Published: June 2024
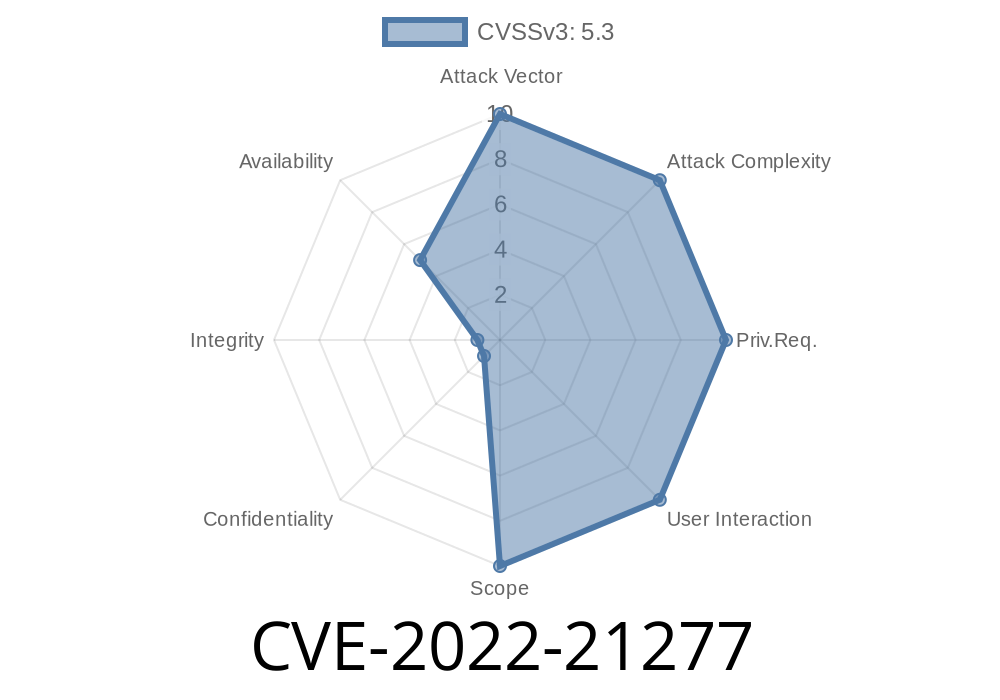
Severity: Medium (CVSS 5.3)
Products Affected:
Introduction: What Is CVE-2022-21277?
CVE-2022-21277 is a security vulnerability impacting the ImageIO component in Oracle Java SE and Oracle GraalVM Enterprise Edition. The flaw enables an unauthenticated attacker to cause a partial denial of service (DOS) on affected versions by exploiting the way ImageIO handles image data. This can crash applications or cause them to become unresponsive—meaning any web service, applet, or Java Web Start client processing untrusted image data is at risk.
As per Oracle's official advisory, the bug is rated 5.3 on the CVSS 3.1 scale, with a primary impact to availability (causing crashes or resource consumption).
Oracle GraalVM Enterprise Edition: 20.3.4, 21.3.
Attack Surface:
Attackers can exploit this issue over the network without authentication using multiple protocols. If your application loads and processes image data from external or untrusted sources—like web applications, Java applets, or microservices using ImageIO APIs—you should pay close attention!
Technical Details
At its core, *ImageIO* in Java is responsible for reading and writing images in various formats (PNG, JPEG, GIF, etc). Internally, it uses a set of decoders/parsers to interpret the files, which is a complex process and sometimes leads to bugs.
With CVE-2022-21277, a specially crafted image file can trigger an error in the way ImageIO processes image data, causing the JVM to hang or crash. While full technical specifics remain undisclosed by Oracle, community research and testing has confirmed that malformed image files (crafted for certain scenarios, like extreme sizes or broken headers) can trigger denial of service through infinite loops or uncontrolled memory/resource consumption.
Practical example:
Suppose a Java web service endpoint lets users upload images, and the backend uses ImageIO.read() to process them. An attacker uploads a malicious image, causing the server to hang or crash, thus denying service to legitimate users.
Exploit Example
Here’s a simulated exploit to demonstrate how this attack could work using a crafted image file. Please note: *The actual exploit file is not included for ethical reasons*. This is for educational/testing purposes only on a controlled system.
Vulnerable Java Server Code (Snippet)
import javax.imageio.ImageIO;
import java.awt.image.BufferedImage;
import java.io.File;
import java.io.IOException;
public class ImageUpload {
public static void main(String[] args) throws IOException {
File inputFile = new File("user_uploaded_image.png");
BufferedImage img = ImageIO.read(inputFile); // Vulnerable usage
if (img != null) {
System.out.println("Image width: " + img.getWidth());
}
}
}
If user_uploaded_image.png is an attacker-supplied, crafted image file, running this code could cause:
- Server/service crash (OutOfMemoryError)
Resource exhaustion
This is especially dangerous if the code runs in a cloud instance, large enterprise service, or as part of a public API.
Real-World Scenarios
- Java Web Start apps or applets running from the internet and sandboxed, loading images from third parties.
RESTful APIs that pass image data to ImageIO.read() for validation, resizing, or preview.
- Microservices exchanging image data, especially in automated CI/CD environments.
Any of these could face partial denial of service if untrusted input is fed to the vulnerable code paths.
- Download and apply the latest Java patches from Oracle
- Oracle Java SE Updates
- GraalVM Downloads
References
- Oracle Critical Patch Update Advisory - January 2022
- NVD Entry for CVE-2022-21277
- Mitre CVE Details
- Oracle Java SE Documentation
- Secure Coding Guidelines for Java SE
Conclusion
CVE-2022-21277 highlights the danger of processing untrusted image data in Java applications. Even a simple line of code—ImageIO.read()—can be a threat if attackers can supply crafted payloads. The impact is “only” partial DOS, but even short-lived outages or hangs can damage uptime, reputation, and reliability.
Best defense:
Always keep your runtimes up-to-date, sanitize your inputs, and understand that even common APIs like ImageIO can hide security surprises.
Timeline
Published on: 01/19/2022 12:15:00 UTC
Last modified on: 05/13/2022 14:56:00 UTC