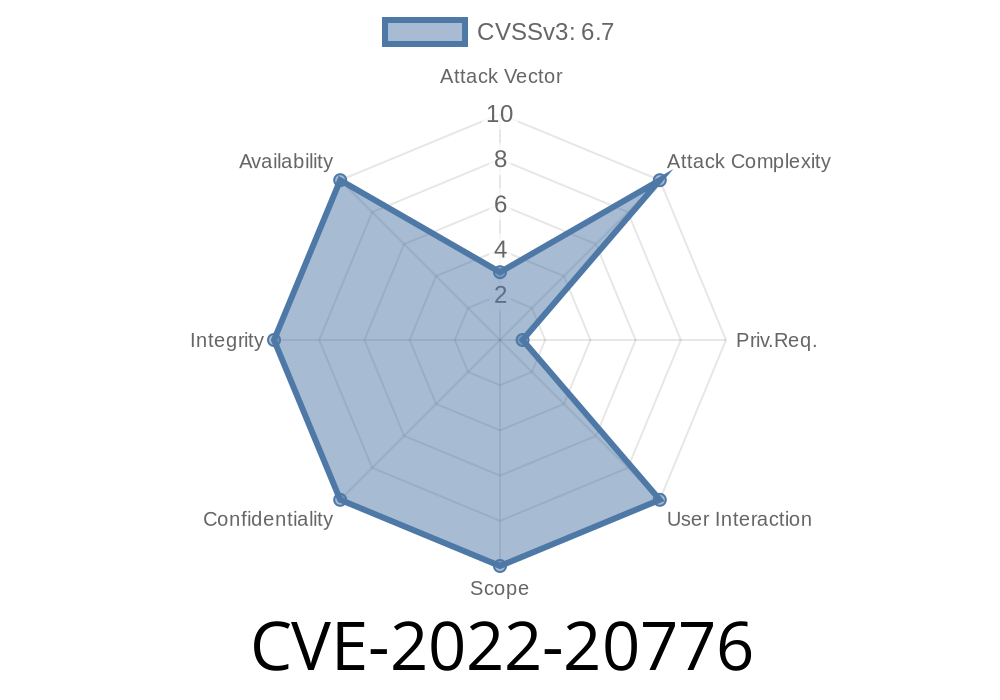
Cisco TelePresence Collaboration Endpoint (CE) Software and Cisco RoomOS Software are widely used for high-quality video conferencing across enterprises. They promise security and ease of use, but in early 2022 researchers uncovered several critical vulnerabilities that could let attackers break through this security, access confidential files, or even upload malicious data to targeted systems. One of the most serious holes is cataloged as CVE-2022-20776.
This exclusive, in-depth post will help you understand the vulnerability, its impact, who it affects, and how a hacker might exploit it — all explained in simple terms with code snippets and technical links for further reading.
What Is CVE-2022-20776?
According to Cisco’s official advisory, multiple vulnerabilities in Cisco TelePresence Collaboration Endpoint (CE) Software and Cisco RoomOS Software allow a remote attacker to:
Write arbitrary files, possibly leading to persistent malicious code installation
The key problem lies in improper input validation when the system processes file requests via specific APIs. An unauthenticated, remote attacker could exploit these gaps to access or modify files on affected devices.
> “An attacker could exploit these vulnerabilities by sending a crafted request to the affected device.”
> —Cisco Security Advisory
Cisco RoomOS Software
For the complete list of affected devices and fixed versions, refer to Cisco’s page:
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-roomendp-path-JEDvHhjb
The Path Traversal Flaw
Web applications and APIs commonly allow users or admins to upload, download, or manage files. Path traversal vulnerabilities occur if the path parameters aren’t properly checked, thereby letting users escape out of the intended directory.
For example, let’s look at a simplified bad code sample in Python which mimics the server-side logic:
from flask import Flask, request, send_file
import os
app = Flask(__name__)
@app.route('/download', methods=['GET'])
def download():
filename = request.args.get('file')
# UNSAFE: does not sanitize file path
file_path = os.path.join("/var/www/resources/", filename)
try:
return send_file(file_path)
except Exception as e:
return str(e), 404
app.run()
If a user sends this GET request:
GET /download?file=../../../etc/passwd
the actual path becomes /var/www/resources/../../../etc/passwd (which resolves to /etc/passwd), possibly letting an attacker read the system's password file.
Cisco’s vulnerability is similar: attackers could craft requests that escape intended directories and reach sensitive configuration, password, or key files.
Crafting the Exploit
Let’s walk through an example, based on public information and common web server behaviors.
1. Locating a Vulnerable Endpoint
First, the attacker probes the device for HTTP endpoints like /api/download?path={filename} or similar, found on TelePresence or RoomOS devices.
Suppose an endpoint /getFile?path=FILENAME exists. An attacker sends
GET /getFile?path=../../../../etc/shadow HTTP/1.1
Host: device.internal
Or, to upload a file via a vulnerable endpoint (say, /uploadFile)
POST /uploadFile HTTP/1.1
Host: device.internal
Content-Type: multipart/form-data; boundary=boundary
--boundary
Content-Disposition: form-data; name="file"; filename="../../../../tmp/exploit.sh"
Content-Type: application/x-sh
echo "pwned" > /tmp/hacked
--boundary--
This could write a new shell script outside the upload directory!
Tamper with device function or brick the system
A compromise of a central video conferencing device could help attackers move deeper into an enterprise network.
How to Fix
Cisco has released updates to patch the flaws.
What YOU should do
- Update to a fixed version (see Advisory Table)
- Disable unneeded HTTP interfaces/firewall unnecessary ports
References & More Information
- Cisco Security Advisory for CVE-2022-20776
- Common Path Traversal Attack Explained
- RoomOS Release Notes and Upgrade Instructions
Final Thoughts
Vulnerabilities like CVE-2022-20776 remind us that even trusted enterprise devices can expose sensitive data if input validation is weak. Anyone running TelePresence CE or RoomOS must keep up with patches and monitor for unusual API access.
Simple coding errors (like failing to clean up file paths) can have wide-reaching consequences — leaving the door open for hackers to walk in.
Stay updated, test often, and review your security policies.
*If you have questions about this vulnerability or want to share your experience patching Cisco CE or RoomOS, leave a comment below!*
Timeline
Published on: 10/26/2022 15:15:00 UTC
Last modified on: 10/31/2022 15:39:00 UTC