Virtualization is supposed to lock things down. It lets us run several virtual machines (VMs) on one piece of hardware, keeping them safely apart. But what happens when that wall between the VM and real host breaks? In late 2022, Cisco’s Enterprise NFV Infrastructure Software (NFVIS) learned this lesson the hard way with CVE-2022-20777—a collection of vulnerabilities that let attackers not only break out of their VM “prison,” but also run code as root and potentially see sensitive data.
Let’s break down why this CVE matters, show how it can be abused, and what to do about it.
What is CVE-2022-20777?
This is an umbrella for several high-severity issues in Cisco’s NFVIS—software popular in network function virtualization. The summary? A malicious user with shell access to a guest VM can escape the virtual machine and interact with the real, underlying host system, potentially gaining full control.
Cisco’s summary:
> Multiple vulnerabilities in Cisco Enterprise NFV Infrastructure Software (NFVIS) could allow an attacker to escape from the guest virtual machine to the host machine, inject commands that execute at the root level, or leak system data from the host to the VM.
Technical Details – How the Exploit Works
The root issue lies in insecure communications and bad isolation between guest and host. Specifically, when a guest VM owner can send crafted data to the host (via certain API calls, filesystem mounts, or device drivers), they can trick the host into running their commands.
Attacker gets shell (command-line) access to a guest VM running on Cisco NFVIS.
2. Attacker uses a crafted command or file to exploit poor isolation and/or command injection in the interface between VM and host.
Here’s a simplified pseudocode sample modeling what went wrong (not production Cisco code)
# Host-side API that listens for VM requests (unsafe version)
def process_vm_input(request):
# bad: command is used directly with shell=True
os.system("sudo " + request.command)
An attacker could send
request.command = "ls; rm -rf /" # result: runs 'ls' then deletes all files!
Or, for a data leak
request.command = "cat /etc/shadow"
In experts’ hands, chaining this with other Linux privilege escalation tricks means the VM user becomes the host’s root user.
Gain Entry: Attacker accesses a VM via SSH (perhaps weak VM user passwords).
2. Upload Payload: Attacker writes a script on VM that abuses the vulnerable “guest tools” or management APIs.
3. Executes Payload: The payload sends a hostile command/request, prompting the host to execute with root powers.
Sample shell snippet from attacker’s VM
#!/bin/bash
# Tries to read /etc/shadow from the host via vulnerable interface
echo 'os.system("cat /etc/shadow")' > /mnt/host_interface/request
The host, due to the bug, executes the command and leaks /etc/shadow back to the attacker’s VM.
Versions: See Cisco’s advisory for exact versions (most before December 2022 patch).
Official Cisco Advisory for CVE-2022-20777
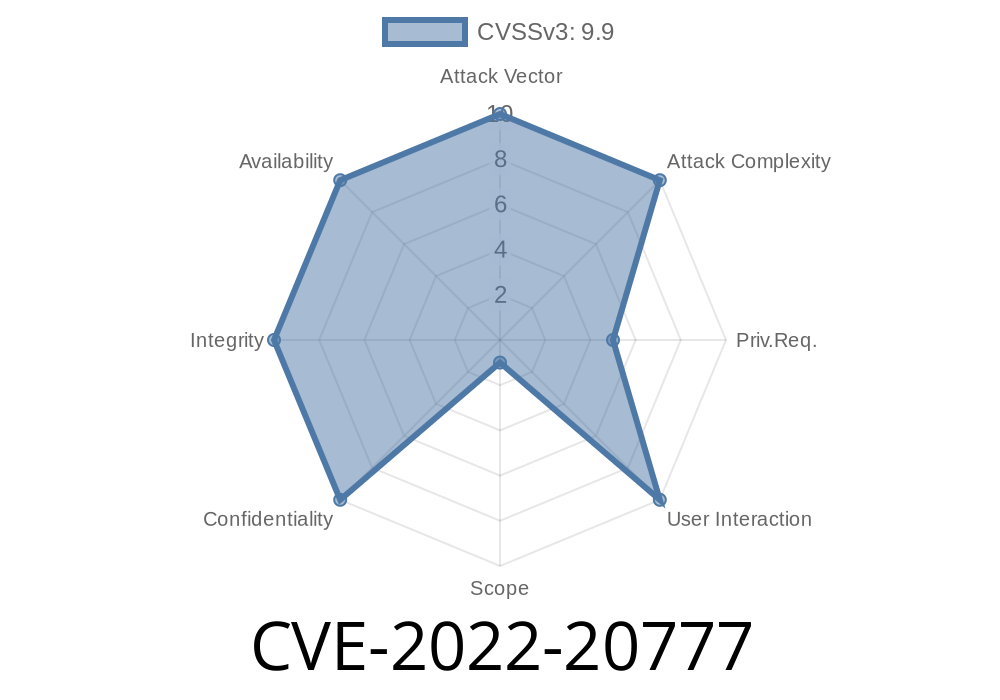
How Bad Is This?
Short version: If you let anyone run code on a guest VM, they may compromise *your entire host*. From there, all other VMs and networks are at risk.
Cisco rates it high severity, given the host escape and root code execution.
How To Fix
1. Patch ASAP:
Cisco released fixes. Update your NFVIS installation!
- Cisco Software Download
2. Restrict Access:
Use strong passwords and network segmentation.
3. Monitor Carefully:
Check for strange commands or user accounts.
4. Follow Cisco’s Best Practices
- Cisco Security Best Practices
More References
- Cisco’s Detailed Advisory: cisco-sa-nfvis-cmdinj-PbA9S7
- CVE Details for CVE-2022-20777
- The Register Coverage
Conclusion
CVE-2022-20777 is a wake-up call: Virtualization isn’t magic. If the software gets isolation wrong—even a little—bad actors can leap out of their “jail” and take over the host system. If you run Cisco NFVIS, patch now, prune unneeded VM access, and keep an eye out—because attackers certainly will.
> If you think your system is exposed, patch immediately and check for strange behavior. Stay safe out there!
Timeline
Published on: 05/04/2022 17:15:00 UTC
Last modified on: 05/11/2022 18:22:00 UTC