLI enabled are vulnerable if the system account is configured with the “system” role.
The following are recommended actions for mitigating this vulnerability:
1. Disable the CLI on all affected devices by removing the “enable” configuration from /config/config.boot, /config/sys, and /config/user.
2. Upgrade to a software version that contains this vulnerability fix as soon as possible. The Cisco SD-WAN software releases noted in Cisco's advisory at https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/CVE-2022-20716 contain this vulnerability fix.
3. Remove the “system” role from any system accounts across your network by using "passwd -x" or other system account management tools.
Cisco SD-WAN Software
Configuration Error
The Cisco SD-WAN Software Configuration error vulnerability exists in the configuration management application. The vulnerability is caused by a logic error and could be exploited if an attacker sends a specific type of HTTP request to the device. An attacker could exploit this vulnerability by sending a specific type of HTTP request to the device with specially crafted cookies that cause an exception. If successful, the attacker will be able to gain escalated privileges and take actions on the system with the privileges of the root user.
Timeline
Published on: 04/15/2022 15:15:00 UTC
Last modified on: 05/13/2022 17:50:00 UTC